CSCI 233 Internet Protocols Class 8
570 likes | 748 Views
CSCI 233 Internet Protocols Class 8. David C. Roberts. Agenda. An Interesting Internet Product Remote Login Applications--TELNET File Transfer Applications—FTP, NFS Mail Applications—SMTP, POP, IMAP. New Product. Scanning Internet Camera Pans, zooms, produces Internet video

CSCI 233 Internet Protocols Class 8
E N D
Presentation Transcript
CSCI 233Internet ProtocolsClass 8 David C. Roberts
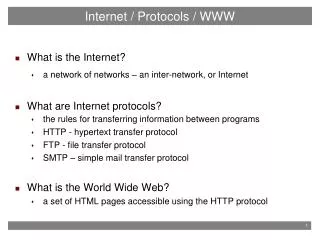
Agenda • An Interesting Internet Product • Remote Login Applications--TELNET • File Transfer Applications—FTP, NFS • Mail Applications—SMTP, POP, IMAP
New Product • Scanning Internet Camera • Pans, zooms, produces Internet video • Connects directly to the Internet • Doesn’t need a server
D-Link DCS-930L Wireless N Network CameraThe D-Link DCS-930L Wireless N Network Camera comes with everything you need to quickly add a surveillance camera to your home or small office network. It works right out of the box. Simply connect the cables, plug in the camera, run the short installation wizard and setup is complete. To view what the D-Link DCS-930L Wireless N Network Camera is seeing, simply log on to mydlink.com, choose your device, and start viewing - there is no need to configure your router to open up ports or remember hard-to-memorize Internet addresses. Order the D-Link DCS-930L Wireless N Network Camera today!
DDNS • What is DDNS? • How do you think it works?
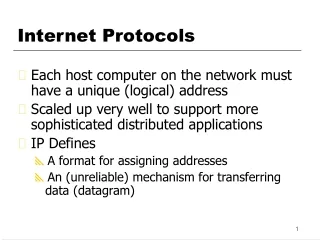
DDNS • Runs as DDNS server • Works with dynamic IP addresses • Software is added to host machine to provide IP address to DDNS at startup • DDNS service maps DDNS name to dynamic IP address
Uses of The Product • Monitor any space; just connect it to the Internet • Control, monitor the camera from anywhere you have Web access • Shows the power, capability of the dumb network that is available everywhere
Remote Login • TELNET is one of the Internet’s oldest protocols—defined in the 1960s • Each computer used to have a terminal wired to it to control it • Hard to control a large complex of computers, and lots more terminals than desired • TELNET allows user to establish login session on remote machine and execute commands • Client-server model can provide services to multiple machines • Using TCP, interactive use of remote machines can also be provided
TELNET Protocol • TELNET establishes TCP connection, passes keystrokes from user’s keyboard to the remote computer, brings back output to the user’s screen • Services: • Network virtual terminal—standard interface • Client and server negotiate options • Both ends of connection treated symmetrically
TELNET Virtual Server (NVT) • TELNET client translates from user terminal format into NVT format • Server translates NVT into local OS requirements
Current Uses • Today TELNET is used mostly within an installation for control of computer systems • Largely replaced for general use by end users for remote access to desktops • However, it’s the foundation of my ISP’s business!
Summary • High-level services provide important functionality to TCP/IP • TELNET is one of those services • TELNET provides a remote control console • Implemented across many operating systems
Methods for File Sharing • Remote file access • File transfer • Peer to peer
File Transfer Protocol • File transfer • Interactive access • Format specification • Authentication control
Process Model • Server allows concurrent access by multiple clients, using TCP/IP • Control and data transfer connections are (often) separate • Client and server usually each have separate processes for control, data transfer • Data transfer processes and connections are created and dropped as needed, but control connection persists during a session
FTP Port Number Assignment • Client uses random, locally determined port to connect to server • Client connects to port 21 at the server (a well-known port) • Client gets (another) unused local port number, connects to port 20 at server for data transfer connection • TELNET network virtual terminal protocol is used for the control connection; but only basic NVT definition.
Modes • Active mode: client sends the server the IP address and port number on which client will listen, and server initiates TCP connection. • Passive mode: (used if client is behind firewall and unable to accept incoming TCP connections) client sends a PASV command to the server and receives an IP address and port number in return. The client uses these to open the data connection to the server.
Representations • ASCII mode: for text. Data converted from the sending host's character representation to 8-bit ASCII before transmission, and to the receiving host's character representation. Inappropriate for files that contain data other than plain text. • Image (aka Binary) mode: sending machine sends each file byte for byte, and recipient stores the byte stream as received. • EBCDIC mode: use for plain text between hosts using IBM’s EBCDIC character set. This mode is otherwise like ASCII mode. • Local mode: Allows two computers with identical setups to send data in a proprietary format without the need to convert it to ASCII
Trivial File Transfer Protocol • Inexpensive, unsophisticated service • Simple file transfer, no authentication • Runs over any unreliable packet system • Sending side sends 512 byte file, waits for ACK for each block, then sends next one • First packet specifies the transfer • Block of less than 512 octets indicates end of file Question: Why would anyone use TFTP when there is also FTP?
NFS—Network File System • Originally developed by Sun Microsystems • Allows computer to access a remotely stored file over an IP network or the Internet
Peer to Peer File Sharing • No notion of clients and servers • “peer” nodes function as both client and server to one another • Foldershare uses peer-to-peer protocols Peer to peer Client-server
Types of Peer to Peer Networks • Structured: • Peers are organized following specific criteria and algorithms, which lead to overlays with specific topologies and properties. They typically use distributed hash table-based (DHT) indexing. • Unstructured: • No algorithm for organization or optimization of network connections • Pure peer-to-peer systems: entire network consists solely of equipotent peers. There is only one routing layer, as there are no preferred nodes with any special infrastructure function. • Hybrid peer-to-peer systems: may have infrastructure nodes to exist, often called supernodes. • Centralized peer-to-peer systems: central server is used for indexing functions and to bootstrap the entire system. Connections between peers are not determined by any algorithm. First prominent and popular peer-to-peer file sharing system, Napster, was centralized. Gnutella and Freenet are decentralized. model. Kazaa is hybrid.
Advantages of Peer to Peer • No single point of computer failure • No single point of network failure • No traffic congestion at servers • No need for high-capacity server • Uses available capacity of client machines
Disadvantages of Peer to Peer • Near-simultaneous updates of the same file can cause lots of network traffic • No guarantee of timeliness
Summary • Forms of access to remote files: • Whole-file copying • Shared on-line access • FTP uses whole-file copying, allows users to list directories as well as transfer files in either direction • TFTP provides a simple means for file transfer • NFS provides file system emulation • Peer to peer provides file transfer without servers, but with potential timeliness problems
Electronic Mail Email allows users to send memos across the Internet. • Notes can be short or quite large • Notes can have multiple attachments • Must work when remote machine is unreachable
Actors in the Email System • Post Office • SMTP servers move email between each other • SMTP servers store email for delivery to end users • Users • POP clients pick up email from SMTP servers • POP clients hand outgoing mail to SMTP servers
Delayed Delivery Sender and receiver do not need to be connected to the server at the same time
Internetworking and Email • TCP/IP internet makes universal delivery service possible • Mail systems built on TCP/IP are inherently reliable because of end-to-end delivery • Alternatively, mail gateways are used • Allow mail transfer between different systems • When gateway has a message, sender discards it Question: Is email through a gateway better or worse than a direct SMTP transfer?
TCP/IP Email Standards • Format and computer interaction are specified separately • Format: header, blank line, body • Body unspecified • Header is key word, colon, value • Some keywords required, others optional • Header is readable
Email Addresses local-part @ domain-name • domain-name: name of mail destination • local-part: address of a mailbox at destination Note: when gateways are employed, mail addresses are site-dependent
SMTP • Simple Mail Transport Protocol • Focuses on how mail delivery system passes messages from one machine to a server on another machine • Does not specify anything about user interface • Does not specify how mail is stored
Assured Delivery • SMTP server forms TCP/IP connection with receiving server • Once receiving server has put message into safe store, then it acknowledges and sender discards message • If SMTP can’t transfer message on the first try, it keeps trying • After several days of failure, SMTP reports failure to deliver.
SMTP Highlights • All communications is readable ASCII text • Transcript of interactions is readable • Each message is acknowledged separately • Addresses of the form local-part@domain-name
Example Transfer Client establishes connection Sent by server Sent by client S: 220 Beta.GOV SMPT ready C: HELO Alpha.EDU S: 20 Beta.GOV C: MAIL FROM: Smith@Alpha.EDU S: 250 OK C: RCPT TO: Green@Beta.GOV 550 No such user here RCPT TO: Brown@Beta.GOV 250 OK C: DATA S: 354 Start mail input;end with <CR><LF>.<CR><LF> C: ..sends body of mail message C: <CR><LF>.<CR><LF> S: 250 OK C: QUIT S: 221 Beta.GOV Service closing transmission channel
Mail Retrieval and Mailbox Manipulation • POP3—Post Office Protocol • POP3 client creates TCP connection to POP3 server on mailbox computer • Mailbox computer runs two servers: • SMTP to place mail into user mailboxes • POP3 server to allow user to extract messages from user mailbox • POP3 retrieves messages, deletes from user mailbox • Two servers must coordinate use of the user mailbox