Advanced File Analysis System
Scan Files Online using Comodo File Verdict Service that runs tens of different methods to analyze a file and display the detailed results in seconds

Advanced File Analysis System
E N D
Presentation Transcript
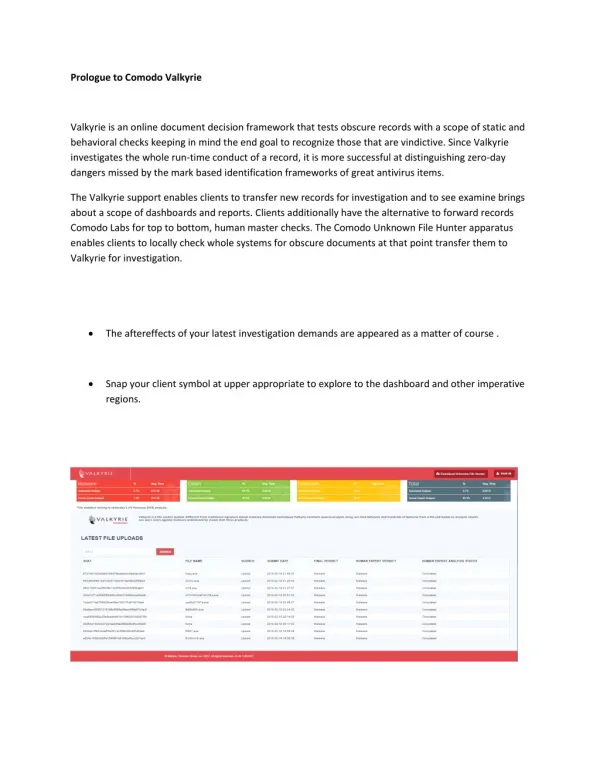
Prologue to Comodo Valkyrie Valkyrie is an online document decision framework that tests obscure records with a scope of static and behavioral checks keeping in mind the end goal to recognize those that are vindictive. Since Valkyrie investigates the whole run-time conduct of a record, it is more successful at distinguishing zero-day dangers missed by the mark based identification frameworks of great antivirus items. The Valkyrie support enables clients to transfer new records for investigation and to see examine brings about a scope of dashboards and reports. Clients additionally have the alternative to forward records Comodo Labs for top to bottom, human master checks. The Comodo Unknown File Hunter apparatus enables clients to locally check whole systems for obscure documents at that point transfer them to Valkyrie for investigation. The aftereffects of your latest investigation demands are appeared as a matter of course . Snap your client symbol at upper appropriate to explore to the dashboard and other imperative regions.
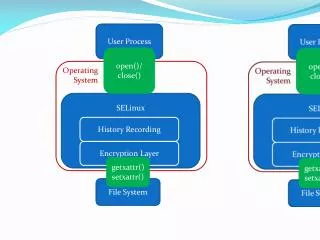
Highlights : No establishment required, simply transfer documents for examination . Computerized and human master examination (discretionary) of submitted documents . Far reaching detailing and dashboards. Diagram of the Technologies : Valkyrie investigation frameworks comprise of various methods to guarantee every single document submitted is examined altogether before giving the decision. Keeping in mind the end goal to do that Valkyrie conveys two sorts of advances - Automatic examination and Human Expert investigation. The strategies utilized for programmed investigation incorporate Static Analysis, Dynamic Analysis, Valkyrie Plugins and Embedded Detectors, Signature Based Detection, Trusted Vendor and Certificate Validation, Reputation System and Big Data VirusScope Analysis System. Static Analysis : This procedure includes extraction and investigation of different parallel highlights and static behavioral derivations of an executable, for example, API headers, alluded DLLs, PE areas and all the more such assets. Any deviation from the normal outcomes are recorded in the static investigation comes about and the decision given likewise. Dynamic Analysis : The dynamic investigation system incorporate concentrate the run time conduct of a document to distinguish malware designs that can't be recognized through static examination. Valkyrie Plugins and Embedded Detectors : Valkyrie modules uses the diverse malware investigation strategies created by different groups and instructive establishments and conveyed by them on their frameworks as RESTful Web Services. Valkyrie incorporates these outcomes additionally to register a last general decision. Installed indicators in Valkyrie utilizes new strategies for malware identification created by Comodo AV research center to register a general last decision of a document. Mark Based Detection :
Valkyrie utilizes distinctive mark based location sources to distinguish a given example in any case. Mark based location essentially checks SHA1 hash of records from signature sources to decide whether there is any match in database. Trusted Vendor and Certificate Validation : Valkyrie checks merchant subtle elements of a record with Trusted Vendor database that are ceaselessly refreshed. In the event that the merchant is whitelisted, at that point authentication approval is done to guarantee that declaration chain is substantial and not disavowed or lapsed. Notoriety System : Notoriety information of records that are gathered from a huge number of endpoints through Comodo system and items are assessed on a major information stage and changed over to knowledge shape to be utilized by Valkyrie. Huge Data VirusScope Analysis System : VirusScope, a piece of Comodo Security items, is a dynamic application analyzer framework that distinguishes pernicious conduct of a document, squares and turns around those activities when important. The distinguished malware are accounted for to Comodo servers and this information is likewise utilized by Valkyrie Human Expert Analysis : Valkyrie framework incorporates accommodation of records by clients for manual examination. Comodo master investigation, which comprises of the most modern examination of a document and gives a definitive decision of the record.