Network Security Topologies
Network Security Topologies. Chapter 11. Learning Objectives. Explain network perimeter’s importance to an organization’s security policies Identify place and role of the demilitarized zone in the network Explain how network address translation is used to help secure networks

Network Security Topologies
E N D
Presentation Transcript
Network Security Topologies Chapter 11
Learning Objectives • Explain network perimeter’s importance to an organization’s security policies • Identify place and role of the demilitarized zone in the network • Explain how network address translation is used to help secure networks • Spell out the role of tunneling in network security • Describe security features of virtual local area networks
Perimeter Security Topologies • Put in place using firewalls and routers on network edge • Permit secure communications between the organization and third parties • Key enablers for many mission-critical network services • Include demilitarized zones (DMZs) extranets, and intranets continued…
Perimeter Security Topologies • Selectively admit or deny data flows from other networks based on several criteria: • Type (protocol) • Source • Destination • Content
Three-tiered Architecture • Outermost perimeter • Internal perimeters • Innermost perimeter
Outermost Perimeter • Router used to separate network from ISP’s network • Identifies separation point between assets you control and those you do not • Most insecure area of a network infrastructure • Normally reserved for routers, firewalls, public Internet servers (HTTP, FTP, Gopher) • Not for sensitive company information that is for internal use only
Internal Perimeters • Represent additional boundaries where other security measures are in place
Network Classifications • Trusted • Semi-trusted • Untrusted
Trusted Networks • Inside network security perimeter • The networks you are trying to protect
Semi-Trusted Networks • Allow access to some database materials and e-mail • May include DNS, proxy, and modem servers • Not for confidential or proprietary information • Referred to as the demilitarized zone (DMZ)
Untrusted Networks • Outside your security perimeter • Outside your control
Creating and Developing Your Security Design • Know your enemy • Count the cost • Identify assumptions • Control secrets • Know your weaknesses • Limit the scope of access • Understand your environment • Limit your trust
DMZ • Used by a company to host its own Internet services without sacrificing unauthorized access to its private network • Sits between Internet and internal network’s line of defense, usually some combination of firewalls and bastion hosts • Traffic originating from it should be filtered continued…
DMZ • Typically contains devices accessible to Internet traffic • Web (HTTP) servers • FTP servers • SMTP (e-mail) servers • DNS servers • Optional, more secure approach to a simple firewall; may include a proxy server
DMZ Design Goals • Minimize scope of damage • Protect sensitive data on the server • Detect the compromise as soon as possible • Minimize effect of the compromise on other organizations
Intranet • Either a network topology or application (usually a Web portal) used as a single point of access to deliver services to employees • Typically a collection of all LANs inside the firewall • Shares company information and computing resources among employees continued…
Intranet • Allows access to public Internet through firewalls that screen communications in both directions to maintain company security • Also called a campus network
Extranet • Private network that uses Internet protocol and public telecommunication system to provide various levels of accessibility to outsiders • Can be accessed only with a valid username and password • Identity determines which parts of the extranet you can view continued…
Extranet • Requires security and privacy • Firewall management • Issuance and use of digital certificates or other user authentication • Encryption of messages • Use of VPNs that tunnel through the public network
Network Address Translation (NAT) • Internet standard that enables a LAN to use one set of IP addresses for internal traffic and a second set for external traffic • Able to translate addresses contained in an IP packet
Main Purposes of NAT • Provide a type of firewall by hiding internal IP addresses • Enable a company to use more internal IP addresses
NAT • Most often used to map IPs from nonroutable private address spaces defined by RFC 1918 • Static NAT and dynamic NAT • Port Address Translation (PAT) • Variation of dynamic NAT • Allows many hosts to share a single IP address by multiplexing streams differentiated by TCP/UDP port numbers • Commonly implemented on SOHO routers
Tunneling • Enables a network to securely send its data through untrusted/shared network infrastructure • Encrypts and encapsulates a network protocol within packets carried by second network • Best-known example: virtual private networks • Replacing WAN links because of security and low cost • An option for most IP connectivity requirements
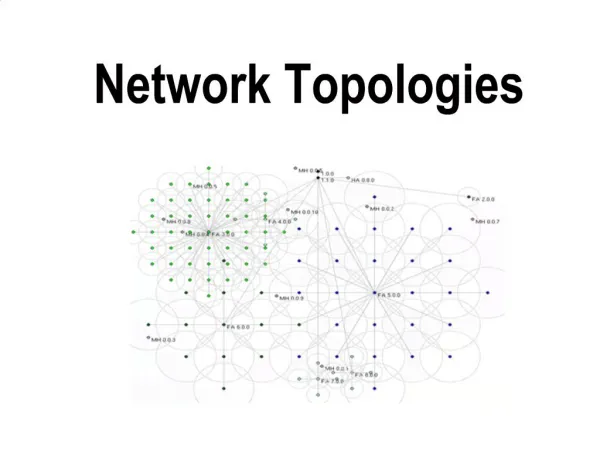
Virtual Local Area Networks (VLANs) • Deployed using network switches • Used throughout networks to segment different hosts from each other • Often coupled with a trunk, which allows switches to share many VLANs over a single physical link
Benefits of VLANs • Network flexibility • Scalability • Increased performance • Some security features
Security Features of VLANs • Can be configured to group together users in same group or team • Offer some protection when sniffers are inserted into the network • Protect unused switch ports • Use an air gap to separate trusted from untrusted networks
Vulnerabilities of VLAN Trunks • Trunk autonegotiation • Prevention: Disable autonegotiation on all ports • Trunk VLAN membership and pruning • Prevention: Manually configure all trunk links with the VLANs that are permitted to traverse them
Chapter Summary • Technologies used to create network topologies that secure data and networked resources • Perimeter networks • Network address translation (NAT) • Virtual local area networks (VLANs)