BLUETHOOTH ARCHITECTURE
200 likes | 396 Views
BLUETHOOTH ARCHITECTURE. Olena Hunsicker CS 555. WHAT IS BLUETOOTH WIRELESS TECHNOLOGY?. Bluetooth wireless technology is a short-range communications technology intended to replace the cables connecting portable and/or fixed devices while maintaining high security level.

BLUETHOOTH ARCHITECTURE
E N D
Presentation Transcript
BLUETHOOTH ARCHITECTURE Olena Hunsicker CS 555
WHAT IS BLUETOOTH WIRELESS TECHNOLOGY? Bluetooth wireless technology is a short-range communications technology intended to replace the cables connecting portable and/or fixed devices while maintaining high security level. The key features of Bluetooth technology are: • Robustness • low power • low cost
BLUETOOTH IS GLOBAL • One version for the world • Bluetooth technology operates in the unlicensed industrial, scientific and medical (ISM) band at 2.4 to 2.485 GHz. • The 2.4 GHz ISM band is available and unlicensed in most countries.
BLUETOOTH TECHNOLOGY USE Landline Cable Replacement Data/Voice Access Points Personal Ad-hoc Networks
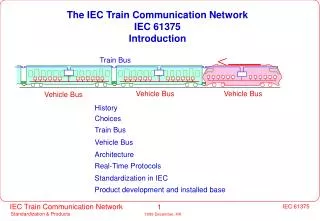
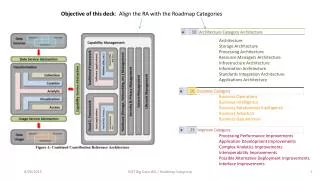
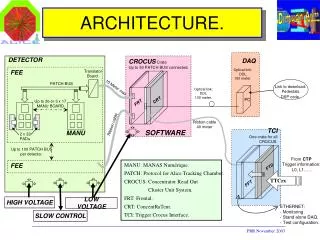
Applications TCP/IP HID RFCOMM Data Control Audio L2CAP LMP Link Manager Baseband RF BLUETOOTH PROTOCOL ARCHITECTURE Application Framework and Support Host Controller Interface Link Manager and L2CAP Radio & Baseband
Software Applications TCP/IP HID RFCOMM Data Control Audio L2CAP LMP Link Manager Baseband RF BLUETOOTH STRUCTURE Link Control Hardware
Link Control Hardware Duties: • radio transmission and reception • digital signal processing • establishing connection • support for asynchronous (data) && synchronous (voice) links • error correction • authentication • provide Host Controller Interface as a standard interface for software
Radio Layer (RF) • Operates in the unlicensed ISM (industrial, scientific, medical) band at 2.4 GHz • Responsible for transmitting and receiving packets of information on the physical channel • Transforms a stream of data to and from the physical channel into required formats. • Support data rate: 1Mbps (Basic Rate) / 3 Mbps (Enhanced Data Rate) • Bluetooth hops 1600 times/sec (uses frequency only for 625 microsecond) in order to avoid interference with other devices (frequency-hopping spread spectrum (FHSS)). Baseband RF
Network Topology • Piconet • Master can connect to 7 simultaneous active slaves per piconet • Scatternet • High capacity system • Minimal impact with up to 10 piconets within range S P M M sb P S sb P S S
Baseband Layer • Provide transmission channels for voice and data • Synchronousconnection-oriented (SCO) links - used for voice transmission. • Slave device is always allowed to respond during the time-slot immediately following a SCO transmission from the master • No retransmission allowed • Asynchronous connectionless (ACL) links -used for data transmission. • After an ACL transmission from the master, only the addressed slave device may respond during the next time-slot, or if no device is addressed, the packet is considered a broadcast message. • Packet retransmission allowed.
Frame Frame f f f f k k+1 k k+1 Master Master One One Slave Slave Slot Sot Packet Packet 625 us 625 us One Slot One Slot Basic Baseband Protocol • Spread spectrum frequency hopping radio • 79 or 23* one MHz channels (*country dependent) • Hops every packet • Packets are 1, 3, or 5 slots long • Frame consists of two packets • Transmit followed by receive • Nominally hops at 1600 times a second (1 slot packets)
Baseband RF Baseband Layer • Single-slave communication (one slave in piconet): • Time divided into slots 625 msec • Master uses even-numbered slots, slave – odd-numbered • Multiple-slave communication (more than one slave in the piconet) • Master uses even-numbered slots • Slaves use odd-numbered slots if they have packet to send, or stay silent if none. • All slaves listen on even-numbered slots
Audio L2CAP LMP Link Manager Baseband RF Link Manager • Link Manager duties: • Controls baseband state • Authentication and security services • QoS monitoring • Change slaves modes • Handling changes in master/slave roles • Communicate with each other using link management protocol (LMP)
TCP/IP HID RFCOMM Control Data Audio L2CAP Link Manager Baseband RF L2CAP • The lowest layer of software protocols • Provide service for upper level protocols transmitting data over L2CAP channels • The L2CAP Specification is defined for only ACL links and no support for SCO links. • Logical link control and Adoption Protocol (LL=2L) Applications
HOW TO ESTABLISH CONNECTION • The inquiry procedure enables a device to discover which devices are in range, and determine the addresses and clocks for the devices. (baseband layer). • Send out inquiry packets and then receiving the inquiry reply. inquiry packets inquiry reply
HOW TO ESTABLISH CONNECTION (cont) 2. Paging : Paging procedure synchronize the device with access point (baseband layer). 3. Establish a link : LMP establish a link with access point 4. Discover services : LMP uses Service Discovery Protocol (SDP) to find which services are available. 5. Create L2CAP channel: LMP create L2CAP channel to access point/or can use RFCOMM (Radio Frequency protocol) to simulate serial line. 6. Authentication: input from the user. Authentication request -> PIN -> encryption -> Authentication reply. 7. Log in : if use PPP over RFCOMM – serial port is emulated, then log in 8. Send and Receive: use TSP/IP
References: • R. Spaker, “ Bluetooth Basics” http://www.embedded.com/2000/0007/0007ia1.htm • Joe Decuir “Bluetooth™ Wireless System” • http://www.bluetooth.com/Bluetooth/