Understanding the Functions of an X.509 Certification Authority (CA)
Explore the functions of Certification Authorities (CAs) in enabling trusted online transactions through Public Key Infrastructure (PKI). Learn about PKI services, identity proofing, certificates, and the direct transaction process.

Understanding the Functions of an X.509 Certification Authority (CA)
E N D
Presentation Transcript
esMDAoR Functions of an X.509 Certification Authority (CA)
CAs and trusted online transactions Table of Contents SlideTitle 3 Trust and PKI 8 Certification Authorities 14 Certificates 19 Identity Proofing 24 PKI Services 28 Direct Transaction Process 29 Direct Provisioning 30 Q & A 31 Acknowledgements 32 About DigiCert
Trust • Trust occurs between people: Technology by itself is not sufficient to solve “Trust”issues • A Trust Framework is a set of standards that combines technology with policies on how and when a technology is utilized/applied, who the participants are, and what their roles and responsibilities are in the system • Public Key Infrastructures are a common methodology for implementing trust frameworks
What is PKI? • Public Key Infrastructure • Comprehensive security technology and policies using cryptography and standards to enable users to: • Identify (authenticate) themselves to network services, access policies, and each other to prove source of origin and destination. • Digitally sign electronic documents, email and other data to provide authorization and prove integrity. • Encrypt email, data, and other documents to prevent unauthorized access.
Why PKI? • Uniform way to address securing many different types of applications • Enables reliable authentication, digital signing and encryption of data/documents/identities • Overcomes many weaknesses of using password based protocols on open networks • Facilitates easy setup of shared secrets between previously unknown parties • Strong and proven underlying security technology • Widely included in technology products
Applications of PKI • Authentication and Authorization of end points in an internet transaction • e.g. users and servers, server to server, user to user • This is the basis for the SSL protocol used to secure web connections using https. • Secure Messaging • e-mail (signed and encrypted) • Secure instant messaging • Electronic signatures • Documents, data, agreements • Prescriptions, Insurance authorizations, case notes • Data encryption • Medical records, Diagnostic datasets, Business documents, Financial data, databases, executable code • Network data protection (VPN, wireless)
Components of PKI • Certification Authority (CA) • Policy (CP) & Practices (CPS) • Registration Authority (RA) • Practices (RPS) • Local Registration Agent (LRA) • X.509 Digital Certificates • Contents • Identity, Usage, Public Key, Validation • Types • Trust Anchors & enablers • Root Certificates, issuing authorities, cross-certificates • End Entities • Client, Server, Device, Group, Role • Cryptography • Algorithms & Protocols • Asymmetric Keys • Public Key, Private Key • Services • Authentication, Digital Signature, Encryption
What is a Certification Authority? • An organization that creates, publishes, and revokes certificates. • Verifies the information in the certificate, binds identities to cryptographic keys. • May outsource identity verification to Registration Authority • Protects general security and policies of the system and its records. • Allows you to check certificates so you can decide whether to use them in business transactions. • Has one or more trusted Roots, called a trust anchor embedded in applications
What is a Registration Authority? • An organization that collects and verifies the identity information that will be used in a certificate based on published standards. • Represents a Certification Authority for any face-to-face validation of identity • Must be authorized by the relevant Certification Authority for this purpose • Audit of processes required • Archival of evidence data required
Registration Authority (RA) Certificate Authority (CA) Identity/Trust Verification Compile/Validate Identity and Trust Documentation Certificate Validation Service Revocation Services Certificate Signing Services Certification Practices Statement Registration Practices Statement Audit RA Agreement Audit Audit CA – RA Relationship Source: DirectTrust.org February, 2012
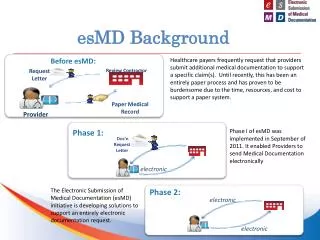
Health Information Service Provider (HISP) • Duties of a HISP: • provide subscribers with account and Direct addresses • provide web portal or EHR/PHR integration • arrange for identity verification - org and individual [RA function] • arrange for digital certificate issuance, management [CA function] • maintain integrity of trust and security framework • stay current with federal policies and regulations
HISP Configurations A HISP may run its own CA, but outsource RA functions to an accredited RA A HISP may run its own CA, and RA functions internally HISP HISP A HISP may outsource both CA and RA functions to accredited entities A HISP may run its own RA, but outsource CA functions to an accredited CA HISP HISP
What is a Certificate? • Signed data structure (x.509 standard) binds some information to a public key. • Trusted entity, called a Certification Authority (CA) asserts validity of information in the certificate, enforces policies for issuing certificates. • Certificate information is usually a personal identity, a server name, or a service identifier, with authorizations for how the keys should be used. • Think of a certificate with its keys as an electronic: • ID card, • encoder/decoder device, and • official seal or notary-style stamp.
Types of Certificates • DigiCert issues a number of different types of certificates. These are governed by the policy(s) they are issued under and the profile being applied: • SSL certificates (standard, Wildcard*, UC) • EV, OV, DV • Code Signing (including EV Code Signing) • Client Certificate (individual, group, role) • Level 1 Personal, level 1 Enterprise, Level 2 Corporate, Level 3 High Assurance / FBCA med / Direct, Level 4 High Hardware Assurance / FBCA Medium Hardware, PIV-I • Authentication Only • IGTF & Grid-Only • Device and Host certificates • L1 through L4 • IGTF & Grid-Only
Identity Proofing for Certificates • Group Certificates • DigiCertmay issue a group certificate (a certificate that corresponds to a Private Key that is shared by multiple Subscribers) if several entities are acting in one capacity and if non‐repudiation is not required. DigiCertor the RA records the information identified above for a sponsor before issuing a group certificate. The sponsor must be at least an Information Systems Security Officer or of the equivalent rank or greater within the organization. • For Direct certificates, the HISP ISSO and the Provider organization representative are both validated • Device Certificates • DigiCertissues Level 1, 2, 3 or 4 Client and Federated Device Certificates for use on computing or network devices, provided that the entity owning the device is listed as the subject. In all cases, the device has a human sponsor who provides: • Equipment identification (e.g., serial number) or service name (e.g., DNS name), • Equipment public keys, • Equipment authorizations and attributes (if any are to be included in the certificate), and • Contact information. • Sponsor is also vetted according to processes defined of individual at required LoA • Identity is revalidated according to the following schedule: • Device Certs: at least every 39 months • Individual Certs (levels 1 thru 4): at least every 9 years (if 3-year cert)
PKI Services • Certificates (containing public keys) and corresponding private keys are used to provide a range of cryptographic services: • Confidentiality (encryption) • Integrity (digital signature) • Authentication (digital signature) • Multiple algorithms and standards can be used • Federal Information Processing Standards (FIPS) exists for federal agencies • e.g. FIPS 186 for Digital Signatures
Encryption Asymmetric encryption prevents need for shared secrets. Anyone encrypts with public key of recipient. Requires some mechanism for discovering intended recipient’s public key Only the recipient can decrypt with their private key. Private key is secret, so “bad guys” can’t read encrypted data.
Digital Signatures Compute message digest, encrypt with your private key. Reader decrypts with your public key. Re-compute the digest and verify match with original – guarantees no one has modified signed data. Only signer has private key, so no one else can spoof their digital signature.
public public Authentication A CA - Certification Authority, signs a certificate attesting that the public key belongs to the entity named in the certificate Certificate Policy indicates what steps are taken to verify identity and how the CA systems operate to ensure security and integrity CA is a Trusted Third Party providing a seal of authenticity Use of certificate provides reliability and non-repudiation in the identity of the source or destination of a transaction
Transactions Certificates vetted to FBCA Medium LoA standard ensures strongest binding between PKI keys and identity listed in the cert HIPAA Covered Entity Assertion governed by DirectTrust CP PKI Encryption ensures confidentiality in messages PKI Digital Signatures ensures integrity and reliability of messages PKI Authentication provides authenticity and trust of message reaching intended recipients
Assume has Digital Identity Certificate Registration Authority (RA) Certificate Authority (CA) Domain Name System (DNS) Compile/Validate Identity and Trust Documentation Identity/Trust Verification Certificate Validation Service Revocation Services Certificate Signing Services HCO Representative Health Information Service Provider (HISP) LDAP Name System Healthcare Organization (HCO) Direct Identity, Trust, and Address Provisioning The CA and RA enforce the policies specified in the DirectTrust.org and FBCA Certificate Policies (CPs). 6. Certificate Signing Request 7. Direct Organization Certificate 2. Request Direct Organization Certificate 3. Credentials and Documentation • Representative FBCA Credentials • Representative Authorization • Legal Entity Documents • Membership/Trust Agreement • HIPAA status 5. CSR + Public Key 4. Direct OrganizationDomain 8. Direct Organization Certificate 1. Enroll with HISP 9. Direct Address/ Org Certificate Source: DirectTrust.org February, 2012
Related CA Questions and Answers • What ability is there to issue multiple digital credentials with one identity proofing? • This is perfectly allowable process, typically an already credentialed entity presents their original certificate as proof of identity binding and can be issued a certificate of equal or less LoA • Identity must be revalidated periodically via original process (at least 39 months for device, 9 years for individual (including group certs) • What is the Revocation process • DigiCert provides a Managed PKI interface (hosted web portal) that allows for issuance, revocation and renewal of certificates. • DigiCert also provides an API (REST-based) for application integration that has similar functionality • What about Proxy Certificates for delegation of rights • Proxy certificates are issued by end entities and not by a CA. As such they are typically not trusted in browsers without appropriate plugins to circumvent the trust validation up to an embedded Root • Proxy certs are used quite successfully in other communities e.g. IGTF and where purpose built application manage them appropriately
Questions? • Scott Rea, CISSP VP GOV/EDU Relations and Sr. PKI Architect DigiCert, Inc. Lindon UT 84042 (Also note: Member of DirectTrust.org) • Scott@DigiCert.com • (801) 701-9636 • http://www.digicert.com/news/bios-scott-rea.htm • http://www.DigiCert.com/
About DigiCert A Few Facts DigiCert – a local interface to your global trust community. • DigiCert established in 2003, a Root CA • DigiCert’s management has combined about 100 years experience in internet security • Frost & Sullivan and Netcraft survey ranks DigiCert 3rd largest high-assurance CA • DigiCert is growing fast • WebTrust audited • DigiCert growing its business globally 146 Countries and Growing!
About DigiCert Who Uses DigiCert? DigiCert provides encryption and authentication services to over 50,000 customers.
About DigiCert DigiCert Trusted Roots DigiCert Trusted Roots Already Embedded In: • Web Browsers • AOL • Firefox • Google Chrome • Internet Explorer • Safari • Konqueror • Camino • Mozilla • Netscape • Opera • Mobile Devices • Android OS • Blackberry OS • iPhone OS • Nokia E-Series Phones • Palm • Symbian OS • Windows Mobile
About DigiCert Rapid Growth DigiCert is the 3rd largest provider of high assurance SSL certificates and among the world’s fastest growing companies:
About DigiCert Testimonials DigiCert features more 5-star reviews than any other Certificate Authority on sslshopper.com. Here are a few user-generated quotes: “This company is 5/5 for me, and I’m the kind of guy who could rate something as 4.97 / 5 out of sheer pickiness” (Dec 16, 2010) “These guys have provided the best level of customer service Ihave ever experienced anywhere.” (Dec 22, 2010) “Miles above the other well known names. Thanks a million to DigiCert and their team” (Oct 22, 2010)
About DigiCert Features DigiCert SSL Certificates Feature: 99.5% Browser Compatibility Unlimited Server License Secure Trust Seal Award-winning 24/7 customer support $1,000,000 Warranty
About DigiCert Managed-PKI Easily manage thousands of SSL certificates with our enterprise-grade, web-based PKI. Instantly approve or reject certificate requests. Intuitive user interface with multiple levels of authority. Assign business units to sub-accounts with limited access. Centralize control while distributing workload.
About DigiCert Industry Leader DigiCert leads the industry toward better practices by participating actively in the following groups: FBCA CA/Browser Forum Four Bridges Forum
About DigiCert Awards DigiCert has been recognized multiple times for its excellence in customer value, customer support and the workplace.