Network Security
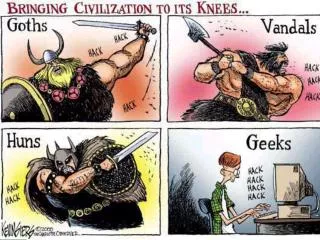
Network Security. The only safe computer is a dead computer (or at least a disconnected one) Security is about balancing the usefulness and the potential abuse of the network and the information therein

Network Security
E N D
Presentation Transcript
Network Security • The only safe computer is a dead computer (or at least a disconnected one) • Security is about balancing the usefulness and the potential abuse of the network and the information therein • The degree of security depends on the type of information you have (although ALL networks require a certain minimum of security measures)
Network Security • Specific threats are: • Unauthorized access to hosts (both clients and servers) via the net • Hackers and Crackers trying to get in and steal or ruin things • Unintended disclosure or modification of data sent between hosts • Interception in transit • Denial of service attacks against connected hosts • Flooding you with traffic so that legitimate customers cannot gain access
General Strategies • Encrypting sensitive data sent between hosts • Reducing the size of the target by disabling unneeded services • Putting obstacles between the attacker and the target systems • obstacles such as firewalls, but also passwords for logon and for access to highly secure data files
Types of Attacks • Attacks can be in many forms: • Denial of Service Attacks • Computer Viruses • Trojan Horse Programs
Denial of Service Attacks • Denial-of-service attacks come in a variety of forms and aim at a variety of services. There are three basic types of attack: • Consumption of scarce, limited, or non-renewable resources • Destruction or alteration of configuration information • Physical destruction or alteration of network components
Denial of Service Attacks • Consumption of Scarce Resources • Network Connectivity • In this type of attack, the attacker begins the process of establishing a connection to the victim machine, but does it in such a way as to prevent the ultimate completion of the connection. In the meantime, the victim machine has reserved one of a limited number of data structures required to complete the impending connection. The result is that legitimate connections are denied while the victim machine is waiting to complete bogus "half-open" connections. • Using Your Own Resources Against You • In this attack, the intruder uses forged packets to connect the echo service on one machine to the chargen service on another machine. The result is that the two services consume all available network bandwidth between them.
Denial of Service Attacks • Consumption of Scarce Resources • Bandwidth Consumption • An intruder may also be able to consume all the available bandwidth on your network by generating a large number of packets directed to your network. Typically, these packets are ICMP ECHO packets, but in principle they may be anything. Further, the intruder need not be operating from a single machine; he may be able to coordinate or co-opt several machines on different networks to achieve the same effect • Consumption of Other Resources • For example, in many systems, a limited number of data structures are available to hold process information (process identifiers, process table entries, process slots, etc.). An intruder may be able to consume these data structures by writing a simple program or script that does nothing but repeatedly create copies of itself.
Denial of Service Attacks • Destruction or alteration of configuration information • An improperly configured computer may not perform well or may not operate at all. An intruder may be able to alter or destroy configuration information that prevents you from using your computer or network. • For example, if an intruder can change the routing information in your routers, your network may be disabled. If an intruder is able to modify the registry on a Windows NT machine, certain functions may be unavailable.
Denial of Service Attacks • physical destruction or alteration of network components • The primary concern with this type of attack is physical security. You should guard against unauthorized access to computers, routers, network wiring closets, network backbone segments, power and cooling stations, and any other critical components of your network.
Computer Viruses • A virus is a small piece of software that piggybacks on real programs • Computer viruses such as the Melissa(1999), ‘I Love You’(2000), MSBlaster (2003), So Big (2003) virus are executable files designed to replicate themselves and avoid detection. • A virus may try to avoid detection by disguising itself as a legitimate program. • There are over 15000 known viruses, and new virus strains continue to show up regularly. The rate of virus infection is also increasing.
Computer Viruses • There are two types of computer viruses: • Boot-sector viruses • File-infecting viruses • Trojan horse programs are another hazard out there.
Viruses • Executable programs that attach to the Host computer. • They can propagate via shared floppies or other media and need a host program in order to propagate. • They can be very harmful, they may damage your system.
Macro Virus • Macro: Computer Program that executes in response to a specific combination of keystrokes or clicking a particular icon. • Macros are normally written in Word, Excel, Access, etc. • Macro Virus is written inside a Macro. • Infects Microsoft office (Specially MS Word).
Boot-sector viruses • When a computer boots (or starts), it looks to the boot sector of the hard disk before loading the operating system or any other startup files. • A boot-sector virus is designed to replace the information in the hard disk's boot sectors with its own code. • When a computer is infected with a boot-sector virus, the virus' code is read into memory before anything else. • Once the virus is in memory, it can replicate itself onto any other disks that are used in the infected computer.
File-infecting viruses • This is the most common type of virus. • A file-infecting virus attaches itself to an executable program file by adding its own code to the executable file. • The virus code is usually added such that it escapes detection. • When the infected file is run, the virus can attach itself to other executable files. • Files infected by this type of virus usually have a .COM, .EXE, or .SYS extension.
Trojan horse programs • A Trojan horse program is not a virus. • The key distinction between a virus and a Trojan horse program is that a Trojan horse program does not replicate itself; it only destroys information on the hard disk. • A Trojan horse program disguises itself as a legitimate program such as a game or utility. • Back Orifice, The Aids Information, Twelve Tricks A and B, and Darth Vader programs are examples of Trojan horse programs.
Trojan horse programs • A Trojan horse program often looks and initially acts like a legitimate program, but once it is executed, it can destroy or scramble data. • A Trojan horse program can contain viruses, but is not a virus itself.
Acceptable Use Policies • A policy that outlines appropriate use of the Internet and that is enforced by the System Administrator. • You are expected to know your AUP and any of its restrictions that apply to your online activities.
Password Security • Your First line of defense against all kinds of mischief and misery is your password. • System Administrator will never need your password. • No matter what someone tells you, don’t give out your password.
Password Security • Creating Passwords: • A good password should contain the following: • At least 6-8 characters. • “UPPER” and “lower” case characters. • A good mixture of alphanumeric characters • E.g., 0xfF&p • Create passwords that are not found in the English dictionary. • There are software programs that would go about guessing these passwords. • Change the password very often.
Safeguards Against Viruses … • Use Antivirus Software • E.g., Mcafee or Norton Antivirus. • If you might have to disable Antivirus software while you are installing any software on your computer. • Update Antivirus software regularly. • Update the “Virus Signature” files.
Safeguards Against Viruses … • Keep Floppy diskettes out of your floppy drives. • Boot sector viruses may infect the floppy disk. • A typical scenario is to receive a diskette from an innocent source that contains a boot disk virus. When your operating system is running, files on the diskette can be read without triggering the boot disk virus. However, if you leave the diskette in the drive, and then turn the computer off or reload the operating system, the computer will look first in your A drive, find the diskette with its boot disk virus, load it, and make it temporarily impossible to use your hard disk.
Safeguards Against Viruses … • Encrypt Files • Encrypt files that may contain sensitive information. • Encryption: • Conversion of data into a form, that cannot be easily understood by unauthorized people. • Decryption: • Process of converting encrypted data back into its original form, so it can be understood.
Safeguards Against Viruses … • Don’t leave your computer connected to the Internet. • Disconnect whenever you don’t need to use the internet. • The longer your stay on the internet, the easier it is for people to break into your system.
Shopping Online • Using credit cards is safer than using personal checks or money orders. • When confidential information; such as, Credit card numbers, SS#, etc, make sure the site is secure. • You can find out if the site is secure or not by checking the padlock icon or if the site address begins with “https” as compared to “http”. • https: “s” stands for secure. • Although a web page may be secure, but you don’t have any idea about how secure the computers are that saves your personal information.
Firewall • Firewall: • A collection of Hardware, Software and corporate policies that protects a LAN from the Internet. • A Firewall is intended to do the following: • Restrict unauthorized users • Retain control of private information • Prevent unauthorized export of proprietary information. • A firewall controls access to your private network.
Defending Your Computer • Some steps to defend your computer: • Antivirus Software • Personal Firewalls • Internet Explorer Security Levels
Antivirus Software • Identifies and removes viruses from your computer. • You have to update virus “Signatures” on a regular basis. • www.mcafee.com • www.symantec.com • Normally Antivirus software isn’t installed as a part of your Operating System.
Antivirus Software • Using Antivirus software isn’t effective, unless you follow some basic rules: • Install Antivirus Software • Update Antivirus Software regularly • Scan your hard drives regularly • Scan Floppy disks • Scan every executable attachment • Beware of unknown mail senders • Keep your IT department informed
Personal Firewalls • If you have a direct connection for your home computer, considering installing a personal firewall. • A personal firewall is a smaller, inexpensive version of full scale firewall that is used on corporate networks.
Personal Firewalls (Continued) • Software Based Personal Firewall: • A program that is installed on a user’s computer. • Software can perform packet filtering. • Some companies that sell personal firewalls are: • McAfee Personal Firewall www.mcafee.com • Norton Internet Security www.symantec.com
Personal Firewalls (Continued) • Hardware Based Personal Firewalls: • Home users may consider hardware based firewalls for added security. • They are also known as Broadband Routers
Configuring Browser Security • Web browsers have their own security features. • Netscape Navigator offers a security button on the toolbar to immediately determine whether a site is secure. • Microsoft Internet Explorer (MSIE) offers safety levels to stop potentially dangerous material from downloading to your computer.
Cookies • Cookies: • Small text files places on client’s computer, so web site managers can gain marketing information about their visitors. • Cookies are not harmful to a computer. • It is difficult for a cookie to contain executable virus or worm program.
Cookies • If users configure their browsers to allow cookie download, then each time a user revisits that site, the user’s computer will send the cookie to the web server. • Cookies are stored in a specific directory • Depending on the browser security settings, the browser may warn the user before downloading the cookie. • Some personal firewalls can also manage which cookies should be saved on your computer.
Spyware removal • SpyBot