3 . Basic Static Analysis
E N D
Presentation Transcript
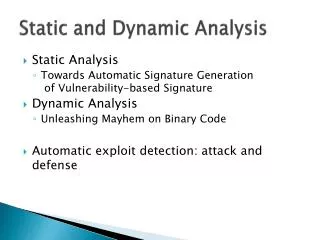
3. Basic Static Analysis Malware Analysis
What is Basic Static Analysis? • Static Analysis: Analyzing a program without executing it • Just review the code to determine the program behavior • It is usually the first step in malware analysis • Many tools exist to do the analysis • One has to choose the proper tool based on the objective • Some tools may execute the code – so, be careful • A combination of tools may be used
Hashing the file • It is a common method used to uniquely identify a malware • A hash function is a one-way function • Creates a unique signature for the file based on the binary content • Example functions: • md5sum (available in *nix platforms) • PowerShell or applications such as Cygwin (in Windows platforms) • SHA1, SHA2, … (Example command: shasum –a 256 <filename>) • May use online resources (be careful though!!)
Hashing on Turing • md5sum <filename> • Example:
Hashing with PowerShell • To open PowerShell • Windows + R (opens the Run window) • Type: powershell (and hit enter) • Enter the following • gci-Recurse | select FullName | %{get-Filehash -Algorithm md5 -Path $_.FullName ; get-FileHash -Algorithm sha1 -Path $_.FullName} | format-list • “gci -Recurse” grabs all items, plus child items from the working directory • “select FullName” returns the full item name • “get-Filehash -Algorithm md5” returns the md5 hash • “get-Filehash -Algorithm sha1” returns the sha1 hash • “format-list” prints it out neatly
Strings • What is a string? • A sequence of printable characters • There are mainly two formats used to store strings • ASCII and Unicode • The format defines how you can search for strings
Strings • What can we find? • Any string appearing in a program • Typical strings • Imports/Exports and other data about the program itself (i.e. artifacts from the file format – such as PE file information) • Messages • IPs, domain names and other command and control information
Strings • If you don’t find any strings, that is still useful information • Indicates that the program may be packed or obfuscated • Adjust your approach – first figure out if you can unpack/deobfuscate the sample, then search for strings
Running “strings” command on Turing Random data Valid string
Anti-Virus (AV) Software • They are effective and prevalent • Usually a good place to start • Should use multiple scanners • If one did not identify, another one may • AVs rely on database of identifiable suspicious code (file signature) • Some use pattern-matching / behavioral analysis • Malware authors can modify the code to avoid detection
AV: VirusTotal • A web service that analyzes malware • Utilizes file signatures and heuristics • It compares its results with those of numerous antivirus databases • It also provides: • Basic Properties • Hashing, File Size • History • First/Last Submission • File Names • Packer Detection
AV: ClamAV • It is an open-source AV engine • It performs Email scanning, web scanning, end-point security • Available at clamav.net • On *nix platforms use: apt-get install • Freshclam: allows updates from command line • Clamscan: Command line AV scanner • You can also write custom signatures for detection
AV: ClamAV • Distributed with several CVD files • Archive of signature files • Main.cvd and daily.cvd • A group of files that contain information/signatures that Clam uses to match files • To unpack a CVD file to view its contents: • $ sudosigtool –u daily.cvd
AV: ClamAV Signature Formats • Hash-based signatures • Easiest way to create a signature for ClamAV • Create file hash checksums • Only used against static malware – i.e. it doesn’t change • Database uses .hdb extension
AV: ClamAV – Creating Hash Signatures • Create/identify a file that you want detected by ClamAV • Generate a hash using sigtool: $ sigtool--md5 <file> • Create a HDB: $ sigtool--md5 <file> >test.hdb • Scan with ClamAV: $ clamscan-d test.hdba.out • Also supports SHA1 and SHA256 signatures • Same format, engine differentiates by hash length
AV: ClamAV – Body-based Signatures • Example: “Hi There” • Create ASCII-based signature based off custom EXE • Use sigtool with --hex-dump to generate hex • Example: sigtool --hex-dump Hi There Input Output 5ui89juy4kd9lka98t50a (not correct output, just randomly picked) • The last two characters in the output will be the newline code – so, ignore those.
AV: ClamAV – Body-based Signatures • Example continued • Build a properly formatted signature and store in a file with .ndbextension • SigName:Target:Offset:HexadecimalSignature • Example: MySignature:0:*: 5ui89juy4kd9lka98t5 • Notice that “0a”, the newline code is removed from the signature • SigName = Malware Name • Target = 0 any file, 1 PE, 2 OLE2, 3 HTML … • Offset: Range of bytes to match in • Hex Signature
AV: ClamAV – Body-based Signatures • To use custom signatures, store them in a file with .ndbextension • $ clamscan-d custom_db.ndbfile_name • Make use of wildcards in your signature to increase detection rate • ??: wildcard for a single byte value 0 - FF • *: traditional wildcard, much broader (match any number of bytes)