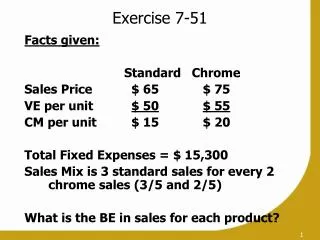
Exercise 7: TOR
Exercise 7: TOR. Daniel Compton, Auburn University. Overview. Tor Overview The Network Tor Hidden Services Tor Exercise: Exploring Tor Hidden Services Defeating Tor Countermeasures: Staying Anonymous Conclusion. Tor Overview.

Exercise 7: TOR
E N D
Presentation Transcript
Exercise 7: TOR Daniel Compton, Auburn University
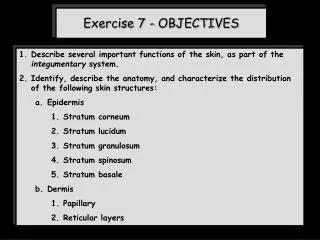
Overview • Tor Overview • The Network • Tor Hidden Services • Tor Exercise: Exploring Tor Hidden Services • Defeating Tor • Countermeasures: Staying Anonymous • Conclusion
Tor Overview • Tor (The Onion Router) is a system originally designed by the U.S. Naval Research Laboratory for protecting government communications. • Now in the public domain, Tor has evolved to become a free-to-use distributed, anonymous network. • Anyone can utilize Tor to anonymously browse the internet or anonymously host web-services (aka Tor Hidden Services).
Tor Overview: Hidden Services • Tor Hidden Services are web-services which are hosted anonymously on the Tor network. • Combined with the anonymous payment system bitcoin, Tor hidden services have recently been utilized to host digital black markets.
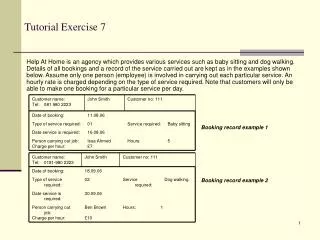
Accessing Tor: Exercise • We will use the Tor Browser Bundle -- a pre-packaged suite available for Windows/OSX/Linux • Freely available at: https://www.torproject.org/projects/torbrowser.html.en • This suite contains everything needed to route your web-traffic through the Tor network and to access Tor Hidden Services
Exercise Part 1: Running Tor • Browse to the “Tor Browser” folder and execute the “Start Tor Browser” shortcut. • After Execution, the “Vidalia Control Panel” should appear. • Once connected to the network (assuming network access) a browser window will open and confirm correct configuration.
Exercise Part 2: IP Comparison • To confirm that our home IP is indeed obscured, we go to google.com and search for “my ip.” • Subsequently, we compare the IP reported by google to that reported by an identical query made in a non-tor-enabled browser.
Exercise Part 3: Network Visualization • After ensuring that our home IP is obscured, we can explore the Tor network and browse anonymously online. • A visualization of the Tor network is provided by “View the Network” option in the Vidalia control panel.
Exercise Part 4: Network Visualization • A list of available Tor relays is displayed to the left of the world-map.
Exercise Part 5: Changing IP • Our apparent IP address can be changed at any time by clicking the “Use a New Identity” button on the Vidalia Control Panel. • Once our identity has been changed, traffic will be routed through a new exit-node and will therefore appear to originate from a different IP address.
Exercise Part 6: Tor Hidden Services • Tor Hidden services are accessed via a URL not unlike a normal web address (though less user-friendly) • Sites like “The Hidden Wiki” provide an index of hidden services. • Navigate your Tor-enabled browser to http://kpvz7ki2v5agwt35.onion/wiki/index.php/Main_Page WARNING: DO NOT CLICK ON RANDOM LINKS
Exercise Part 7: Tor Hidden Services • The Hidden Wiki provides links to commonly known Tor Hidden Services. The Commercial services section is especially interesting.
Defeating Tor • Tor does not protect traffic at the boundaries of the network. • “Bad Apple Attack” can reveal IP addresses of BitTorrent users on Tor • ESIEA (French School) claims attack capable of decrypting Tor network traffic via DDOS to redirect network traffic to malicious nodes and statistical attack against third encryption layer. • Possible to identify Hidden Services hosts by shutting off internet access to hosts via ISP cooperation.
Countermeasures: Stay Anonymous • How secure is Tor? • Very secure if used properly. • Most de-anonymization attacks are academic/impractical • How further anonymity is ensured • Utilize VPN at entry and exit to Tor network • Bounce traffic through botnet/busybox bounces • Don’t use home internet connection (e.g. use a coffee shop)
Conclusion • Tor provides easy way for masses to anonymize traffic • Tor hidden services allow individuals to host web-services without revealing their home IP • Ways to defeat Tor • How to stay anonymous in the wake of novel attacks against Tor