Internet Security
Internet Security By Abdiasis Mohamud What is Internet Security Internet security is the practice of protecting and preserving private resources and information on the Internet.

Internet Security
E N D
Presentation Transcript
Internet Security By Abdiasis Mohamud
What is Internet Security • Internet security is the practice of protecting and preserving private resources and information on the Internet. • Internet Security is keeping anyone from doing things you do not want them to do, with on or from your computers or any peripheral devices. • One of the Internet's key strengths is that no one agency or organization is responsible for its overall management, leaving it largely free of bureaucratic control and burdensome regulation. From a security standpoint, however, this could also be viewed as one of its weaknesses.
Types Of Protocols • TCP/IP- It’s the usual shorthand phrase for a collection of communications protocols. Originally developed by ARPANET. • IP- Packets are bundles of data from the foundation of TCP/IP protocol suite. • ARP- Works by sending out the an Ethernet broadcast packet containing the desired IP address. • TCP- Provides reliable virtual circuits to user processes. • UDP- Is used for large transmissions it tends to behave badly on network. Its easier to spoof UDP than TCP packets, since there’s no handshakes or sequence numbers.
Cont’d • ICMP- Its used to influence behavior of TCP and UDP connections. To report trouble with route and terminate connection because of network problems. • FTP- Supports the transmission and character set translation of text and binary files.
Internet Security Problems • Securing the web server and data that is on it • Securing Information that travels between the web and the user • Securing the end user’s computer and other devices that people use to access the Internet. • Business Integrity- Credit card security is one of the biggest issue of the Internet because the potential to literally create a world wide commerce opens a very large hole to credit card fraud. • Systems Disabled- Systems providing TCP-based services (WWW, email, newsgroup, gopher, etc ...) to the Internet community may be unable to provide those services while under a hacker's attack and for some time after the attack has ceased.
How Hackers Operate?? • Hacker-is programmer who hacks or reaches a goal by employing a series of modifications to exploit or extend existing code or resources gain unauthorized access through skill and tactics. • Password Cracking-are usually the first thing a hacker will try to "break" to gain access to your system. • Packet and password sniffing- Hackers have programs which do this, and then scan all the messages which traverse a network looking for passwords. • IP spoofing- Hacker sends a client request to the server using the source route. • Social Engineering- Phone, talk or Internet chat.
I need Security • Firewalls- is device that checks each packet against a list rules to permit or deny that transmission. • It a system designed to prevent unauthorized access to or from a private network. Firewalls can be implemented in both hardware and software or a combination of both. • Proxy Firewall- User runs an application, then the application connects to the firewall and logs in.
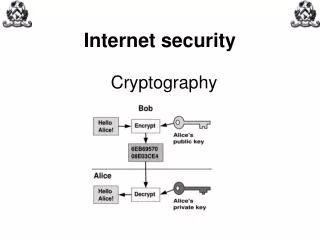
Cont’d • Encryption- Encryption is the transformation of data into a form unreadable by anyone without a secret decryption key. • Symmetric Encryption-It is a type of encryption where the same key is used to encrypt and decrypt the message. • Authentication- is a process whereby the receiver of a digital message can be confident of the identity of the sender and/or the integrity of the message. Its mechanism for users to change their passwords or obtain new passwords.
What Can You Do?? • Make sure network is guided against spoofing. • Secure your machines. • Make your password difficult, use Punctuations and characters.
References • Firewalls And Internet Security by William R. Cheswick and Steven M. Bellovin • Web Security by Simon Garfinkel and Gene Spafford. • Protect Your Privacy On The Internet, by Byran Bfaffenberger • http://www.nss.co.uk/WhitePapers/InternetSecurity.htm.