563.12.1 Automated Identification
200 likes | 462 Views
563.12.1 Automated Identification. Anh Nguyen University of Illinois Fall 2007. Agenda. Identification Automated Identification Applications Technologies Patient Identification My research project. 1. Identification.

563.12.1 Automated Identification
E N D
Presentation Transcript
563.12.1 Automated Identification Anh Nguyen University of Illinois Fall 2007
Agenda • Identification • Automated Identification • Applications • Technologies • Patient Identification • My research project
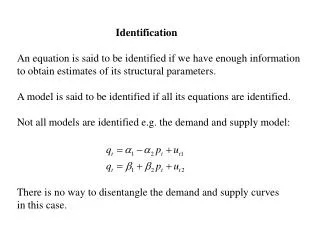
1. Identification • “The function of identificationis to map a known quantity to an unknown entity so as to make it known. The known quantity is called the identifier (or ID) and the unknown entity is what needs identification...” – Wiki • No guarantee of provenance or right mapping.
Need and concern • Why Identification: • In many cases it is a required part of the workflow. • Build up profile (better shopping experience). • In security: • Authorization = Identification & Authentication + Assigning Privilege(s).(Identity Crisis: How Identification Is Overused and Misunderstood - Jim Harper - debate at Techliberation) • Security concerns according to CIA model: • Confidentiality: Might not want outside parties to learn your ID (SSN) • Integrity: of ID transferred. • Availability: the ID is ready when needed.
2. Automated Identification (AID) • The process is done automatically, less human interventions. • To save times, increase productivity • To operate in harsh environment where it is harmful for human • Either replace traditional identification procedure to provide more seamless workflow, or bring new applications: • Commercial: Product identification, Supply chain & Logistics, E-Commerce. • Healthcare: Equipment tracking/ Patient Identification (later) • Transportation: E-Tickets • Others: Animal Tracking, Vehicle / People Identification
AID Applications - Domino • Microsoft touch screen computing & domino technology http://www.news.com/1606-2-6186146.html
AID Technologies - Barcode • Printing ID in a way which is machine readable. Information can be expressed via different symbologies. • History: developed in 1948, commercial use 1966, not commercially successful until the 1980s. • Recent developments: 2D Barcode / stacked barcode, Semacode. • Characteristics: cheap, short/long operating range, line of sight, low data rate. • Current uses: Groceries – UPC, Books – ISBN, drugs Barcode, Semacode, UPC, ISBN – Wikipedia
Magnetic Stripe Card • Storing data by modifying the magnetism of tiny iron-based magnetic particles on a band of magnetic material, as in video tape. • Sticking a piece of magnetic tape to a plastic card base. • Characteristics: cheap, higher data rate, near operating range, inconvenient (operation + reliability), low coercivity card easily damaged. • Highly standardized. • Current uses: ID cards (UID), Credit & Debit Cards, Subway and Bus Card.
Smart Card • Adding processing power: any pocket-sized card with embedded integrated circuits which can process information. • Contact, contactless. Contactless and RFID. • Characteristics: has processing power, often come with tamper resistant feature, short operating range (ISO 14443 – 10cm, ISO 15693 – 50cm), more expensive. • Current uses: Mobile phone SIM, ATM Cards, contactless CC/DC, smart driver licenses. RFID Vs Contactless Smart cards – An unending debate - Parul Oswal – 2006
Biometrics • Uniquely recognizing humans based upon one or more intrinsic physical or behavioral traits. (but must be unique) • Characteristics: convenient / inconvenient, not very reliable (collision, effect of aging), usually more expensive. • Current uses: Personal laptops, digital IDs, ePassport (US, Brazil, Germany). • Concerns: once compromised it is compromised for life, danger to owner. Biometrics - Wikipedia
RFID • Using radio frequency to transfer identifier. • Characteristics: very flexible (HF/LF/UHF, active/passive, implantable..), convenient, does not require line of sight. • Concerns: privacy, cancer (implantable tags). • Emerging market: DoD and Wal-Mart’s mandate, Prescription Drug Marketing Act (PMDA) - pharmaceutical supply chain (pedigree system by Dec 2006 – FDA), China national ID card, Qatar National Identification Project...
3. Patient Identification • Current practice • Use text/color wristband • Use barcode wristband (ex: University of Wisconsin Hospital – 2004) • Use RFID wristband (ex: Bangkok Hospital – 2006, Birmingham Heartlands Hospital - 2007)
Need to Improve • Patient misidentification is identified as a root cause of many errors: adverse drugs event, wrong invasive surgical operations... • Study by FDA shows that adverse drug events (ADEs) range from 2.4 percent to 6.5 percent per facility, with a mean rate of 4.3 percent – about 770,000 adverse events in the U.S. each year, $1.7 billion cost – Zebra white paper. • Joint Commission – JCAHO - listed “improving patient identification accuracy” as the first of its National Patient Safety Goals introduced in 2003, and this continues to be an accreditation requirement from 2004 to 2008. • WHO and JCAHO encourage the use of at least two identifiers. (*3) The Wrong Patient - Mark R. Chassin – 2002, Patient Identification - WHO Press - 2007
Applications • Combine it with automated medication administration systems. U of Wisconsin Hospital reduced medication administration error by 87%. • Blood Administration • Sample / Treatment Management (to prevent unnecessary procedures) • Automated Billing • Patient tracking (babies, sleepwalker)
Technology Trade-off • Regulations (FDA, FCC compliance; EU Directive – CE mark) • Reliability • Privacy concerns • Convenience. • Cost for hospital. • Cost for patient. (not a big issue) • (*4)
Barcode, Magnetic Stripe, Smart Card • Barcode: • Advantage: conform to regulation, proven reliability, cheap • Disadvantage: inconvenient, limited applications, low capacity, not re-writable. • Magnetic Stripe • Advantage: conform to regulation, acceptable reliability, cheap, higher capacity. • Disadvantage: inconvenient, limited applications, not easily re-writable • Smart card • Advantage: conform to regulation, high reliability, high capacity, flexible (contact/contactless, rewritable/not), computation & security features. • Disadvantage: more expensive, limited applications (range).
RFID, Biometrics • RFID • Advantage: higher capacity, more applications, convenient, flexible (long/short range, re-writable/not, passive/active) • Disadvantage: regulation conformation, reliability (metal & liquid), privacy concerns (more engineering researches), more expensive. • Biometrics • Advantage: conform to regulation, convenient, no extra cost for patient. • Disadvantage: limited applications, no extra information, most expensive (for hospital), reliability improvement. http://www.pdcorp.com/healthcare/case-study-chang-gung-hospital.html
My research • Working with Ayesha: • “To design, implement and verify a system that will enable clinicians to gather, verify and store medical device reading in an automated fashion” Medical Device reading (Nurse ID, Patient ID, reading) Ser-ver Patient ID Nurse info, patient info, human readable reading (*) Yes/ No Patient (*) Yes/No Nurse ID Nurse https://agora.cs.uiuc.edu/display/cs598cag/Automated+Medical+Data+Acquisition
Conclusion • Automated Identification is very useful. • RFID is an emerging technology. • Patient Identification need to be improved. And could be done using AID. • Each AID technology has its own advantage and disadvantage. • More researches to prove/improve reliability of RFID and Biometrics, design so that RFID will conform with EMC requirements.
References • Identity Crisis: How Identification Is Overused and Misunderstood - Jim Harper - 2006 • www.rfidjournal.com • www.rfidupdate.com • Patient Identification - Patient Safety Solutions - volume 1, solution 2, May 2007 - WHO Press • Patient identification - a crucial aspect of patient safety - patient Safety First • The Wrong Patient - Mark R. Chassin, MD, MPP, MPH, and Elise C. Becher, MD, MA* - 4 June 2002 | Volume 136 Issue 11 | 826-833 • It's All in the Wrist: Improving Patient Safety with Bar Code Wristbands – Zebra – 2006 • A wearable device for a fully automated in-hospital staff and patient identification - M. Cavalleri, R. Morstabilini, G. Reni – 2004 • Interoperability Issues regarding Patient Identification in Europe - C. Quantin et al - IEEE EMBS - 2007