Techniques for Visual Feedback of Security State
90 likes | 308 Views
Techniques for Visual Feedback of Security State. Tara Whalen and Kori Inkpen Faculty of Computer Science Dalhousie University whalen at cs dot dal dot ca DIMACS Workshop on Usable Privacy and Security Software July 8, 2004. Introduction. Trying to define an area for doctoral research

Techniques for Visual Feedback of Security State
E N D
Presentation Transcript
Techniques for Visual Feedback of Security State Tara Whalen and Kori Inkpen Faculty of Computer Science Dalhousie University whalen at cs dot dal dot ca DIMACS Workshop on Usable Privacy and Security Software July 8, 2004
Introduction • Trying to define an area for doctoral research • ideas very much in development: feedback welcome and encouraged! • General focus: visualization of security information • Goal: to give users appropriate feedback about security • aid in assessment and carrying out appropriate actions • Dalhousie EDGE Lab focuses on collaboration and visualization • initial ideas focused on secure collaboration
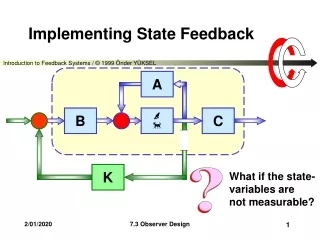
Security Lens • We looked at how to reveal security information for distributed collaboration • e.g., using a CSCW tool, or text messaging • how to quickly communicate that security configuration was done correctly • Led to the idea of a “security lens”: a representation of peering into a channel • Consider relevant parties along the path of communication • Use lens to show what security (secrecy) looks like from multiple perspectives: self, partner, world (eavesdroppers) • Currently a visualization technique, not a real tool
Simple example: text message • Include a lens in messaging application; user selects this when they want to run a check (preview) • Shown below is communication between two parties • Set view to self, Bob or world to see what is revealed to each • Could represent secrecy as unreadable text. Plaintext should be revealed only for self and partner
Advantages • At-a-glance view provides snapshot of useful security information • Provides a sort of sanity check for configuration • Can provide information on demand – not intrusive, gives feedback at appropriate time • Application-level data can provide context unavailable at lower level • e.g., can provide tailored feedback for specific actions, include info about private versus public keys, info about parties in communication
Challenges and Concerns • Pragmatically difficult: application-level view requires integration of lens into different programs • Simple example is simplistic: does not take into account the complexity of many situations • Lens perspective might be only useful for transactions, not long-duration activities (monitoring) • How to use the lens perspective for one user across multiple programs; potentially many different tasks, data, and roles to incorporate • How much approximation is appropriate? • Don’t want abstraction to cloud the facts • Correct configuration may not guarantee actual secrecy, and incorrect configuration may succeed if encryption exists at lower level • Would users bother to adjust perspective?
Future Directions • The direction is likely to be set through discussions at this workshop • Need to look at viability of perspective view as useful visualization technique • Can it be applied effectively across a range of applications and situations? • If it seems to be a helpful approach, then we can consider how this visualization might be done in practice • We are (in parallel) considering other visualization problems • how to present snapshots of host security information (e.g., personal firewall, virus scanner) • starting a small stud y on how people use visual security cues in web browsers
Conclusions • We feel that it is important to provide support for at-a-glance visualization of security information • This is not an easy problem: complex area, need to integrate variety of data types and tasks, don’t want to overwhelm user • Work is at very early stages: we hope to work with the researchers at this workshop to further refine our approach
Thanks! • Thanks for your kind attention • Thanks to Diana Smetters (PARC) and Paul Dourish (UC Irvine) for feedback on these early ideas • Please forward comments, suggestions, flames, etc., to whalen at cs dot dal dot ca