Extending IBM Security Identity Manager
240 likes | 688 Views
Extending IBM Security Identity Manager. With StealthAUDIT for Data & A ccess Governance. STEALTHbits Technologies. Strong Management Team. Data & Access Governance Expertise. Strong & Growing Customer Base. Purpose-built automation platform Infrastructure-independent

Extending IBM Security Identity Manager
E N D
Presentation Transcript
Extending IBM Security Identity Manager With StealthAUDIT for Data & Access Governance
STEALTHbits Technologies StrongManagement Team Data & Access Governance Expertise Strong & Growing Customer Base • Purpose-built automation platform • Infrastructure-independent • Enterprise-Scale & Grade • Patented Technologies • Strong references & deployments • 7 of the top 10 Financial Services firms • 3 of the top 5 Property Insurance firms • 2 of the top 5 Pharmacy Service firms • Top 2 Telecommunications firms Strong Partner Ecosystem
Business Challenges • Access Sprawl • Joiners, Mover, Leaver Activity • Access Never thoroughly Reviewed/Adjusted • Distributed Entitlement Stores • Data Explosion • 80% of Data is Unstructured • 30-40% of that data is sensitive • Gartner predicts 650% increase in next 5 years • Big Data, Cloud, Virtualization, Mobility & Social • Risk Exposure on the Rise • Brand, Revenue & Reputation Exposure • Security Breach / Compliance Findings • Service Level Impacts
What does this really mean? • No Visibility into Effective Permissions • No Understanding of Data Ownership • No Common Access or Permission Standards • No Ability to Transform Groups or ACLs • No Ability to Automate Access Management
StealthAUDIT For Data & Access Governance
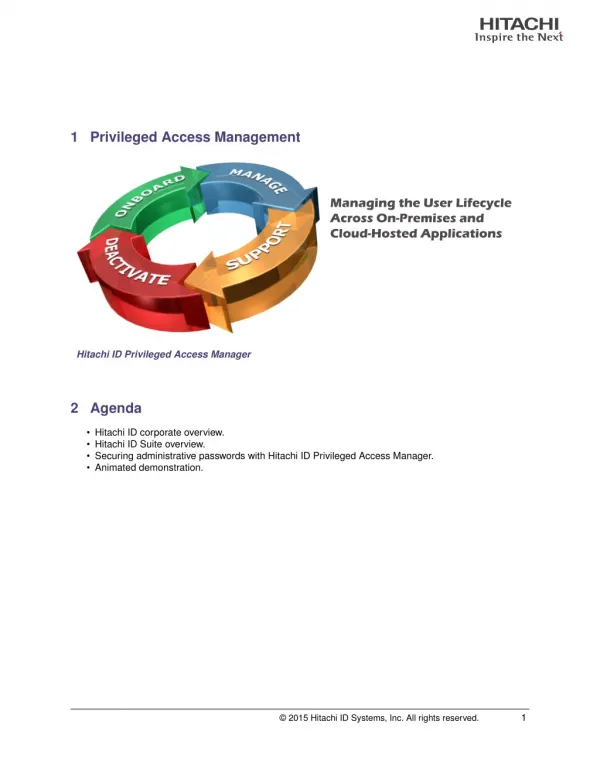
Holistically Safeguard Your Data and Access Who Has Access? What Are they Doing? How Do I Manage It? DISCOVER PRIORITIZE REMEDIATE StealthAUDIT Management Platform (SMP)
Access Governance Lifecycle Active Directory Cleanup Access Transformation M&A Migrations Open File Shares Unused Permissions Over-Provisioning IAM Integration Role Modeling IAM Policy Creation Identify Owners Entitlement Reviews Executive Oversight
How Can STEALTHbits Help IBM? • Differentiate IBM vs. Competition • New ISIM License Sales / Protect Renewals • Grow Upsell Opportunities • Expand Access to Security & Audit Stakeholders • More Revenue & Quicker Quota Retirement
What Can You Offer Your Clients? • Automated Access Governance For Unstructured Data • Request, Provision, Review, Revoke • Deliver the Right Access to the Right People • Who should have access and to what extent • Reduce Risk – satisfy Security & Compliance Need • Repeatable Security Practices, Fully Audited
Traditional IAM Platforms are Blind to Unstructured Data Directory Services Applications Databases SharePoint & Email File Systems
StealthAUDIT Eliminates the Blindspot! Discover the Unstructured Data Resources Correlate Access & Permissions Determine Resource Ownership Publish to ISIM PDB ADCD Virtual Entitlements Store Directory Services Applications Databases SharePoint & Email File Systems
Leverage Same Request Process for Unstructured Data! Approval Workflow Self-Service Access Request Access Granted via Security Group PDB ADCD Virtual Entitlements Store Directory Services Applications Databases SharePoint & Email File Systems
IBM Security Identity Manager & StealthAUDIT • Extend ISIM into Unstructured Data Governance • Drive New Revenue • Secure Renewals • Box Out the Competition • Capture Market Share!
Appendix: Steps to Publish to StealthAUDIT data to ISIM
Click Through For Summary of StealthAUDIT & ISIM Integration Begin Typing Resource Name, then click Next Select a Probable Owner/Reviewer Using the StealthAUDIT AIC, Click Manage Resource Ownership Click the Add Button Select Resource, Click Publish Search for, Request or Approve Access to published shares in ISIM Once Published, Click Close - Next, Login into ISIM to view published Resources Select Resource Based Groups, Click Finish Login with ISIM Credentials