Image Authentication Under Geometric Attacks Via Structure Matching
240 likes | 375 Views
http://signal.ece.utexas.edu. 2005 IEEE Int. Conference on Multimedia and Expo. Image Authentication Under Geometric Attacks Via Structure Matching. Vishal Monga, Divyanshu Vats and Brian L. Evans. July 6 th , 2005.

Image Authentication Under Geometric Attacks Via Structure Matching
E N D
Presentation Transcript
http://signal.ece.utexas.edu 2005 IEEE Int. Conference on Multimedia and Expo Image Authentication Under Geometric Attacks Via Structure Matching Vishal Monga, Divyanshu Vats and Brian L. Evans July 6th , 2005 Embedded Signal Processing LaboratoryThe University of Texas at AustinAustin, TX 78712-1084 USA {vishal, vats, bevans}@ece.utexas.edu
Introduction The Problem of Robust Image Authentication • Given an image • Make a binary decision on the authenticity of content • Content : defined (rather loosely) as the information conveyed by the image, e.g. one-bit change or small degradation in quality is NOT a content change • Robust authenticationsystem: required to tolerate incidental modifications yet be sensitive to content changes • Two classes of media verification methods • Watermarking: Look for pre-embedded information to determine authenticity of content • Digital Signatures: feature extraction; a significant change in the signature (image features) indicates a content change
Global Local Original Shearing Random bending Introduction Geometric Distortions or Attacks • Motivation to study geometric attacks • Vulnerability of classical watermarking/signature schemes • Loss of synchronization in watermarking • Classification of geometric distortions
Geometric distortion resistant watermarking Periodic insertion of the mark[Kalker et. al, 1999 ] [Kutter et. al, 1998 ] Template matching [Pun et. al, 1999 ] Geometrically invariant domains[Lin et. al, 2001], [Pun et. al, 2001] Feature point based tessellations[Baset. al, 2002] Related Work Related Work
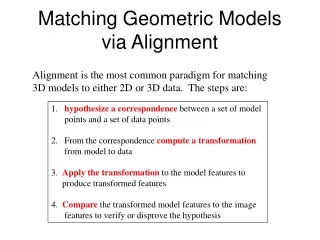
Proposed Framework Proposed Authentication Scheme Received Image • System components Visually significant feature extractor T: model of geometric distortion D(.,.) : robust distance measure Feature Extraction N Update T T(.) Reference Feature Points M Compute d = D(M, T(N)) d = dmin? No Yes • Natural constraints • 0 < ε < δ dmin > δ ? dmin< ε? No No Human intervention needed Yes Yes Credible Tampered
Feature Extraction Hypercomplex or End-Stopped Cells • Cells in visual cortex that help in object recognition • Respond strongly to line end-points, corners and points of high curvature [Hubel et al.,1965; Dobbins, 1989] • End-stopped wavelet basis [Vandergheynst et al., 2000] • Apply First Derivative of Gaussian (FDoG) operator to detect end-points of structures identified by Morlet wavelet Synthetic L-shaped image Morlet wavelet response End-stopped wavelet response
Feature Extraction Proposed Feature Detection Method • Compute wavelet transform of image I at suitably chosen scale i for several different orientations • Significant feature selection: Locations (x,y) in the image identified as candidate feature points satisfy • Avoid trivial (and fragile) features: Qualify location as final feature point if
H.D. = small Robust Distance Metric Distance Metric for Feature Set Comparison • Hausdorff distance between point sets M and N • M = {m1,…, mp} and N = {n1,…, nq} where h(M, N) is the directed Hausdorff distance • Why Hausdorff ? • Robust to small perturbations in feature points • Accounts for feature detector failure or occlusion
Distance Metric for feature comparison Is Hausdorff Distance that Robust? h(N, M) M N One outlier causes the distance to be large This is undesirable......
Distance Metric for feature comparison Solution: Define a Modified Distance • One possibility • Generalize as follows
Geometric Distortion Modeling Modeling the Geometric Distortion • Affine transformation defined as follows x = (x1, x2) , y = (y1, y2), R – 2 x 2 matrix, t – 2 x 1 vector
Authentication Authentication Procedure • Determine T* such that • Let • dmin < ε credible • dmin > δ tampered • Else human intervention needed • Search strategy based on structure matching [Rucklidge 1995] • Based on a “divide and conquer” rule
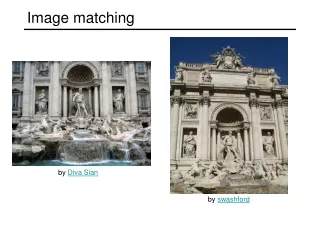
Results Results: Feature Extraction Original image JPEG with Quality Factor of 10 Rotation by 25 degrees Stirmark random bending
Results Quantitative Results • Feature set comparison If N isa transformed version of M otherwise Generalized Hausdorff distance between features of original and attacked (distorted) images Attacked images generated by Stirmark benchmark software
Security Via Randomization Randomized Feature Extraction • Randomization • Partition the image into N random (overlapping) regions • Random tiling varies significantly based on the secret key K, which is used as a seed to a (pseudo)-random number generator This yields a pseudo-random signal representation
Conclusion • Future work • Extensions to watermarking • More secure feature extraction • Faster transformation matching for applications to scalable image search problems • Highlights • Robust feature detector based on visually significant end-stopped wavelets • Hausdorff distance: accounts for feature detector failure or occlusion; generalized the distance to enhance robustness • Randomized feature extraction for security against intentional attacks
End-Stopped Wavelet Basis • Morlet wavelets [Antoine et al.,1996] • To detect linear (or curvilinear) structures having a specific orientation • End-stopped wavelet [Vandergheynst et al., 2000] • Apply First Derivative of Gaussian (FDoG) operator to detect end-points of structures identified by Morlet wavelet x – (x,y) 2-D spatial co-ordinates ko – (k0, k1) wave-vector of the mother wavelet Orientation control – Back
Feature Extraction Computing Wavelet Transform • Generalize end-stopped wavelet • Employ wavelet family • Scale parameter = 2, i – scale of the wavelet • Discretize orientation range [0, π] into M intervals i.e. • θk = (k π/M ), k = 0, 1, … M - 1 • End-stopped wavelet transform
Example Search Strategy: Example (-12,15) , (11,-10), (15,14) (15,12) , (-10,-11), (14,-14) transformation space
Solution: Data set normalization • Normalize data points in the following way • Why do normalization? • Preserves geometry of the points • Brings feature points to a common reference normalize
Digital Signature Techniques Relation Based Scheme : DCT coefficients • Discrete Cosine Transform (DCT) • Typically employed on 8 x 8 blocks • Digital Signature by Lin • Fp, Fq, DCT coefficients at the same positions in two different 8 x 8 blocks • , DCT coefficients in the compressed image 8 x 8 block p q N x N image Back
Conclusion Conclusion & Future Work • Decouple image hashing into • Feature extraction and data clustering • Feature point based hashing framework • Iterative feature detector that preserves significant image geometry, features invariant under several attacks • Trade-offs facilitated between hash algorithm goals • Clustering of image features [Monga, Banerjee & Evans, 2004] • Randomized clustering for secure image hashing • Future Work • Hashing under severe geometric attacks • Provably secure image hashing?
End-Stopped Wavelet Basis • Morlet wavelets [Antoine et al.,1996] • To detect linear (or curvilinear) structures having a specific orientation • End-stopped wavelet [Vandergheynst et al., 2000] • Apply First Derivative of Gaussian (FDoG) operator to detect end-points of structures identified by Morlet wavelet x – (x,y) 2-D spatial co-ordinates ko – (k0, k1) wave-vector of the mother wavelet Orientation control – Back