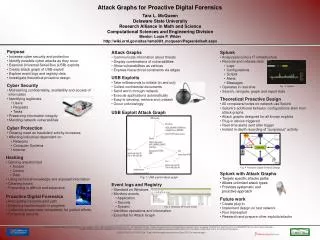
Attack Graphs for Proactive Digital Forensics
Attack Graphs for Proactive Digital Forensics. Tara L. McQueen Delaware State University Louis P. Wilder Computational Sciences and Engineering Division August 2009. Overview. Purpose Cyber Security Hacking Proactive digital forensics Attack graphs Universal Serial Bus (USB) exploits

Attack Graphs for Proactive Digital Forensics
E N D
Presentation Transcript
Attack Graphs for Proactive Digital Forensics Tara L. McQueen Delaware State University Louis P. Wilder Computational Sciences and Engineering Division August 2009
Overview • Purpose • Cyber Security • Hacking • Proactive digital forensics • Attack graphs • Universal Serial Bus (USB) exploits • Registry and event logs • Future work
Purpose • Increase cyber security • Identify possible cyber attacks as they occur • Create attack graph of USB exploit • Link event logs and registry data to attack graph • Investigate theoretical proactive design
Cyber security • Maintaining confidentiality, availability and access of information • Identifying legitimate • Users • Requests • Tasks • Preserving information integrity • Mending network vulnerabilities • Hacking prevention/detection
Cyber protection • Growing need as fraudulent activity and electronic commerce increases • Affecting industries dependent on • Networks • Computer Systems • Internet
Hacking • Gaining unauthorized • Access • Control • Data • Using technical knowledge and exposed information • Cleaning tracks • Preventing is difficult and expensive
Proactive digital forensics • Anticipating hacker/exploit path • Detecting hacker/exploit in process • Collecting proper data immediately for judicial efforts • Enhancing security
Attack graphs • Communicate information about threats • Display combinations of vulnerabilities • Shows • Vulnerabilities as vertices • Hierarchical constraints as edges
USB attack • Take milliseconds to initiate (drive by) • Collect confidential documents • Send worm through network • Execute applications automatically • Easy to develop, retrieve and unleash • Occur unknowingly
Registry and event logs • Standard on Windows • Monitors events • Application • Security • System • Identifies operations and information • Essential for attack graph
Conclusion • Numerous of attack paths can be targeted • Systematic and proactive approach can be reached • Real-time detection and alerts • Detailed recordings can be triggered for judicial efforts
Future work • Create plug-in • Implement design on test network • Run trial exploit • Research and prepare other exploits/attacks
Acknowlegments Louis P. Wilder, Christopher Lanclos, Sharon Hastings, Joe Trien George Seweryniak, Debbie McCoy, Rashida Askia and Cindy Latham The Research Alliance in Math and Science program is sponsored by the Office of Advanced Scientific Computing Research, U.S. Department of Energy. The work was performed at the Oak Ridge National Laboratory, which is managed by UT-Battelle, LLC under Contract No. De-AC05-00OR22725. This work has been authored by a contractor of the U.S. Government, accordingly, the U.S. Government retains a non-exclusive, royalty-free license to publish or reproduce the published form of this contribution, or allow others to do so, for U.S. Government purposes.