Tracking
Tracking. Murat Demirbas SUNY Buffalo. A Pursuer-Evader Game for Sensor Networks. Murat Demirbas Anish Arora Mohamed Gouda. Pursuer-evader problem. Evader is omniscient; Strategy of evader is unknown

Tracking
E N D
Presentation Transcript
Tracking Murat Demirbas SUNY Buffalo
A Pursuer-Evader Game for Sensor Networks Murat Demirbas Anish Arora Mohamed Gouda
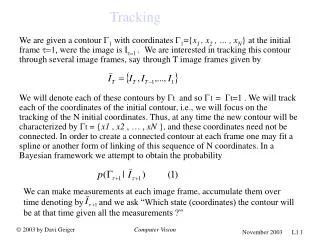
Pursuer-evader problem • Evader is omniscient; Strategy of evader is unknown • Pursuer can only see state of nearest node; Pursuer moves faster than evader ( ratio = f ) • Required is to design a program for nodes and pursuer so that pursuer can catch evader (despite the occurrence of faults)
Model • Connected graph of sensor nodes • Transient faults; connectivity still maintained • Maximal parallelism in node actions
Two approaches • Evader-centric program • move is costly, find is for free • sensor nodes communicate periodically with neighbors • stabilizes and tracks faster • Pursuer-centric program • find is costly, move is for free • sensor nodes communicate with neighbors only upon request • minimizes number of messages and energy efficient • Hybrid program • find & move are both tunable
Outline • Evader-centric program • Pursuer-centric program • Hybrid program • Extensions
Evader-centric program • Nodes collectively maintain a tracking tree • ts.j : latest timestamp that j knows about detection of evader • p.j: parent of j in tree • d.j : distance of j from evader • root is the node where the evader resides {Evader resides at j} ---> p.j := j; ts.j :=clock.j; d.j :=0 • every node sets its parent to be the nbr with maximum ts ts.k > ts.j ---> p.j :=k ; ts.j := ts.(p.j); d.j:= d.(p.j)+1 • Find is for free: pursuer follows the tracking tree to its root
Evader-centric program (cont.) • Tracking tree is dynamically rooted at the evader • Parent of a node is closer to the evader
Evader-centric program (cont.) • Tracking tree is dynamically rooted at the evader • Parent of a node is closer to the evader
Evader-centric program (cont.) • Tracking tree is dynamically rooted at the evader • Parent of a node is closer to the evader
Evader-centric program (proof of stabilization) • Tracking tree is rooted at the evader within D steps • soft-state stabilization • The distance between pursuer and evader does not increase once the constructed tree includes the pursuer • Starting from an arbitrary state pursuer catches evader in at most D+ 2D * f/(1-f) steps
Pursuer-centric program • Move is for free: ts.j is maintained locally {evader detected at j} ---> ts.j := clock.j • Nodes communicate with nbrs only at the request of pursuer; pursuer is directed to nbring node with highest recorded time {pursuer detected at j} ---> next.j :in {k | ts.k= max ts.nbr.j }; ts.j :=0 • Pursuer action is to move to next.j • pursuer does a random walk until it reaches a node that evader has visited
Pursuer-centric program (cont.) • If the pursuer reaches a node j with ts.j>0, pursuer catches evader within N*f/(1-f) steps
Pursuer-centric program (stabilization) • Since ts.j is reset to 0 when pursuer visits j, bad values disappear • From random walk result, pursuer reaches a node j, ts.j >0 , within O( N2 * log N ) steps • Then, pursuer catches evader within N*f/(1-f) steps
Hybrid program Tracking tree is bounded to a depth R Pursuer-centric program is executed at nodes outside tracking tree
Hybrid program (stabilization) • Since tracking tree is bounded to a depth R, soft-state stabilization is not available for nodes outside tree • Cycles are detected and removed by counting to R • Starting from an arbitrary state pursuer finds the tracking tree in at most O( (N-n)2 * log (N-n) ) steps • n : number of nodes in tracking tree • Then, pursuer catches evader within R*f/(1-f) steps • Hybrid program is tunable by assigning R appropriately
Outline • Evader-centric program • Pursuer-centric program • Hybrid program • Extensions
Extensions • Asynchronous model : Readily available • Faster convergence : Extended hybrid program • Better scalability : Hierarchical tracking program
Asynchronous model • Evader-centric program • instead of ts.j maintain val.j • val.j denotes the number of detections of the evader that j is aware of • when j detects evader it increments val.j • tracking tree is rooted at evader in 2D steps • we have implemented the asynchronous version for June 2002 DARPA/NEST demo • Pursuer-centric program • readily available
Extended hybrid program • Pursuer-centric program can be modified query a radius Rp(instead of 1) s.t. R+ Rp = D
Self-Stabilizing Hierarchical Tracking Service for Sensor Networks Murat Demirbas , Anish Arora , Tina Nolte , Nancy Lynch
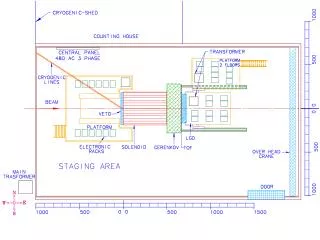
STALK: Scalable tracking • Maintain tracking structure • over fewer number of nodes • with accuracy inversely proportional to the distance from evader • communication cost of msgj,k= distance(j,k), delay= δ*distance(j,k) • nearby nodes (cheap to update) have recent & accurate info • distant nodes (expensive to update) have stale & rough info • Local operations : • Cost of move proportional to the distance the evader moves • Cost of find proportional to the distance from the evader • Cost of healing proportional to the size of the initial perturbation • To this end we employ a hierarchical partitioning of the network M. Demirbas, A. Arora, T. Nolte, and N. Lynch. A Hierarchy-based Fault-local Stabilizing Algorithm for Tracking in Sensor Networks. OPODIS, 2004.
Hierarchical clustering R: dilation factor of clustering to determine size at higher levels Radius at level L is ≈ RL M. Demirbas, A. Arora, V. Mittal, and V. Kulathumani. Design and Analysis of a Fast Local Clustering Service for Wireless Sensor Networks. BroadNets 2004.
Hierarchical tracking path evader evader evader • Grow action for building a tracking path • Shrink action for cleaning unrooted paths
Local find • Searching phase: • A find operation at j queries j’s neighbors & j’s clusterhead at increasingly higher levels to find the tracking path • Tracing phase: • Once path is found, operation follows the path to its root
Examples of find A find for an evader d away incurs O(d) work/time cost • guaranteed to hit the tracking path at level logRd of hierarchy evader find find find
A problem for move evader dithering between cluster boundaries may lead to nonlocal updates evader evader evader
Local move • Laterallinks to avoid nonlocal updates • When evader moves to new location j: • a new path is started from j • the new path checks neighbors at each level to see whether insertion of a lateral link is possible • Restricts lateral links to 1 per level in order not to deteriorate the tracking path • otherwise find would not be local since it could not hit the path at level logRd for an evader d away
Examples of move A move to distance d away incurs O(d*logRd) work/time cost • a level L pointer is updated at every iL-1Ridistance; level L is updated d/iL-1Ritimes • update at L incurs O(RL) cost evader evader evader evader evader evader evader
Local healing means work/time for recovery proportional to perturbation size & not the network size In the presence of faults a grow can be mistakenly initiated; shrink should contain grow a shrink can be mistakenly initiated; grow should contain shrink Local healing
Fault-containment • Give more priority to the action that has more recent info regarding the validity of the path • A shrink or grow action is delayed for longer periods as the level of the node executing the action gets higher • j.grow-timer = g * R lvl(j) • j.shrink-timer = s * R lvl(j) • Catching occurs within a constant number of levels • For g=5δ, s=11δ, b=11δR • grow catches shrink in 2 levels: logR ((bR–b+sR2–gR-δR)/(sR-gR-3δ)) • shrink catches grow in 4 levels: logR ((bR–b+sR+gR-2s+3δR)/(gR-s-δ))
Seamless tracking • Fault-containment does not affect responsiveness • Total delaying up to l is a constant factor of communication delay up to l, δR l • Concurrent move operations • move occurs before tracking path is updated • a complete path is no longer possible; discontinuity in the path • give a bound on evader speed to maintain a reachable path • Concurrent find operations • when find reaches a dead-end, search phase is re-executed • reachability condition guarantees that new path is nearby • Cost of find & move unaffected find