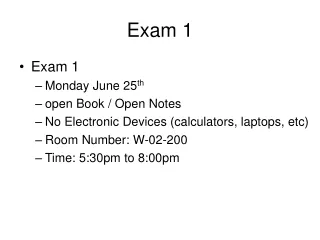
Exam 1
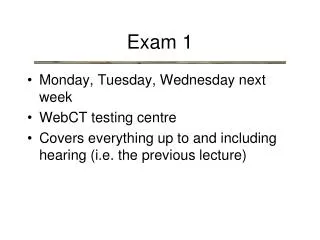
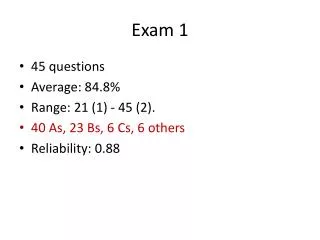
Exam 1. Security policy Evaluate python and linux commands Identification vs Authentication vs authorization Confidentiality, availability, integrity Types of attacks (phishing, spoofing, brute force, dictionary , intelligent,…) Input validation Passwords against attack type

Exam 1
E N D
Presentation Transcript
Exam 1 • Security policy • Evaluate python and linuxcommands • Identification vs Authentication vs authorization • Confidentiality, availability, integrity • Types of attacks (phishing, spoofing, brute force, dictionary, intelligent,…) • Input validation • Passwords against attack type • Categories of systems which need security • Man vs. machine model • Types of authentication • Security management • Encryption (high lvl only) • Database security • Access Control • Something you know/are/have