1 / 1
Lamport ’ s Scheme
50 likes | 270 Views
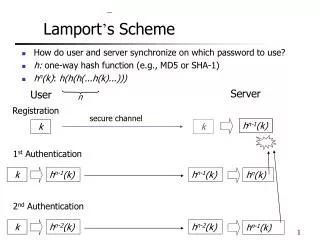
1 st Authentication. h n-1 (k). h n-1 (k). k. h n (k). 2 nd Authentication. h n-2 (k). h n-2 (k). k. h n-1 (k). Lamport ’ s Scheme. How do user and server synchronize on which password to use? h: one-way hash function (e.g., MD5 or SHA-1) h n (k) : h(h(h(...h(k)...))). Server.
Download Presentation 

Lamport ’ s Scheme
An Image/Link below is provided (as is) to download presentation
Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author.
Content is provided to you AS IS for your information and personal use only.
Download presentation by click this link.
While downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
During download, if you can't get a presentation, the file might be deleted by the publisher.
E N D
Presentation Transcript
1st Authentication hn-1(k) hn-1(k) k hn(k) 2nd Authentication hn-2(k) hn-2(k) k hn-1(k) Lamport’s Scheme • How do user and server synchronize on which password to use? • h: one-way hash function (e.g., MD5 or SHA-1) • hn(k): h(h(h(...h(k)...))) Server User n Registration secure channel hn-1(k) hn(k) k k
More Related