Field-Level Security View - Concealing Sensitive Data from Unauthorized Users
90 likes | 115 Views
This view allows administrators to conceal sensitive field data and entire records based on in-data conditions, ensuring restricted access and confidentiality. It offers quick and easy modification of user profiles and precise field and record restrictions.

Field-Level Security View - Concealing Sensitive Data from Unauthorized Users
E N D
Presentation Transcript
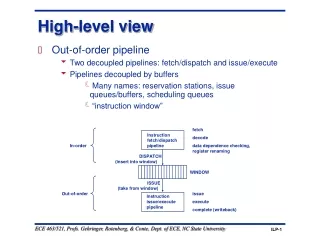
View Record and Field-LevelSecurity
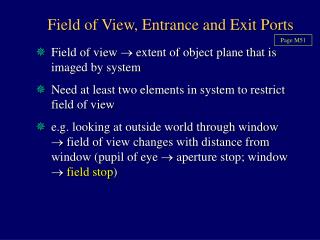
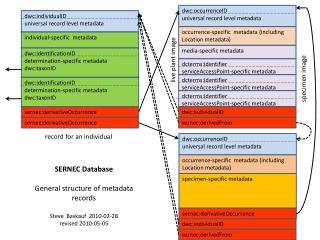
View – Database Environment Conceals sensitive field data from unauthorized users, with no modifications to existing applications Conceals entire records based upon numerous in-data conditions Allows administrators to restrict fields/records to selected users Quick, easy modification of user and user-group profiles Defining file and field restrictions is a snap
Application Data Entry Screens As Seen by Restricted Users As Seen by Authorized Users
Sample View Application (2/2) Sensitive data in the “Contact person” and “Credit” fields are hidden…
Thank You! Please visit us at www.razlee.com