Malicious Hubs
Malicious Hubs. Sarah Jaffer. Malicious Hubs. PCs monitored by users Varying levels of security Autonomous Systems (AS) monitored by sysadmin Same security within a system Which is more valuable in a botnet?. Malicious Hubs. Some AS have poor security

Malicious Hubs
E N D
Presentation Transcript
Malicious Hubs Sarah Jaffer
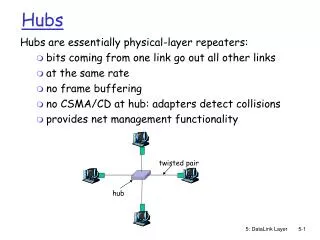
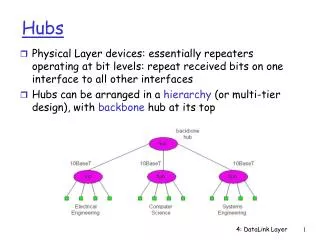
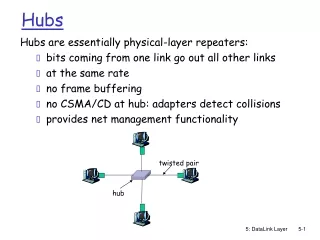
Malicious Hubs • PCs monitored by users • Varying levels of security • Autonomous Systems (AS) monitored by sysadmin • Same security within a system • Which is more valuable in a botnet?
Malicious Hubs • Some AS have poor security • If one machine can be infected, many can • Some may be criminal • Either way, these malicious hubs need to be shut down • First, need to be identified
Methodology • Aggregate blacklists of malicious IPs • Determine what AS (if any) they belong to • Longest prefix matching on IP • Evaluate AS using these statistics • Two methods
Method 1 • Ratio of malicious IP to total IP range • Total IP range is approximate • Blacklists may not have all malicious IPs • Wide variance in AS hostility • ~0.6% to 9.25% of IP range compromised
Method 2 • Percentage of each blacklist database comprised of each AS • Characterizes different AS tendency towards different activity • Most small: 0.25% to 1% • Few large: 7% to 10%
Conclusions • Methods identify AS which are either insecure or criminal • Enough evidence to hold them accountable? • How much do blacklists miss? • Other methods of evaluation?