Internet Security
Internet Security Background on Internet technologies and protocols LANs and WANs IP Addressing, DNS OSI model TCP/IP, UDP Attacks Firewalls Background on Internet Technologies Evolution of Networking Batch Environment - 1950s

Internet Security
E N D
Presentation Transcript
Internet Security • Background on Internet technologies and protocols • LANs and WANs • IP Addressing, DNS • OSI model • TCP/IP, UDP • Attacks • Firewalls
Background on Internet Technologies • Evolution of Networking • Batch Environment - 1950s • no direct interaction between users and their programs during execution • Time Sharing - 1960s • dumb terminals were connected to a central computer system • Users were able to interact with the computer and could share its information processing resources • Marked the beginning of computer communications • Distributed Processing: use of minicomputers - 1970s • Users demanded computing closer to their work areas • Communication between neighbor processors and applications via networks • WAN and LAN- 1980s
LANs • collection of hosts connected by a high speed network • designed and developed for communications and resource sharing in a local work environment (room, campus, building) • users can access other networks via bridges and gateways PC 1 Printer PC 2 PC n File Server
WANs and Internetworks • span a large geographic area, cross public property • often based on services provided by 3rd party companies, use telephone networks for transmission from one node to another • can be used to connect several LANs together • Routers attached to each LAN filter the network traffic to and from the WAN • LANs can also be connected by special modems or dedicated leased lines Internetwork PC 1 Router PC 2 File Server PC n
Routers • Special purpose computers used for interconnecting networks • Essentially a router receives messages originating from one network and sends (routes) them to the other network • The process of selecting a network over which to send a message is called routing • Ex: computers X and Y can communicate via routers R1, R2 and R3
An example R1 x R2 R3 Y
Internet • The global Internet consists of thousands of computer networks interconnected by routers. • Internet appears as a single, seamless communication system to which many computers can attach. • each computer is assigned an address • any computer can send a message to any other computer
Transmission Capacity • Speed of transmission is measured in bits per second (bps) or cycles per second (Hertz) • Multiplexing: many signals can be sent on a single physical channel • Based on the physical medium • twisted wire pair, coaxial cable, fiber optic cable, satellite transmission, microwave • Dial-up access, Leased circuits, Cable modem, DSL technologies,Wireless access
Packet Switching • A message is not sent as a single unit, but broken down into small packets that are transmitted individually • Each packet has header that contains the info about source, destination and the packer number • Packets may travel on different routes • May even arrive the destination out of order • Good for data communication
Packet Switches • A WAN is constructed from many switches • A switch moves packets from one connection to the other • A switch is a dedicated computer, with two types of connections • High-speed connections with other switches; they can be: leased phone lines, optical fibers, microwave, satellite. • Low-speed connection: used to connect with an individual computer, or a LAN.
Switch Switch Switch Switched Network High speed connection
Internet2(http://www.internet2.edu/) • Is a high speed network that enables communications 100 - 1000 times faster than today’s internet • Rutgers, which is part of the Internet2 consortium, has launched RUNet 2000 ($100million) • Operates at 10Gbps (compare with the fastest modems now available ~Mbps) 15,000 times faster than a typical home broadband connection • Developed by academic and research community: more than 205 universities, NSF, NIH, NASA,.., IBM,DEC,Cisco, Sun, MCI, Sprint, .. • In Europe: European Union-funded network, TEN-34 was launched (initially 34Mbps, will later reach 155Mbps) • designed to provide a range of broadband network applications: collaborative research, distance learning, video-conferencing, remote medical consultation and diagnoses
Internet2 (cont’d) • Current telephone uses circuit switching where a piece of network entirely dedicated to a call • In contrast, information over Internet is broken down into small data packets, and the packets navigate from junction to junction (routers) • Aim of Internet2 is to install “gigapops” (gigabit capacity point of presence) capable of routing packets more quickly through the network (by launching a gigabit switch router to support speeds of 10Gbps) • With current Internet, real-time images have the same priority as email; Internet2 will be able to distinguish these two (Current IP is democratic) • Although Internet2 is being developed for universities and research labs, in next 5 years it may reach homes (for $30/month with 10Mbps)
IP Addressing • Every host on the Internet has a unique IP address. • IP protocol (the one in use now) has 32 bits for an address. How many hosts total? 232 = 4,294,987,296. • 32 bits must be divided into a Network portion and a Host portion. • Typically written in a "dotted decimal" form:128.6.10.4In this case, the network portion is 128.6The host portion is 10.4
IP Addressing (cont’d) • How to divide up the addresses ? Four Classes of IP addresses: • 1.Class A: First bit is 0, next 7 bits define the network, last 24 bits define the hosts. 128 networks with 16,777,216 hosts each. • 2.Class B: First two bits are 1 and 0, next 14 bits define the network, last 16 bits define the hosts. 16,384 networks with 65,536 hosts each. • 3.Class C: First three bits are 1 1 0, the next 21 bits define the network, last 8 bits define the host. 2,097,152 networks with 256 hosts each. • 4.Class D (Multicast): First three bits are 1 1 1, next 29 bits define a multicast address.
IP Addressing (cont’d) • For a network with a large number of hosts (e.g. Class B networks), we can divide the hosts into subnetworks using a subnet mask. • The subnet mask indicates which of the 32 bits should be considered the network portion and which should be considered the host portion. • A common subnet mask is: 255.255.255.0meaning the first 24 bits define the network and the last 8 bits define the host. • Special IP address: 127.0.0.1 called the "localhost"
Domain Name Services • Each host on the Internet has its own unique IP address - Who can remember all of them ? • DNS gives us a means to map an IP address to a "host name" and vice versa. • Host names are typically broken down into 4 or 5 parts: • 1.A geographic (e.g. country) designation is given at the "highest level": • uk us ca au fr it dr zw • 2.An organizational designation may be in place of geographic but can also appear in combination: • com edu gov mil org net • 3.The next level down in the "organizational" level: • rutgers microsoft pizzahut plannetreebok • 4.Within an organization, there may be several individual hosts, each with their own name: • CIMIC andromeda
Domain Name Services (cont’d) • These parts are assembled from right to left: • andromeda.rutgers.edu • www.microsoft.com • psych.leeds.ed.uk • www.whitehouse.gov • Resolving Internet Names using DNS • Most commonly used IP and host name pairs are kept in a hosts file. See /etc/hosts • If not in the hosts file, a primary DNS site is consulted. • UDP is used to send a DNS Query message to the designated Name Server on port 53. • This is done in a logical fashion. e.g. for host names ending in rutgers.edu, a local Rutgers DNS server can be queried.
Domain Name Services (cont’d) • If not found at a local DNS server, additional secondary DNS servers are checked until • 1.The connection times out or • 2.The request exceeds a predefined hop count • 3.The list of DNS servers is exhausted • Look at:/etc/resolv.conf on UNIX systems. In Windows, look at the properties of the TCP/IP protocol.
The Structure of WWW • A global collection of hypertext pages stored on Internet hosts. • Hypertext - Text documents that allow non-linear reading through hypertext links. • Normally we read a book in a linear fashion. Page 1, then Page 2, etc. • With hypertext, we follow our curiosity by skipping around the document(s) using hypertext links. • Hypertext is made up of three distinct parts: • Text Pages - The text you read. • Anchors - The starting point for a link. • Links - A pointer to another text page.
WWW(cont’d) • URL - Uniform Resource Locator. The address of a hypertext page or other Internet resource. • HTML - The HyperText Markup Language. The language used to create hypertext pages for use on the WWW. • WWW Browser - A program capable of displaying hypertext pages and navigating the WWW by allowing users to select hypertext links. Examples: • Netscape Navigator , NCSA Mosaic, Microsoft Internet Explorer, Mozilla • WWW Server - A daemon program (httpd) that responds to requests from a WWW Browser by sending it HTML hypertext pages.
The WWW Client/Server Model • WWW Servers are Servers • The request protocol used for WWW pages is HTTP - The HyperText Transfer Protocol. • 1.HTTP is an application layer protocol. • 2.Uses TCP/IP to make a connection. • 3.Issues a GET command. • 4.HTML Pages are returned. • Other protocols can also be used within a WWW Browser: • FTP - File Transfer Protocol • E-Mail • Telnet
URL’s • Uniform Resource Locators • A three part name for a WWW or Internet resource:protocol://hostname/filename • 1.Protocol: The application layer protocol used to access the resource. Examples: HTTP, FTP, GOPHER, MAILTO • 2.Host Name: The name of the host (or IP address) where the resource is located. • 3.File Name: The directory and file name of the resource. • URL Examples
Communication Architecture • Why do we need? • Communication systems involve heterogeneous technologies • change rapidly • they are complex (addressing, routing, multiplexing, error control, …) • How to cope with the above? • modularization • standardization • International Standards Organization (ISO) developed the Open Systems Interconnection (OSI) reference model (1974)
OSI Reference Model • Consists of seven layers • Each layer provides a set of functions to the layers above and relies on the functions provided by the layers below • Each layer communicates with its peer layer on the other node (protocols) • The layer boundaries (interfaces) should be designed in such a way as to minimize the information flow between the boundaries • The main idea is to have independent standards for different layers so that changes to one would not cause changes in other layers
OSI Reference Model (cont’d) +--------------+ +--------------+ | application |<--------------------->| application | +--------------+ +--------------+ | presentation |<--------------------->| presentation | +--------------+ +--------------+ | session |<--------------------->| session | +--------------+ +--------------+ | transport |<--------------------->| transport | +--------------+ +---------+ +--------------+ | network |<---->| network |<---->| network | +--------------+ +---------+ +--------------+ | data link |<---->|data link|<---->| data link | +--------------+ +---------+ +--------------+ | physical |<---->|physical |<---->| physical | +--------------+ +---------+ +--------------+
OSI Reference Model (cont’d) User A User B application presentation session transport network data link physical physical medium application presentation session transport network data link physical Higher level protocols Higher level protocols Lower level protocols Lower level protocols
Physical Layer • The physical layer defines electrical signaling on the transmission channel; how bits are converted into electrical current, light pulses or any other physical form • Specific functions • connection establishment and termination • encoding and transmission of bits • Repeating or amplification to increase the range of transmission
Data Link Layer • Specifies how to organize data into packets, and how to transmit packets over a network. For example, defined in this layer are: • maximum packet size, • format packet header, • checksum computation • Defines how the network layer packets are transmitted as bits • Examples of data link layer protocols • PPP (Point to Point Protocol) • Ethernet framing protocol • Bridges work at this layer only • Other functions • Framing and Error detection • transmission might get corrupted, bits may be lost (parity, checksum) • may lose connection • Flow control • may send data too fast for a modem • data might get delayed a long time in the network
The Network Layer • Specifies how addresses are formed (IP addresses) • How packets are forwarded (store and forward technique) • Delivers packets from sending computer to receiving computer (host-to-host) • Defines how information from the transport layer is sent over networks and how different hosts are addressed • Example of a network layer protocol: the Internet Protocol • Device that takes care of the network level functions is router or sometimes a gateway • Functions • Addressing: Determines which machine to send the packet to • Routing: Determines the best set of links • Congestion Control: Routes the packets via a different route if one intermediate node gets flooded with packets
The Transport Layer • Handles details of reliable transfer • format of acks, retransmission times, rules for changing it • Essentially, takes care of data transfer, ensuring the integrity of data if desired by the upper layers • Provides end-to-end delivery • Functions: • establishing and terminating connection • flow control • error detection and correction • multiplexing • TCP and UDP operate at this layer
The Session Layer • Specifies how to establish a communication with a remote system e.g.: telnet • authentication details; e.g.: passwords • Establishes and terminates connections and arranges sessions to logical parts • Provides a means of controlling the dialogue between two end users • Dialogue management (half versus full duplex) • Synchronization and recovery management • This layer is not often used in existing systems • TCP and RPC provide some functions at this layer
The Presentation Layer • Specifies how to represent data • Takes care of data type conversion • Different computers use different internal representation (Ex: ASCII, EBDIC) for integers and characters; • How to translate from one representation to another • An example of protocol residing at this layer: XDR (External Data Representation), which is used by RPC applications to provide interoperability between heterogeneous computer systems • Presentation layer functions are, in most systems, handled elsewhere in the network protocols
The Application Layer • Specifies how one particular application uses a network • Specifies request format (how to name a file) and how the application on another machine responds. • Defines the protocols to be used between the application programs • Examples of protocols at this layer are: protocols for electronic mail (e.g. SMTP), file transfer (e.g. FTP)and remote login,directory look up, http
How layered software works? • Each layer solves one part of the problem • To do so, each layer on the sending computer adds information to the outgoing data • The same layer in the receiving computer uses the additional information to process data (for example:checksums in data layer)
How layered software works? • Layering Principle: Layer N software on the destination computer, must receive the exact message sent by layer N software on the sending computer. • For example • if one layer adds a header, the corresponding layer has to remove it. • If one layer encrypts data, the receiving computer layer has to decrypt it.
Once Again, The purpose of Layers • Each layer can be: • Designed • Implemented • Tested independently of other layers. Each Layer can change and evolve independent of other layers
Applications • Electronic mail • File transfers (FTP) • Remote login (TELNET, rlogin) • Chat • Bulletin boards and Network News • Commerce • Network news • Networked information discovery and retrieval tools • Fax over the Internet • Games • ….
TCP/IP Protocol StackBasic protocols Layers 5-7 TELNET FTP SMTP HTTP ….. Layer 4 TCP UDP Layer 3 IP Layer 2 Ethernet Token-ring ATM PPP …..
TCP/IP Protocol StackInfrastructure and Security protocols Layers 5-7 TELNET FTP SMTP HTTP ….. DNS SSL RIP EGP BGP Layer 4 TCP UDP ICMP IPSEC Layer 3 IP ARP RARP Layer 2 Ethernet Token-ring ATM PPP ….. ICMP: Internet Control Message Protocol, ARP: Address Resolution Protocol RARP: Reverse Address Resolution Protocol, DNS: Domain Name Service RIP: Routing Information Protocol, BGP: Border Gateway Protocol EGP: External Gateway Protocol, SSL: Secure Socket Layer
TCP/IP(Transmission Control Protocol/Internet Protocol) • TCP/IP is the basic communication protocol of the Internet • Protocol: the special set of rules for communicating that the end points in a telecommunication connection use when they send signals back and forth. • TCP , IP , HTTP, FTP, and other protocols, each with defined set of rules to use with other Internet points relative to a defined set of capabilities.
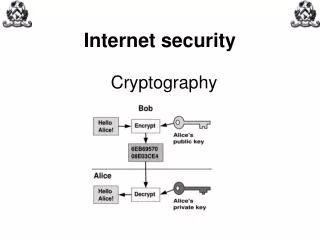
TCP/IP(Cont’d) • TCP: • manages the assembling of a message into packets that are transmitted over the Internet and received by a TCP layer that reassembles the packets into the original message. • A packet is the unit of data that is routed between an origin and a destination on the Internet or any other packet-switched network • IP • handles the address part of each packet so that it gets to the right destination.
TCP/IP(Cont’d) • Uses the client/server model of communication • Communication is primarily point-to-point: • Each communication is from one point (or host computer) in the network to another point or host. • Higher layer application protocols that use TCP/IP to get to the Internet • Hypertext Transfer Protocol (HTTP), File Transfer Protocol (FTP), Telnet (Telnet), and the Simple Mail Transfer Protocol (SMTP).
TCP • Adds Port Numbers, packet Sequence Numbers, Acknowledgement Numbers and other fields to IP addresses • A Port number refers to a specific application running on a host. e.g. SMTP uses Port 25 while Telnet uses Port 23. • TCP Header format • source port number • source IP address + source port number is a socket: uniquely identifies sender • destination port number • destination IP address + destination port number is a socket: uniquely identifies receiver • SYN, ACK flags • sequence number • acknowledgement number
TCP (cont’d) • Result is a TCP/IP "stream" - a connection established using handshake and error detection/control through positive acknowledgement. • Three-way handshake: • 1. A sends a SYN message to B - I'd like to set up a connection and I will start with sequence number s • 2. B Replies with a SYN and ACK message to A - Yes I will talk to you. • 3. A sends an ACK message to B along with the first piece of data - I got your ACK so here's the start of my data. SYN(A) initiator responder SYN(B),ACK(A) ACK(B)
TCP (cont’d) • Useful for when error correction is required and connection will last a long time (e.g. large data transfer). • Large data is broken into chunks and sent separately. Can arrive in any order. Discards duplicates. • Provides flow control.
User Datagram Protocol (UDP) • Adds Port Numbers to IP addresses • A Port number refers to a specific application running on a host. e.g. SMTP uses Port 25 while Telnet uses Port 23. • UPP header format • source port number • source IP address + source port number is a socket: uniquely identifies sender • destination port number • destination IP address + destination port number is a socket: uniquely identifies receiver • Also an optional Checksum - Error checking • No handshaking or error control • Also called a "Connectionless" protocol • Often referred to as "Unreliable" - meaning error control can't be relied upon. • Useful for situations where overhead is a concern. Small data requests such as queries, etc.
TCP/UDP Port Numbers and Services • TCP and UDP add Port Numbers to the IP addresses. • Each port corresponds to a specific application or service. • Ports 1 - 1024 are generally considered privileged ports. That is, on UNIX systems, one needs to have special permissions to run services on these ports. • Above 1024, any port number can be used. • Internet assigned numbers committee agrees on some standard port numbers.
TCP/UDP Port Numbers and Services (cont’d) • The following are some well known services and their assigned IP port numbers. • Service Port Protocol • Day Time 13 TCP/UDP • FTP 21 TCP • Telnet 23 TCP • SMTP Mail 25 TCP • DNS 53 UDP • HTTP/WWW 80 TCP