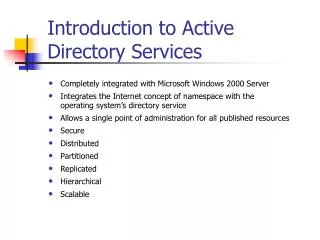
Introduction to Active Directory Services
570 likes | 976 Views
Introduction to Active Directory Services. Completely integrated with Microsoft Windows 2000 Server Integrates the Internet concept of namespace with the operating system’s directory service Allows a single point of administration for all published resources Secure Distributed Partitioned

Introduction to Active Directory Services
E N D
Presentation Transcript
Introduction to Active Directory Services • Completely integrated with Microsoft Windows 2000 Server • Integrates the Internet concept of namespace with the operating system’s directory service • Allows a single point of administration for all published resources • Secure • Distributed • Partitioned • Replicated • Hierarchical • Scalable
Understanding Active Directory Concepts • Schema • defines attributes an instance class must have and those attributes that are optional • What Object classes can be parents • Default schema contains definitions of most commonly used objects • Extensible schema • Can name new object types and their attributes • Or new attributes of existing objects • Not for the faint hearted
Global Catalog • The global catalog is the central repository of information about objects in a domain tree or forest. • Contents generated by AD Services • Only the most frequently used attributes • The global catalog is a service as well as a physical storage location that contains a replica of selected attributes of every object in the Active Directory store. • By default, the first domain controller is a global catalog server. • Additional domain controllers can also be designated as global catalog servers by using the Active Directory Sites And Services snap-in.
Understanding Active Directory Concepts • Namespace • Any bounded area in which a name can be resolved • Based on DNS naming scheme • Contiguous namespace • Parent name part of full name • Disjoint namespace
Distinguished Names (DNs) • Objects are located within Active Directory domains according to a hierarchical path. • Every object in the Active Directory store has a DN, which uniquely identifies the object. • The DN includes the name of the domain that holds the object as well as the complete path through the container hierarchy to the object. For example: if John Smith works for msft.com and is a member of the CONTOSO domain his DN is DC=com/DC=msft/DC=Contoso/CN=Users/CN=John Smith
Relative Distinguished Names (RDNs) • The RDN is one of an object’s attributes. • The RDN is part of the full DN. For example: CN=John Smith • Active Directory services allows duplicate RDNs for objects, but no two objects with the same RDN can exist within the same OU.
Globally Unique Identifiers (GUIDs) • Assigned to every object • 128 bit number • Never changes • Identifies Object regardles of DN • Unique across Domains • Stored in an Object attribute • Can move objects but GUID stays the same
User Principal Names (UPNs) • The UPN is a friendly name that is shorter than the DN and easier to remember. • The UPN consists of a shorthand name that represents the user and usually the DNS name of the domain where the object resides. • Independent of DN • Example: johns@contoso.msft
Active Directory Structure • Data model • X.500 • Schema • Class instances • Can be updated dynamically • Protected by ACL’s • Security model • Trusted Computer Base • Administration model • Authorized to perform certain set of actions • Directory System Agent • Manages physical storage
Protocol Support • LDAP is the Active Directory core protocol. • V2 or v3 • Active Directory services supports remote procedure call (RPC) interfaces that support Messaging Application Programming Interface (MAPI) interfaces. • The Active Directory information model is derived from the X.500 information model. • Does not support all x.500 defined wire protocols
Application Programming Interfaces (APIs) • Active Directory Service Interfaces (ADSI) • Easy to write applications • Developers - C++, VB • Administrators - C++, VB, Script • Users - Script • LDAP C API • Ability to work with many types of clients • Windows MAPI • Outlook or other legacy apps
Virtual Containers • Active Directory services supports virtual containers, which allow any LDAP-compliant directory to be accessed transparently through Active Directory services. • The virtual container is implemented via location information in the Active Directory store. • Location describes where in the AD Store the foreign directory should appear
Interfaces • LDAP provides the API for LDAP clients and exposes the ADSI so that additional applications can be written that can talk to the Active Directory services. • REPL is used by the replication service to facilitate Active Directory replication via RPC over Internet Protocol (IP) or Simple Mail Transfer Protocol (SMTP). • SAM Provides down-level compatibility to facilitate communication between Microsoft Windows 2000 and Microsoft Windows NT 4.0 domains. • MAPI supports legacy MAPI clients.
Directory System Agent (DSA) • Object identification • Maintains GUID association with object • Transaction processing • Commit / Rollback • Schema enforcement of updates • Multimaster Replication • Duplication and Synchronization of directory information • Change in an object may conflict with other object in same or other replicas • Single-master Replication • Any change you make on the master is made on all replicas • Ie. Schema changes must be replicated to preserve consistency • Access control enforcement • SIDs • Support for replication • Referrals
Database Layer • Provides an object view of database information by applying schema semantics to database records • Is an internal interface that is not exposed to the public • Follows the parent references in the database and concatenates the successive RDNs to form DNs • Translates each DN into an integer structure called the DN tag, which is used for internal access • Is responsible for the creation, retrieval, and deletion of individual records, attributes, and values
Extensible Storage Engine (ESE) • A new and improved version of the JET database • Implements a transacted database system that uses log files to ensure that committed transactions are safe • Stores all Active Directory objects • Comes with a predefined schema that defines all the attributes required and allowed for a given object • Stores attributes that can have multiple values • Can handle sparse rows
Introduction to Namespace Planning • Consists of • Doman hierarchy • Global catalog • Trust relationships • OU’s • The Active Directory namespace is the top-level qualified domain name for the company. • You must determine whether the internal and external namespaces will be the same or separate. • Internal - Inside the firewall • External - Outside the firewall • Registered Domain Name • Your name space architecture should be: • scalable • adaptable to change • able to distinguish between internal and external resources • protect company data
Scenarios • Same internal and external name space • Internal users can access both intranet and internet servers • External users external users can access internal resources • Solution • Company DNS divided into two zones • One resolves resources for external users - outside the firewall • The other resolves resources for internal users – inside the firewall • May need to duplicate the external zone for internal user access • Advantage - Single logon, Consistent naming • Disadvantage – complicated, duplication, different view of internal and external resources
Scenarios • Different internal and external name space • Requires registering two Domain Names • If internal name not reserved someone else may use it??? • Two DNS Zones • Advantages • Distinct difference between internal and external resources • No overlap or duplication • Configuration simpler • Disadvantages • Registering two names • Different logon names and email names • Internal ken@expedia.dom • Email ken@microsoft.com
Introduction to OU Planning • OUs should reflect the details of the organization’s business structure. • Create OUs to delegate administrative control over smaller groups of users, groups, and resources. • OUs eliminate the need to provide users with administrative access at the domain level. • OUs inherit security policies from the parent domain and parent OU unless inheritance is specifically disabled.
Creating the OU Structure • You should begin your OU design by creating an OU structure for the first domain in the namespace. • When you create an OU, you should determine who will be able to view and control certain objects and what level of administration each administrator will have over the objects.
OU Design Guidelines • Create OUs to delegate administration. • Create a logical and meaningful OU structure that allows OU administrators to complete their tasks efficiently. • Create OUs to apply security policies. • Create OUs to manage the visibility of published resources. • Create OU structures that are relatively static. OUs also give the namespace flexibility to adapt to changing needs of the enterprise. • Avoid allocating too many child objects to any OU.
Structure the OU Hierarchy • Administration-based or object-based Ous • Users, Computers, applicatiosn • Geographical-based Ous • Eastern, Central, Rocky Mountaion .. • Business function–based Ous • Accounting, Finance, Marketing, Manufacturing • Department-based Ous • Shipping, Receiving, Sales • Project-based Ous
Introduction to Site Planning • The physical design of a Windows 2000 network is demarcated by site. • The Active Directory replication engine allows you to differentiate between replication over a LAN and replication over a WAN. • How you set up your sites affects Windows 2000 with respect to workstation logon and directory replication. • In Active Directory services, sites are not part of the namespace. • Properly planned sites ensure that network links are not saturated by replication traffic, that Active Directory services stay current, and that client computers access resources that are closest to them. • When planning how to group subnets into sites, consider the connection speed between the subnets.
Optimizing Workstation Logon Traffic • When planning sites, consider which domain controllers workstations should use. • To have a particular workstation log on to a specific set of domain controllers, define the sites so that only those domain controllers are on the same site as the workstation.
Optimizing Directory Replication • When planning sites, consider where the domain controllers will be located. • Configure sites so that replication occurs at times or intervals that will not interfere with network performance. • When implementing sites in branch offices, base your planning on the size of the branch office.
Adding or Creating a Domain Controller • If you add a domain controller to an existing domain, you create a peer domain controller. • If you create the first domain controller for a new domain, you are creating not only the domain controller but also a new domain.
The Active Directory Database and the Shared System Volume Created when Active Directory Services is installed
The Active Directory Database • The database is a file named Ntds.dit, which is the directory for the new domain. • The default location for the database and the database log files is %systemroot%\Ntds, although you can specify a different location. • The database contains all the information stores in the Active Directory store. • The Ntds.dit file is an ESE database that contains the entire schema, the global catalog, and all the objects stored on that domain controller.
The Shared System Volume • The shared system volume is a folder structure that exists on all Windows 2000 domain controllers. • The shared system volume stores scripts and some of the group policy objects for the current domain as well as the enterprise. • Replication of the shared system volume occurs on the same schedule as Active Directory replication.
Domain Modes • Mixed mode • Native mode
Introduction to OUs and their Objects • Each Active Directory object is a distinct named set of attributes that represents a specific network resource. • Before objects are added to Active Directory services, you should create the OUs that will contain those objects. • Snap-ins • Active Directory Domains and Trusts • Active Directory Sites and Services • Active Directory Users and Computers • Active Directory Schema • Active Directory Group Policy • Active Directory Security Configuration and Analysis • Active Directory Security Templates • Low Level Active Directory Editing • Active Directory Replication Monitor
Contact User Printer Shared Folder Computer Group Adding Objects to OUs
Modifying Attributes and Deleting Objects • You can modify the attributes of an object to change or add information. • You can modify an object’s attribute by opening the properties for that object in the Active Directory Users And Computers snap-in. • To maintain security, delete objects when they are no longer needed.
Moving Objects • You can move objects from one location in the Active Directory store to another location. • You should move objects when organization or administrative functions change.
Managing Active Directory Permissions • Use Active Directory permissions to determine who has the permissions to gain access to the object and what type of access is allowed. • The object type determines which permissions you can select. • Permissions inheritance minimizes the number of times you need to assign permissions for objects.
Delegating Administrative Control of Objects • You can delegate administrative control of objects to individuals. • Use the Delegation Of Control wizard to delegate control of objects. • An administrator can delegate specific types of control. • The most common method of delegating control is to assign permissions at the OU level. • To delegate administrative control, you should try to follow specific guidelines. • You can access the Delegation Of Control wizard through the Active Directory Users And Computers snap-in.
Guidelines for Administering Active Directory Services • Coordinate Active Directory structure with other administrators. • Complete all attributes when creating objects. • Use deny permissions sparingly. • Ensure that at least one user has Full Control permission for each object. • Ensure that delegated users take responsibility and can be held accountable. • Provide training for users who control objects.