Proactive Forensics of Web Application Attacks
Proactive Forensics of Web Application Attacks. Shlomi Ben- Hur and Shay Chen Hacktics ASC. A Step By Step Guide. June 2013. Introduction. Shlomi Ben- Hur. Shay Chen. Hacktics ASC, E&Y Chief Technology Officer. Hacktics ASC, E&Y Forensics Service Leader. Shlomi.Ben-Hur@il.ey.com.

Proactive Forensics of Web Application Attacks
E N D
Presentation Transcript
Proactive Forensics of Web Application Attacks Shlomi Ben-Hur and Shay Chen Hacktics ASC A Step By Step Guide • June 2013
Introduction Shlomi Ben-Hur Shay Chen Hacktics ASC, E&Y Chief Technology Officer • Hacktics ASC, E&Y • Forensics Service Leader Shlomi.Ben-Hur@il.ey.com Shay.Chen@il.ey.com
Proactive Web Forensics (PWF): What’s New? • The Business Case • An excellent tool for managing budgets and priorities • Proactive process benefits • Recent Technical Advancements • Methodology per vulnerability (as in Security Assessments) • New commercial tools and open source projects
A Missing Piece The Limitations of Traditional Security Controls
Traditional Services – Penetration Tests • Locates “A possible way into the system” • Doesn’t provide solid proof the system was hacked Do we know if the system was Hacked?
Traditional Services – Forensics • Indentify and trace-back security incidents • Trace-back limited to the attacks that caused the impact In the absence of a “Trigger”, We’re left unaware as to whether the system was actually compromised
The Current Coverage of Security Controls Security Testing (Attack & Pen) SIEM/SOC Reactive Forensics • Undetected Incidents, Attacks & Vulnerabilities
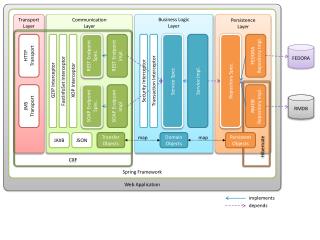
What is Proactive Web Forensics? Attacks leave traces and audit trails Familiarity with System Architecture Identify attacks and hacking incidents for each component
The outcome of a PWF process Provides evidence of system hacks Identifies how attacks were performed Evaluates the severity of hacks
Benefits of Proactive Web Forensics Identify your most attacked/hacked systems Identify the impact on sensitive systems
Benefits of Proactive Web Forensics Request Budget Based on Facts Improve Risk Management Manage Resources Effectively Spot-on Security Controls
We’re currently mitigating POSSIBILITIES, Wouldn't we do it better if we mitigated FACTS?
Proactive Web Forensics Capabilities, Methodologies and Tools
Prolonged and Ongoing Incidents • Incident Components • Vulnerability Detection • Exploitation • Incubation Period • Impact • Incident Timeframes • Dormant, Ongoing, Prolonged and Immediate • Incident Response Timeframes
Why PWF? • Exposures detected in pen-tests are rarely investigated • There usually isn’t any attempt to identify past exploits • Exploitation might have occurred prior to the implementation of countermeasures: • WAF / IDS / Security Mechanisms Integration • An active or dormant exploit could be hosted on a machine for years, and the evidence may still be there.
Information Sources • Triggers • Penetration Test Reports • File System • File Metadata • Crash Dump Files • Content • Data Repository Content (DB, Web, File, LDAP, etc) • Log Files • OS, Web Server, DB, Application, Network Devices • Security Products, Forensics Blackbox, SIEM/SOC • 3rd Party Analysis Tools • Google Analytics, External Captcha Repositories, Etc
POC: Locating Persistent XSS in System DB • Persistent XSS rely on HTML/JS/VBS injection, in either clear on encoded format; these patterns can be detected by scanning the data stored in the database, and the content hosted on the website: • iScanner / ScanEx vs. Live Web Site • OWASP Scrubber vs. Database
POC: Locating Malicious File Upload • Abusing vulnerabilities to upload malicious files eventually results in the malicious file being uploaded into the context of the web application.: • Check the system metadata of the application files and locate abnormal date/time, permissions or similar properties. • Use WinMerge to compare the application files in the production environment to those of the relevant build in the development / staging environment. • Recover deleted file names in the web application directories • Compare deleted file names to historical file names in the source code management systems
POC: Locating SQL Injection Attempts • SQL Injection is often performed after executing multiple attempts with invalid syntax. These instances often cause exceptions that leave traces in multiple layers: • Apache Scalp & PHP IDS on System Logs
Prominent Open Source Analysis Tools • Initial Log Analysis • AWStats • Log Analysis Tools • Apache Scalp & PHP IDS Engine • Web Forensik • PHP IDA • File Metadata Analysis Tools • Winmerge • Content/Data Analysis • iScanner / ScanEx • OWASP Scrubber
Log Analysis Perquisites • Infrastructure Familiarity • CMS/Framework Logs • OS/Database Logs • Crash Dump Files • Application Familiarity • External Data Tracked by 3rd Party Components
Wordpress / Apache / MySQL Sample • Wordpress • Optional* configuration in file: ‘wp-config.php’, Relevant values: • @ini_set('log_errors','On') • @ini_set('error_log','/SecuredPath/logs/wp-php_error.log') • Apache • Default Access and Error logs Path:Linux Installation: ‘/var/log/apache2/’ - access_log, error_logWindows Installation: ‘Apache root/logs/’ - access.log, error.log • MySQL • By default, the server writes files for all enabled logs in the data directory(i.e. . • By default, no logs are enabled(except the error log on Windows), Optional log types: Error log, General Query log, Binary log, Relay log, Slow query log
Environment Comparison Perquisites • Version History • SCM Repositories • SVN, CVS, Mercurial, Git, SourceSafe, Etc • Developer Stations • Backup Solutions • NAS, Drives, Cloud, Etc • Technology Familiarity • Identify executables, legitimate and illegitimate files
Proactive Web Forensics in the Security Lifecycle
PWF Triggers in Security Assessments • Embedding PWF in the organization security policy • After detecting high risk vulnerabilities in penetration tests, follow up and check if they were exploited
Proactive Web Forensics Frequency • Assessment Frequency • Sample Scenario: Incubation Period Effective Response Timeframe Exploit Impact Exposure Detection PONR 2 Months 3 Months Insurance Timeframe Trojan via SQL Injection Theft Start Theft End Infection PONR
PWF Frequency Formula Glossary • Incubation Period • The incubation period of the Attack AND Exploitation • Affected by the type of system and the type of exploit • Effective Response Timeframe • The timeframe in which a proper incident response will still mitigate the damage somehow • PWF Analysis Timeframe • The assessment segment dedicated to analysis information sources Analysis Result: The gap between PWF instances
Potential Issues • False Positives • Penetration Tests might create similar traces • Can be mitigated by focusing on events that occurred in dates prior to the penetration test, and/or on events generated from non trusted sources. • An ever growing collection of attack vectors • Focus on attack vectors with higher severity • Adapt the assessment for each technology-in-use • Enhance the assessment methodology and toolset over time
Recommendations • Embed PWF into the organization security lifecycle • Calculate the PWF frequency based on the threat map • Perform PWF periodically on sensitive • Use output to adjust budget allocations and priorities • Perform PWF follow-ups on severe exposures detected in attack and penetration services • Identify past exploitations of vulnerabilities • Evaluate the severity of the impact • Adapt PWF to system specific technology and enhance the PWF tool arsenal
References • WASC Web Hacking Incident Database: http://goo.gl/zNwMU • Presentations • Web Application IR & Forensics: A whole New Ball Game! • Blackhat Aug 2006 & AppSec Seattle 2006 • Web Application Digital Forensics (ISACA) • Whitepapers • Web Application Forensics: Taxonomy and Trends • Krassen Deltchev, Sep 5th, 2011 • Web Application Forensics: The Uncharted Territory • Ory Segal, July 2002 • Fingerprinting port 80 Attacks, Part 1 & 2 • CGI Security, March 2002