The Internet and Security
Learn about the history of the internet, telecommunications, and how the TCP/IP protocols work. Explore web addresses, domains, and connecting to the internet. Discover information system security measures such as risk assessment, access control, and disaster recovery plans.

The Internet and Security
E N D
Presentation Transcript
The Internet and Security Chapter 4
Key Terms Telecommunications Transmission of all forms of communication including digital data, voice, fax, sound, and video from one location to another over some type of network Networks A group of computers and peripheral devices connected by a communication channel capable of sharing information and other resources among users Bandwidth Is the carrying capacity of a telecommunications network. (i.e. the size of the telecommunications channel or pipeline)
Email with teeth Sample of Interpersonal Use of Telecommunications
Warriors History of the Internet • ARPANET 1960 (Advanced Research Project Agency Network) • NSFNET1986(National Science Foundation Network) • Connected to ARPANET and many others (BITNET, CSNET, etc) to become a major component of the Internet • Internet Support • Ongoing support comes from many universities, federal and state governments, and national international research institutions and industry
How the Internet Works – TCP/IP & Routers TCP/IP Approach TCP – Transmission Control Protocol IP – Internet Protocol • Routers • Connect one network to another • Identify each device on a network as unique using IP protocol • Serve as the “Traffic Cop” directing packets to their destination
How the Internet Works – Web Addresses & Domains • Domain • Identifies the Website (host) • Comes in many suffixes such as: • .edu (educational institutions) • .org (organizations; non-profit) • .mil (military) • .net (network organizations) • Example: microsoft.com • IP Address • Each domain is associated with one or more IP addresses • Format: a 32-bit address written as 4 numbers (from 0-255) separated by periods • Example: 1.160.10.240 • (URL) Uniform Resource Locator • Identifies particular Web pages within a domain • Example: http://www.microsoft.com/security/default.mspx
How the Internet Works – Connecting to the Internet Modem (stands for Modulate/Demodulate) Internet Service Provider (ISP) Network Access Points (NAPs) Internet Backbone
Network Connection Types POTS (Plain Old Telephone Service) ISDN (Integrated Services Digital Network) DSL (Digital Subscriber Line) Cable Modem IoS (Internet over Satellite) • Wireless • Fixedwireless • Mobilewireless
World Wide Web • HTTP (Hypertext Transfer Protocol) • A protocol used to process user requests for displaying Web pages from a Web server • Web Servers • A special computer that is specifically designed to store and “serve up” Web pages • This machine contains special hardware and software to perform its many specialized functions
Information System Security IS Security Precautions taken to keep all aspects of information systems safe from unauthorized access • Managerial Methods • Several techniques are commonly used to manage information systems security: • Risk Assessment • Controlling Access • Organizational Policies and Procedures • Backups and Recovery
Information System Security – Managerial Techniques • Assessing Risk • Security Audit • Risk Analysis • Alternatives based on Risk Analysis: • Risk Reduction • Risk Acceptance • Risk Transference – • Controlling Access • Keeping information safe by only allowing access to those that require it to do their jobs • Authentication – • Access Control –
Information System Security – Managerial Techniques • Organizational Policies and Procedures • Acceptable Use Policies – formally document how systems should be used, for what, and penalties for non-compliance • Backups and Disaster Recovery • Backups – taking periodic snapshots of critical systems data and storing in a safe place or system (e.g. backup tape) • Disaster Recovery Plans – spell out detailed procedures to be used by the organization to restore access to critical business systems (e.g. viruses or fire) • Disaster Recovery – executing Disaster Recovery procedures using backups to restore the system to the last backup if it was totally lost
Identity theft State of IS Security - Security Threats & Technologies • Security Threats • Identity Theft – • Denial of Service – • Others: Spyware, Spam, Wireless Access, Viruses • Security Technologies • Companies and research organizations continue to develop and refine technologies to prevent security breaches. Some Include: • Firewalls • Biometrics • VPN and Encryption
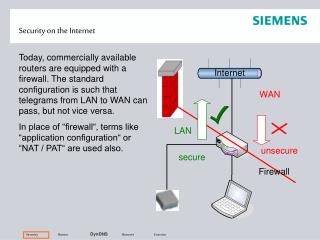
IS Security: Technology Firewalls A system of software, hardware or both designed to detect intrusion and prevent unauthorized access to or from a private network
Firewall Capability Firewall can • Focus for security decisions • Enforce security policy • Log internet activity • Limit exposure • keeps one section of intranet separate from another Firewall can not • Protect against malicious insiders • Protect against connections that do not go through it • Protect against new threats • Protect against viruses
Biometrics Security Technology: Biometrics • Biometrics • A sophisticated authentication technique used to restrict access to systems, data and/or facilities • Uses biological characteristics to identify individuals such as fingerprints, retinal patterns in the eye, etc. that are not easily counterfeited
Security Threat: Access to Wireless • Unauthorized Access to Wireless Networks • With the prevalence in use of wireless networks this threat is increasing • Problems - Drive-by hacking - an attacker accesses the network, intercepts data from it, and can use network services and/or send attack instructions without entering the building • Prevention - Encryption between network and user devices
On 8 February, 1587 Elizabeth I of England signed Mary's death warrant, and she was executed at Fotheringay Castle. The execution did not go well for Mary as the executioner was unable to sever her neck with one blow, and was forced to use a grinding motion on her to complete the task. All because of weak encryption.
Security Technology: VPN and Encryption • Encryption • The process of encoding messages before they enter the network or airwaves, and then decoding at the receiving end • Public Key - known and used to scramble messages (SSL) • Private Key - not known and used by receiver to descramble • Certificate Authority – a third party that issues keys
Virtual private network • Virtual private network (VPN): a secure connection between two points across the Internet • Tunneling: the process by which VPNs transfer information • by encapsulating traffic in IP packets over the Internet