FILE SYSTEM
FILE SYSTEM. Introduction. File System is a mechanism which is provided by the operating system to store and retrieve files on the disk. This system is primarily responsible for the management and organization of various files in a system. File Concept.

FILE SYSTEM
E N D
Presentation Transcript
Introduction File System is a mechanism which is provided by the operating system to store and retrieve files on the disk. This system is primarily responsible for the management and organization of various files in a system.
File Concept A file is a collection of related data stored as a named unit on the secondary storage. It can store different types of data, like text, graphics, database, executable code, sound, videos, etc and on the basis of the data, a file can be categorized as a data file, graphic file, database file, executable file, sound file, video file, etc.
File Attributes A file in a system is identified by its name. The file name helps a user to locate a specific file in the system. Different operating systems follow different file naming conventions. File attributes help the file system to manage a file within the system. Files attributes may vary in different operating system.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection Helps to identify and locate a file in the system.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection Stores information about the current size of the file.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection Helps the operating system to recognize and use the recommended program to open a particular file type.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection A unique tag, usually a number that helps the file system to recognize the file within the file system.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection A pointer that stores location information of the device and location of the file on that device.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection Stores information such as date and time of creation, last modification and last use. This is useful for protection, security and monitoring.
File Attributes • Name • Size • Type • Identifier • Location • Date and Time • Protection Stores information about the access permissions (read, write, execute) of different users.
File Operations • File operations are the functions that can be performed on a file. Operating system handles the file operations through the use of system calls. Various operations that can be performed on a file are: • Create a file • Open a file • Write to a file • Read a file
File Operations • Seek file • Close file • Delete file • Append file • Rename file
File Operations • File operations are the functions that can be performed on a file. Operating system handles the file operations through the use of system calls. Various operations that can be performed on a file are: • Create a file • Open a file • Write to a file • Read a file “create” system call is used to create a file. When this system call is used, the operating system searches for the free space in the file system and allocates it to the file. In addition, the OS makes a directory entry to record the name, location and other information about the file.
File Operations • File operations are the functions that can be performed on a file. Operating system handles the file operations through the use of system calls. Various operations that can be performed on a file are: • Create a file • Open a file • Write to a file • Read a file “open” system call accepts the file name and the access-mode as parameters to open a file and returns a pointer to the entry in the open-file table. The OS searches the directory entry for the file name and also checks the access permission.
File Operations • File operations are the functions that can be performed on a file. Operating system handles the file operations through the use of system calls. Various operations that can be performed on a file are: • Create a file • Open a file • Write to a file • Read a file “write” system call accepts the file name and the data to be written to the file as parameters. The OS searches the directory entry to locate the file and writes data to the specified position in the file and also updates the write pointer to the location where next write operation is to take place.
File Operations • File operations are the functions that can be performed on a file. Operating system handles the file operations through the use of system calls. Various operations that can be performed on a file are: • Create a file • Open a file • Write to a file • Read a file “read” system call accepts the file name, amount of data to be read and a read pointer to point to the position from where the data is to be read as parameters. The current position pointer will be updated after the read operation.
File Operations • Seek file • Close file • Delete file • Append file • Rename file “seek” system call is used to position the pointer to a specific position in a file. Once the pointer is positioned, data can be read from and written to that position.
File Operations • Seek file • Close file • Delete file • Append file • Rename file “close” system call is used to close a file, when all the operations on that file are completed. The OS erase the file entry from the open-file table to make space for the new file entries.
File Operations • Seek file • Close file • Delete file • Append file • Rename file “delete” system call is used to delete a file, when a file is not required. The OS will erase its corresponding directory entry also.
File Operations • Seek file • Close file • Delete file • Append file • Rename file “append” system call is used to add data at the end of an existing file. The system call works similar to the “write” system call, except that it positions the pointer to the end of the file and then performs the write operation.
File Operations • Seek file • Close file • Delete file • Append file • Rename file “rename” system call is used to change the name of an existing file. The OS changes the directory entry also.
File Types The most common technique to implement file type is by providing extension to a file. The file name is divided into two parts separated by a period, where the first part is the name and the second part after the period is the file extension. A file extension is generally one to three characters long. The extension indicates the type of the file and the operations (read, write, execute) that can be performed on that file.
Access Methods • The information stored in the file can be accessed as follows: • Sequential Access • Direct Access
Access Methods • The information stored in the file can be accessed as follows: • Sequential Access • Direct Access Information from the file is accessed in order, one record after the other. Compilers, multimedia applications, sound files, etc. are the most common examples of programs using sequential access. In case of a read operation, the record at the location pointed by the file pointer is read and the file pointer is then advanced to the next record. In case of write operation, the record is written to the end of the file and pointer is advanced to end of new record.
Access Methods • The information stored in the file can be accessed as follows: • Sequential Access • Direct Access Under direct access, a file is viewed as a sequence of blocks (or records) which are numbered. The records of a file can be read or written in any order using this number. The block number is relative to the beginning of the file. This relative number internally has an actual absolute disk address and this mapped by the file system. In direct access, the system calls for read and write operations are using the block number as parameter.
Directory Structure To manage the data stored on a disk, the disk is divided into one more partitions also known as volumes and each partition contains information about the files in it. This information is stored in directory.
Operations Performed on Directory • Search for a file • Create a file • Delete a file • List a directory • Rename a file • Traverse the file system • It is possible to have more than one operating system on a single disk, where a user can boot any of the operating system.
Organize the Directory (Logically) to Obtain • Efficiency – locating a file quickly • Naming – convenient to users • Two users can have same name for different files • Grouping – logical grouping of files by properties, (e.g., all Java programs, all games, …)
Single-Level Directory • A single directory for all users Naming problem – No two files can have the same name. Grouping problem – Only one directory is available for all users.
Two-Level Directory • Separate directory for each user (MFD, UFD) • Path name • Can have the same file name for different user • Efficient searching • No grouping capability
Protection The information stored in a system requires to be protected from the physical damage and unauthorized access. A file system can be damaged due to various reasons such as, a system breakdown, theft, fire, lightning or any other nature calamities.
Protection When the physical damage is irreversible, the data can be lost permanently. Physical damage to a system is unavoidable, we must take proper measures to safeguard and protect the data. Protection can be provided by storing a copy of information on the disk to the disk itself, or to some other removable storage media.
Protection Apart, from protecting the file from physical damage, the file in a system also needs a protection mechanism to control improper access. In a multi-user system, one user can access files of other users, and the system is prone to improper access. A protection mechanism is necessary in such a situation.
Types of Access Different access rights that can be assigned to a particular user for a particular file are: • Read – Allow only reading the file. • Write – Allow write or rewriting the file. • Execute – Allow running the program or application. • Append – Allow writing new information at the end of file. • Copy – Allow creating a new copy of the file. • Rename – Allow renaming a file. • Edit – Allow adding or deleting information from the file. • Delete – Allow deleting the file and releasing the space.
Access Control Access control is to protect the file from improper accesses. • Password • Access Control List (ACL) To resolve the problems associated with ACL, the users can be categorized as: • Owner • Group • Universe
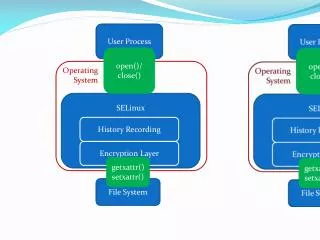
File System Structure File system helps to organize, manage and retrieve data on the disk. The file system resides permanently on the disk. Two key issues in the design of file system: • Defining a file and attributes, operations that can be performed on a file and the directory structure. • Creating data structures and algorithms for mapping the logical file system into the secondary storage device.