TESTA II Network Security
Explore the comprehensive network security measures implemented by Global One Communications to safeguard corporate data and infrastructure. Learn about backbone security, access network security, VPN services, and security management practices.

TESTA II Network Security
E N D
Presentation Transcript
TESTA II Network Security June 06, 2000 Global One Communications Christian Sinephro email: christian.sinephro@globalone.net
Contents • Overview • Corporate Security • TESTA II Network Security • Backbone Security • Access Network Security • Global Dial Access Security • Additional Security Options • Security Management
Overview • Corporate Security Policy • IP VPN using MPLS - No Internet traffic • Physical control and security on the backbone • Controlled access to the EuroGate • Logical segregation of customer traffic based on strong routing protocol (port configuration) • Central Management (NMC) of the VPN configuration - No third-party access or delegation of network management function
Corporate Security • Key elements of the Corporate Security policy are: • comprehensive staff screening • Physical security for network nodes and Operations support systems, with access to limited staff on a need-to-know basis • Password and user ID for network nodes and support systems, including enabling auditing features • Documentation of specific security procedures and processes • Continued review of security procedures as an inherent element of network operations. • Security Architecture focused on: • Securing network infrastructure to avoid network service disruption • Preventing and detecting fraud and abuse of Global One network services • Implementing overlay services to enhance the implementation of specific security policies
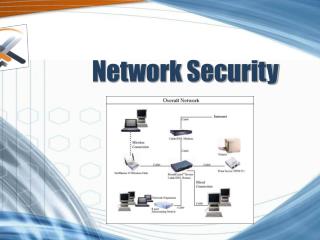
TESTA II Network Security • Backbone Security • Backbone node infrastructure • Access Network Security • Quality of Service • Service level guarantees (e.g. availability) • Classes of Service • Security Management • Corporate security • Security Management
LocalDomain D LocalDomain C EuroGate EuroGate EuroDomain EuroGate EuroGate LocalDomain B LocalDomain A TESTA II Network Security Backbone Security Layer “Door-to-Door” Security “Door-to-Door” Security Backbone Security
Backbone Security • Fiber - secure Transmission Medium: • Backbone Transmission security on fiber optic links (backhaul route diversity, secure cable routing, heavy armoring, ..) • Impervious to radio frequency and electromagnetic interference • Access Management and Control: • All network equipment locations protected with access alarms • Alarms monitored continuously by Regional Control centres (NMCs) • Network Monitoring: • Real-time status and remote software control of switching & transmission • Remote diagnostic tools for adding, deleting or modifying circuits or viewing port condition • Only registered operators, with appropriate administrator functions, have access to NMC tools and systems. • External Protection • Denial of service attack: only LD users can access the EuroDomain • Tracking and support can be provided
Access Network Security • Local Loops: • Ordered by Global One and currently provided by local Telecom Operators • In some countries, alternative carriers can be used • Security is the currently accepted level of security on the local loop • Customer Premises Equipment: • Provided and managed by Global One under an onsite Rental and maintenance contract. • Only Global One has access to the router configuration.
Global Dial Access Security TESTA II EuroDomain Access Server Home Gateway VPDN Tunnel Application Host TESTA II Dial-up User AAA Server
Global Dial Access Security • Only registered users have access to the Dial Access service • User Authentication via AAA server (Radius) based on the Network Access Identifier • Additional SecurID client can be used for strong authentication • Limits access to pre-defined resources on the TESTA II backbone • Performs user accounting for purposes of security and charge back
Additional Security Options • Firewalling • Managed firewall service at site location • Optional network-based firewall • Dedicated secure IP VPN boxes performing: • Authentication (Remote keys) • Encryption (ITSEC) • Firewalling functions • Access Filtering • Restricted VPN configurations on the TESTA II backbone
Security Management • Corporate Security Department responsible for: • Performing threat analysis • Conducting surveillance and detection services • Recommending overall solutions to security issues • Protecting management systems and applications