TOR
TOR. The Second-Generation Onion Router. About the Paper. This paper is one of few that shape the history because it was the origin of the Alpha version of TOR. Agenda. Overview The mechanism Goals and Assumptions Improvement to be done Attacks in mind and problems. To make life easier.

TOR
E N D
Presentation Transcript
TOR The Second-Generation Onion Router
About the Paper This paper is one of few that shape the history because it was the origin of the Alpha version of TOR
Agenda Overview The mechanism Goals and Assumptions Improvement to be done Attacks in mindand problems
To make life easier • Tor and Https security comparison: https://www.eff.org/pages/tor-and-https
Onion Routers A distributed overlay network designed to anonymize TCP-based applications like web browsing, secure shell (SSH), and instant messaging Client make a circuit consists of nodes and the data transferred in fixed size cells
Problems Onion Routing network was deployed briefly, the only long-running public implementation was a fragile proof-of-concept that ran on a single machine. Even this simple deployment processed connections from over 60,000 distinct IP addresses from all over the world at a rate of about 50,000 per day. But many critical design and deployment issues were never resolved, and the design has not been updated in years
The next Onion Router • Perfect forward secrecy • No central encryption management between node • Separation of “protocol cleaning” from anonymity • Use of SOCKS proxy interface • No mixing, padding, or traffic shaping (yet) • Many TCP streams can share one circuit • One circuit per user NOT per application • Leaky-pipe circuit topology • Congestion control • Decentralized • Directory servers • Trusted node act as a directory server • Variable exit policies • End-to-end integrity checking • Rendezvous points and hidden services
https://atlas.torproject.org/#details/350A0BD2E19CB579AFA07044CCE36AA745E0D4A1https://atlas.torproject.org/#details/350A0BD2E19CB579AFA07044CCE36AA745E0D4A1
Other Anonymity work • Mix-Net (1981) http://en.wikipedia.org/wiki/File:Decryption_mix_net.png
Other Anonymity work • Maximize Anonymity with High latency • Babel, Mix-Master and Mixminiom • Not proper for interactive activity • Less Anonymity with low Latency • Anonymizer, Java Anon Proxy, PipeNet • Tarzan, MorphMix are (P2P) • Crowds • These designs typically involve many packets that must, be delivered quickly, it is difficult for them to prevent an attacker who can eavesdrop both ends of the communication from correlating the timing and volume of traffic entering the anonymity network with traffic leaving it
Other Anonymity work • Complex Distributed-Trust Circuit Based • One or more bidirectional node • Data sent in fixed size cells • Tunneling by public key cryptography
Circuit Based Design • The protocol they used • Intercept IP Packet (L3) and rely them whole (change the source IP) like the Anonymizer. • This can handle any protocol • though these systems require kernel-level modifications to some operating systems, and so are more complex and less portable • Intercept TCP (L4) stream and then rely data in those streams ignoring the TCP segments (like TOR) • Application neutral • by treating application connections • as data streams rather than raw TCP packets, they avoid the inefficiencies of tunneling TCP over TCP. • Intercept Application Data (L7) like Crowd that receive the HTTP and then relays it by them self • Can utilize caching to limit the number of requests • Can batch or encode requests to minimize the number of connections
Attackers Distributed-trust anonymizing systems need to prevent attackers from adding too many servers and thus compromising user paths. Tor relies on a small set of well-known directory servers, run by independent parties, to decide which nodes can join. Tarzan and MorphMix allow unknown users to run servers, and use a limited resource (like IP addresses) to prevent an attacker from controlling too much of the network. Crowds suggests requiring written, notarized requests from potential crowd members.
NO Censorship Anonymous communication is essential for censorship resistant systems like Eternity [2], Free Haven [19], Publius[53], and Tangler [52]. Tor’s rendezvous points enable connections between mutually anonymous entities; they are a building block for location-hidden servers, which are needed by Eternity and Free Haven.
Goal To prevent linking communication partner (Mostly the location)
To Achieve this TOR Must • Deployability • In real world • Not expensive (BW for Volunteer) • Liability burden on operators (illegal activity over TOR) • Not difficult to implement (kernel modification or separate proxy for each protocol)
Relay Nodes As of the writing (2004), the network stands at 32 nodes spread over two continents In 2014 (yesterday) it is 5553 nodes http://torstatus.blutmagie.de/
To Achieve this TOR Must (2) • Usability • Hard-to-use system has fewer users • We need more user to increase the anonymity in the system (Hide user among users) • Easy to implement in all platform and use with already existed applications
To Achieve this TOR Must (3) • Flexibility • The protocol must be flexible and well specified, so Tor can serve as a test-bed for future research. • E.g. generating dummy traffic or preventing Sybil attacks • Simple design • Made it simple now with proven working technique • Tor aims to deploy a simple and stable system that integrates the best accepted approaches to protecting anonymity. • Not to handle any cost of complexity that threats out design
Not goal • Not peer-to-peer • Tarzan and MorphMix • Aim to scale to completely decentralized peer-to-peer environments with thousands of short-lived servers, many of which may be controlled by an adversary • Not secure against end-to-end attacks • Explicitly mentioned in their website, use (HTTPS) • Has been checked in the demo • No protocol normalization • Use Priovoxy • Not steganography • If you use TOR, they know you use it
Privoxy - Home Page “Privoxyis a non-caching web proxy with advanced filtering capabilities for enhancing privacy, modifying web page data and HTTP headers, controlling access, and removing ads and other obnoxious Internet junk. Privoxy has a flexible configuration and can be customized to suit individual needs and tastes. It has application for both stand-alone systems and multi-user networks.”
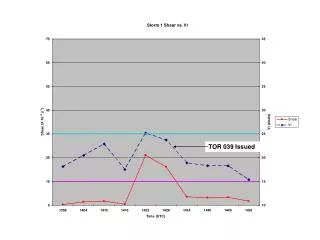
Globally Passive Adversary In US only
TOR The Tor network is an overlay network; each onion router (OR) runs as a normal user-level process without any special privileges Each onion router maintains a TLS connection to every other onion router These onion proxies accept TCP streams and multiplex them across the circuits. The onion router on the other side of the circuit connects to the requested destinations and relays data. 2 Type of Keys used (Short Term and long term keys) Medium term key also introduced (https://gitweb.torproject.org/torspec.git?a=blob_plain;hb=HEAD;f=tor-spec.txt)
Source :How Tor Work: https://www.youtube.com/watch?v=LAcGiLL4OZU
The Cells Traffic passes along these connections in fixed-size cells. Each cell is 512 bytes, consists of a header and a payload Control Cell Relay Cell
Circuits and Streams • In old Onion Routing, each TCP has a circuit • High cost form many TCP streams like Web browsing • In TOR, many streams can share one circuit, giving the user the ability to change the circuit periodically or automatically
Source :How Tor Work: https://www.youtube.com/watch?v=LAcGiLL4OZU
Other associated service • Integrity Checking on Stream • At edges • Better than the old one • Rate Limited and Fairness • Congestion Control • Circuit level Through ling • Hidden Service aaZaaAA
Other Design Decisions • DOD • As a public service • Flow control and rate limit • Expensive Cryptography (TLS half hand shake) • Disturb circuit (Individual users only) • TBA
Other Design Decisions 2 • Exit Policy abuse • Bad use of TOR exits • Specially for IP based authentication • Solution: Restricted Exit • Permit exit to world at large and forbid for certain known problematic services,, e.g. SMTP • Port restriction • OR rewrite the header to indicate it used an anonimous service
Other Design Decisions 3 • Directory Servers • In old days (Onion Router once) use flooding the status • Attacker to exploit the difference in client knowledge • Different Router have different view of link state and publish topology is not a good idea. • Flooding is expensive • Now, we have Trusted, Redundant Directory
Attack and Defense • Passive Attack • Observing user traffic pattern (eavesdropping on the services) • Like NSA in first slides • Observe User content • Mostly from hosted website • Or between end point and the responder • Option Distinguish • Likability • Traceability • End-to-end timing correlation • End-to-end size correlation • Website fingerprinting
Attack and Defense • Active Attacks • Compromise Key (TSL) • Iterate Compromise • Run a recipient • Run an onion proxy (OP) • DoS non-observed nodes • Run a hostile OR. • Introduce timing into messages • Tagging attacks • Replace contents of unauthenticated protocols • Replay attacks • Smear attacks • Distribute hostile code. • Directory Attack • Attack Against Rendezvous points