Enabling Secure Internet Access with ISA Server
Enabling Secure Internet Access with ISA Server. Enabling Secure Access to Internet Resources. What Is Secure Access to Internet Resources ? Users can access the resources that they need The connection to the Internet is secure The data that users transfer to and from the Internet is secure

Enabling Secure Internet Access with ISA Server
E N D
Presentation Transcript
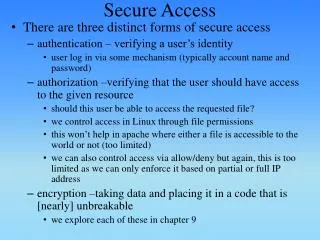
Enabling Secure Access to Internet Resources • What Is Secure Access to Internet Resources? • Users can access the resources that they need • The connection to the Internet is secure • The data that users transfer to and from the Internet is secure • Users cannot download malicious programs from the Internet • Secure access to the Internet also means that the user’s actions comply with theorganization’ssecurity or Internet usage policy.
What Is Secure Access to Internet Resources • Secure access: • Only users who have permission to access the Internet can access the Internet. • These users can use only approved protocols and applications to access Internetresources. • These users can gain access only to approved Internet resources, or these userscannot gain access to denied Internet resources • These users can gain access to the Internet only in accordance with any other restrictions • the organization may establish, such as when and from which computers accessis permitted.
How ISA Server Enables Secure Access to Internet Resources • ISA Server provides the following functionality to enable secure access • Implementing ISA Server as a firewall • Implementing ISA Server as a proxy server. • Using ISA Server to implement the organization’s Internet usage policy
Configuring ISA Server as a Proxy Server • What Is a Proxy Server? • A proxy server is a server that is situated between a client applicationand a server to which the client connects. • All clientrequests are sent to the proxy server. The proxy server creates a new request and sendsthe request to the specified server. The server response is sent back to the proxy server,which then replies to the client application. • A proxy server can provide enhancedsecurity and performance for Internet connections. • Using a proxy server is to make the user’s connection tothe Internet more secure.
Configuring ISA Server as a Proxy Server • Proxy servers make the Internet connection more secure inthe following ways: • User authentication • Filtering client requests • Content inspection • Logging user access • Hiding the internal network details
How Proxy Servers Work • How Does a Forward Proxy Server Work? • How Does a Reverse Web Proxy Server Work?
How Does a Forward Proxy Server Work? • When a proxy server is used to secure outbound Internet access, it is configured as aforwarding proxy server. • Forward proxy servers are usually located between a Web or Winsock application runningon a client computer on the internal network and an application server located onthe Internet
1. A client application, such as a Web browser, makes a request for an object locatedon a Web server. The client application checks its Web proxy configuration to determine whether the request destination is on the local network or on an externalnetwork. 2. If the requested Web server is not on the local network, the request is sent to theproxy server. 3. The proxy server checks the request to confirm that there is no policy in place thatblocks access to the requested content. 4. If caching is enabled, the proxy server also checks if the requested object exists inits local cache. If the object is stored in the local cache and it is current, the proxyserver sends the object to the client from the cache. If the page is not in the cacheor if the page is out of date, the proxy server sends the request to the appropriate server on the Internet.
5.The Web server response is sent back to the proxy server. The proxy server filtersthe response based on the filtering rules configured on the server. 6. If the content is not blocked and it is cacheable, ISA Server saves a copy of thecontent in its cache and the object is then returned to the client application thatmade the original request.
A user on the Internet makes a request for an object located on a Web server thatis on an internal network protected by a reverse proxy server. The client computerperforms a DNS lookup using the fully qualified domain name (FQDN) of thehosting server. The DNS name will resolve to the IP address of the external networkinterface on the proxy server. 2. The client application sends the request for the object to the external address ofthe proxy server
3.The proxy server checks the request to confirm that the URL is valid and to ensure that there is a policy in place that allows access to the requested content. 4. The proxy server also checks whether the requested object already exists in itslocal cache. If the object is stored in the local cache and it is current, the proxyserver sends the object to the client from the cache. If the object is not in thecache, the proxy server sends the request to the appropriate server on the internalnetwork. 5. The Web server response is sent back to the proxy server. 6. The object is returned to the client application that made the original request
How to Configure Web and Firewall Chaining • ISA Server 2004 Standard Edition supports the chaining of multiple servers running ISAServer together to provide flexible Web proxy services
Configuring Access Rule Elements • By default, ISA Server 2004 denies all network traffic between networks connected tothe ISA Server computer. • Configuring an access rule is the only way to configure ISAServer so that it will allow traffic to flow between networks
What Are Access Rule Elements • Access rule elements are configuration objects in ISA Server that you use to createaccess rules. • Example:you may want to create an access rule that allows onlyHTTP traffic, ISA Server provides an HTTP protocol access rule element thatyou can use when creating the access rule
How to Configure Access Rule Elements • ISA Server includes several default access rule elements
How to Configure User Set Elements • access rule specifies whichusers will be allowed or denied access by the access rule. • To limit access to Internetresources based on users or groups, you must create a user set element. • When youlimit an access rule to specific users, users must authenticate before they are grantedaccess. • For each group of users, you can define the type of authentication required
How to Configure User Set Elements • All Authenticated Users:This set includes all users who have authenticatedusing any type of authentication. • All Users:This set includes all users, both authenticated and unauthenticated. • System and Network Service:This user set includes the Local System serviceand the Network service on the computer running ISA Server. This user set is usedin some system policy rules
How to Configure User Set Elements • In ISA Server
How to Configure Content Type Elements • Create a new content type element, or use one of the existing content typeelements when you create an access rule. • Content type elements define MultipurposeInternet Mail Extensions (MIME) types and file name extensions. • When a client such asMicrosoft Internet Explorer downloads information from the Internet using HTTP orFile Transfer Protocol (FTP), the content is downloaded in either MIME format or as afile with a specified file name extension.
How to Configure Content Type Elements • Content type elements apply only to HTTP and FTP traffic that is tunneled in an HTTPheader. • When a client requests HTTP content, ISA Server sends the request to the Webserver. • When the Web server returns the object, ISA Server checks the object’s MIMEtype or its file name extension, depending on the header information returned by theWeb server. • ISA Server determines if a rule applies to a content type that includes therequested filename extension, and processes the rule accordingly • ISA Server is preconfigured with the following content types: Application, Applicationdata files, Audio, Compressed files, Documents, Hypertext Markup Language (HTML)documents, Images, Macro documents, Text, Video, and Virtual Reality ModelingLanguage (VRML).
How to Configure Schedule Elements • To configure access to the Internet based on the timeof day. • ISA Server : • Weekends:Defines a schedule that includes all times on Saturday and Sunday • Work Hours:Defines a schedule that includes the hours between 09:00 (9:00 A.M.)and 17:00 (5:00 P.M.) on Monday through Friday
How to Configure Network Objects • to define which Web sites or servers users can or cannot access • Networks: • A network rule element represents anetwork, which is all the computersconnected • EX:Internal, External, Branch Office • Network Sets: • A network-set rule element representsa grouping of one or more networks • Ex:All Protected Networks
How to Configure Network Objects • Computer: • A computer rule element represents asingle computer, identified by its IPaddress • Ex:DC1 (IP Address: 192.168.1.10). • Address Ranges: • An address range is a set of computersrepresented by a continuousrange of IP addresses • Ex:All DCs (IP Address Range:192.168.1.10 – 192.168.1.20).
How to Configure Network Objects • Subnets: • A subnet represents a network subnet,specified by a network addressand a mask. • Ex:Branch Office Network (IPAddresses 192.168.2.0/24). • Computer Sets: • A computer set includes a collectionof computers identified by their IPaddresses, a subnet object, or anaddress-range object • Ex:All DCs and Exchange Servers
How to Configure Network Objects • URL Sets: • URL sets specify one or more URLsgrouped together to form a set. • Ex:Microsoft Web Site (http://www.microsoft.com/*) • Domain Name Sets: • Domain name sets define one ormore domain names as a single set,so that you can apply access rules tothe specified domains
How to Configure Network Objects • In ISA server
Configuring ISA Server Authentication • to limit access to Internet resources based on users or groups • ISA Server Authentication Options: • Basic authentication: • Basic authentication sends and receives user information as plaintext and does not use encryption • Digest authentication: • Digest authentication passes authentication credentialsthrough a process called hashing. • Hashing creates a string of characters based onthe password but does not send the actual password across the network, ensuringthat no one can capture a network packet containing the password and impersonatethe user.
Integrated Windows authentication: • Uses either the Kerberos version 5authentication protocol or NTLM protocol, both of which do not send the username and password across the network. • Digital certificates authentication: • Requests a client certificate from the clientbefore allowing the request to be processed. • Users obtain client certificates from acertification authority that can be internal to your organization or a trusted externalorganization. • Remote Authentication Dial-In User Service • RADIUS is an industry-standardauthentication protocol.
ISA Server Clients and Authentication • SecureNAT Clients: • For SecureNAT clients, there is no user-based authentication • Restrict access to the Internet based only on network rules and other access rules • If an access rule requires authentication, SecureNAT clients will be blocked fromaccessing the resources defined by the rule
Firewall Clients • When ISA Server authenticates a Firewall client, it uses the credentialsof the user making the request on the computer running the Firewall client
Configuring Access Rules for Internet Access • What Are Access Rules