Service Discovery Proposal
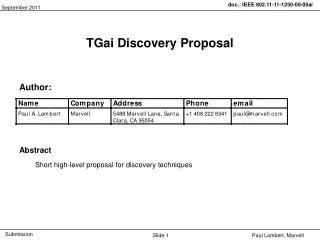
This proposal by Paul A. Lambert from Marvell Semiconductor outlines a framework for service discovery in IEEE 802.11 networks. It emphasizes the need for devices to identify and interact with services available within their vicinity, such as connecting to specific access points or applications. The document proposes the utilization of unique identifiers created through cryptographic hash functions, ensuring interoperability and facilitating the rapid growth of mobile applications. The proposed management frames for service discovery enhance network efficiency by allowing devices to discover and utilize services effectively.

Service Discovery Proposal
E N D
Presentation Transcript
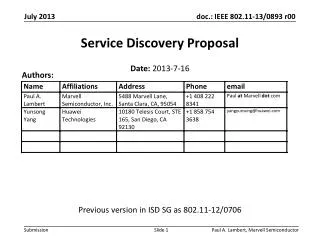
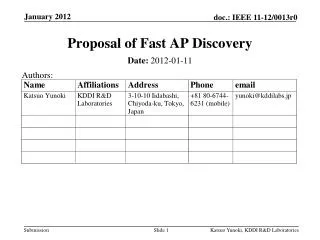
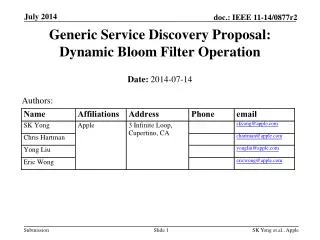
Service Discovery Proposal Authors: Date: 2013-7-16 Previous version in ISD SG as 802.11-12/0706 Paul A. Lambert, Marvell Semiconductor
For IEEE 802.11, knowledge of “services” supported by a device help in the selection of the appropriate STA/AP for subsequent communications • Examples might include: • Finding the right AP to connect to a print service • Finding a near-by WLAN supporting a particular application • Find a network (AP) with appropriate network connectivity and services for a particular set of applications • Find a AP/STA that can reach a particular application and user What is a Service? Paul Lambert, Marvell
What would this service discovery look like? Who has service “foo”? I have “foo” I have “bar” Paul Lambert, Marvell
There are many different existing ways to define application level services, possible examples include: UPnP, Bonjour, XML, OIDs, OUI fields, Bluetooth ids, URLS, Wi-Fi Alliance types (e.g. WFD), etc. Some of the above can be very large (e.g. UPnP) Many different organizations want to control and register identifiers to ensure interoperability (they want a single rooted hierarchy) Rapid growth of new mobile applications requires a simple process to ensure unique identification from many different organizations. More on “Services” Paul Lambert, Marvell
Most identifiers are made unique by creating hierarchies that are controlled by a central authority with sub branches delegated within a limited name space (e.g. DNS names and IANA) A powerful alternative is to define identifiers within a very large address space where the address space is so large that every identifier is guaranteed to a very high probability to be unique 16 octets can define a very large address space (2^128) to provide unique identifiers and is actually shorter in octets than most hierarchical naming schemes A hash function can be used to define a process for the creation of unique identifiers Mapping services to a unique identifier Very large set of possible identifiers. Used identifiers are a very small set within name space Paul Lambert, Marvell
A hash takes a block of data and returns a fixed size octet string such that any change in the data has a high probability of changing the hash value (aka digest) A “good’ cryptographic hash function has the property that it is infeasible to generate a message for a given hash Examples of well known cryptographic hash functions include: MD5, SHA-1, SHA-256 Cryptographic Hash Functions http://en.wikipedia.org/wiki/Cryptographic_hash_function Paul Lambert, Marvell
“Astronomy has long been humanity's go-to subject when it comes to contemplating the truly enormous. But actually, if 2128 is so much more vast than the number of stars in the observable universe (1015 times more vast*, or 4,000,000,000,000,000 in long-hand notation), then even the name "astronomical" is rather inadequate.” -- from Economist http://www.economist.com/blogs/johnson/2011/01/big_numbers Very Big Numbers Paul Lambert, Marvell
Process to define hash based identifiers Any group can get together and define a service Definition of “foo” service Definition of “bar” service Each service needs to define an appropriate string (text or octets) to define there service A cryptographic hash is used to create a unique identifier and may be a truncated version of the full hash Hash Function Hash Function “foo” Service Id “bar” Service Id Resulting identifiers are unique and any device that recognizes the identifier will have knowledge of it’s usage Paul Lambert, Marvell
Define Service Discovery frames as new IEEE 802.11 Management frame(s) of subtype Public Action. • Public Action frames carry opaque “Service Id” octet string(s) that are created as a hash of some application specific information that uniquely identifies a service. • For a Service Id, there may be an optional Service Capability field to provide service specific additional constraints • Service Discovery is performed by: • Service Discovery request/response sequence(request may be unicast or broadcast for a Service Id) • Service Announcement, a unsolicited broadcast/multicast of a Service Id • 46 bits of the Service Id can be used to create a multicast address for requests or announcements. • Service Discovery frames may be constructed to allow request or indication of more than one service, however limitations on the fields should constrain the size of the Service Id fields, Service Capability fields and total size of the Discovery Frames. Service Discovery Proposal Paul Lambert, Marvell
Unique Service Identifier –the first 128 bits of the SHA-256 hash of an octet string identifying the service (Service Name). Service Name – an octet string created by the developer of the service that provides a unique identification of the service. For unprotected services, the octet string is human readable. Service Id – An identifier formed by truncating a Unique Service Identifier. 6 octets (48 bits) is a convenient size for a Service Id in IEEE 802.11 applications. 46 bits is also an interesting size for a Service Id since it can be used as a multicast address. Definitions Paul Lambert, Marvell
Unique Service Identifier (USID) • 128 bits long (16 octets) is large enough to be statistically unique (3E+38) • is a type of “UUID”, a well defined construct in other standards activities Service Identifier (SID) • Provides a convenient short identifier (e.g. 6 octets) • May not always be unique, there may be collisions.Collisions, however, can be very rare for well selected sizes and collision impact can be mitigated • Multiple Service Identifiers can be created from the same Unique Service Identifier by taking different ranges for the truncation(e.g. First 6 octets, next 6 octets ...) Unique Service Identifiers vs. Service Identifiers Paul Lambert, Marvell
Multiple SIDs can be formed from the same USID and then used for discovery request versus discovery responses • E.g. SIDreq= 1st 6 octets of USID SIDrsp= 2nd 6 octets of USID • Same SID for req/rsp of 6 octets has 1 in 17 million collisions (2^24),Different Sid for req/rsp has 1 in 2.8 E+14 collision probability (2^48) -> much better • Different SiD for req/rsp has interesting privacy propertiesmore difficult to correlate req to rsp Secure SiDs can be created to form private groups • Secure USID = first 128 bits of SHA-256(f(Service Name and Group Key)) • Secure SID = truncation of Secure USID SIDs – Collisions and Security Paul Lambert, Marvell
Privacy is important • Wireless discovery exposes mobile users new risks • Adoption of service discovery in mobile devices will be handicapped if privacy features are not supported Protecting Service Discovery Service Name Protected Service Name i F(key,SN) GK i SHA-256 SHA-256 Hash (256 bits) Hash (256 bits) Truncate 128 Truncate 128 USID (128 bits) USID (128 bits) SID-req SID-rsp • SID obscured by group key SID-req SID-rsp Paul Lambert, Marvell