Scenarios
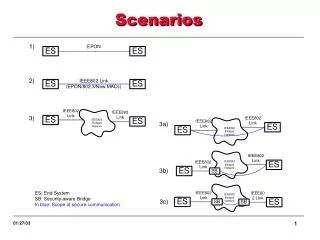
Scenarios. Business Applications. Scenario 1: Secure EPON FTTH/FTTB (provider network) Scenario 2: IEEE 802 Link Security RPR provider network? ??? Scenario 3: Secure Bridged Networks RPR enterprise networks? ???. Levels of Trust.

Scenarios
E N D
Presentation Transcript
Business Applications • Scenario 1: Secure EPON • FTTH/FTTB (provider network) • Scenario 2: IEEE 802 Link Security • RPR provider network? • ??? • Scenario 3: Secure Bridged Networks • RPR enterprise networks? • ???
Levels of Trust • Scenarios 3a, 3b and 3c depict different levels of trust of a network • In the absence of any SA (#3), all bridges are trusted • 3a) Implies the opposite (complete paranoia) • 3b) The ES’s trust exactly one SB (there may be other SB’s but the ES’s don’t trust them). • 3c) The left ES trusts the left SB and the right ES, the right SB. Neither ES trusts the SB furthest from it. SB’s trust each other, and they may be separated by a normal (security–unware) bridge B or an SB they don’t trust. • Different security approach depending on trust level
Classification of Scenarios • Classify scenarios by trust models (first cut): • Scenario T1: ES-EN-ES • Enterprise trust model • ES-EN links may be shared medium • Scenario T2: ES-PN-EN • Provider network in one Admin Domain • Scenario T3: ES-PN-EN • Provider network spans multiple Admin Domains • EPON ES-PN links or other shared media ES: End System EN: Enterprise Network PN: Provider Network
Unified Solution: Two Architecture Views? • Single-hop security associations • Basis of the solution is the link security • Secure Bridged network is designed as a (secure) sequence of secure links • Multi-hop security associations • A secure bridged network operates as a single end-to-end security association where end points may be secure bridges, not stations • Link security may be obtained by considering the link as the simplest form of a network • Combinations are possible
Single-hop SAs SA management is between contiguous “devices” (simple) L2 network infrastructure must be security-aware New infrastructure? Upgrade existing? What is the impact? Disadvantage: can’t support secure link layer between bridged stations separated by security-unaware bridges Multi-hop SAs No impact in the network infrastructure (transparent service) SA management is more complicated During SA establishment? After topology changes Restricted link protection Control and management frames may cannot be protected Is it needed? Special mechanisms can be added Factors