Botnet Dection system
Botnet Dection system. Introduction. Botnet problem Challenges for botnet detection. What Is a Bot/Botnet?. Bot A malware instance that runs autonomously and automatically on a compromised computer (zombie) without owner’s consent Profit-driven, professionally written, widely propagated

Botnet Dection system
E N D
Presentation Transcript
Introduction • Botnet problem • Challenges for botnet detection
What Is a Bot/Botnet? • Bot • A malware instance that runs autonomously and automatically on a compromised computer (zombie) without owner’s consent • Profit-driven, professionally written, widely propagated • Botnet (Bot Army): network of bots controlled by criminals • Definition: “A coordinated group of malware instances that are controlled by a botmaster via some C&C channel” • Architecture: centralized (e.g., IRC,HTTP), distributed (e.g., P2P) • “25% of Internet PCs are part of a botnet!” ( - Vint Cerf)
Botnets are used for … • All DDoS attacks • Spam • Click fraud • Information theft • Phishing attacks • Distributing other malware, e.g., spywarePCs are part of a botnet!” ( - Vint Cerf)
Challenges for Botnet Detection • Bots are stealthy on the infected machines – We focus on a network-based solution • Bot infection is usually a multi-faceted and multiphased process – Only looking at one specific aspect likely to fail • Bots are dynamically evolving – Static and signature-based approaches may not be effective • Botnets can have very flexible design of C&C channels – A solution very specific to a botnet instance is not desirable
Roadmap to three Detection Systems • Bothunter: regardless of the C&C structure and network protocol, if they follow pre-defined infection live cycle • Botsniffer:works for IRC and http, can be extended to detect centralized C&C botnets • Botminer:independent of the protocol and structure
BotHunter system-detection on single infected client • Detecting Malware Infection ThroughIDS-Driven Dialog Correlation • Monitors two-way communication flows between internal networks and the Internet for signs of bot and other malware • Correlates dialog trail of inbound intrusion alarms with outbound communication patterns
Dialog-based Correlation • BotHunter employs an Infection Lifecycle Model to detect host infection behavior
Evaluation • Example: http://www.cyber-ta.org/releases/malware-analysis/public/2009-01-13-public/
BotSniffer-detection on centralized C&C botnets(IRC,HTTP) • WHY we will focus on C&C? • C&C is essential to a botnet – Without C&C, bots are just discrete, unorganized infections • C&C detection is important – Relatively stable and unlikely to change within botnets – Reveal C&C server and local victims – The weakest link
Correlation Engine • Based on two properties • Response crowd – a set of clients that have (message/activity) response behavior -A Dense response crowd: the fraction of clients with message/activity behavior within the group is larger than a threshold (e.g., 0.5). • A homogeneous response crowd – Many members have very similar responses
Why Botminer? • Botnets can change their C&C content (encryption, etc.), protocols (IRC, HTTP, etc.),structures (P2P, etc.), C&C servers, dialog models • So bothunter, botsniffer systems may be evaded. We need to consider more
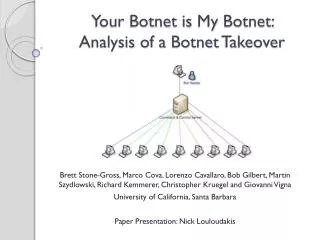
Revisit Botnet Definition • “A coordinated group of malware instances that are controlled by a botmaster via some C&C channel” • We need to monitor two planes – C-plane (C&C communication plane): “who is talking to whom” – A-plane (malicious activity plane): “who is doing what”
C-Plane clustering • What characterizes a communication flow (Cflow) between a local host and a remote service? – <protocol, srcIP, dstIP, dstPort>
Cross-clustering • Two hosts in the same A-clusters and in at least one common C-cluster are clustered together
Botnet Detection Systems summary • Bothunter: Vertical Correlation. Correlation on the behaviors of single host. • Botsniffer: Horizontal Correlation. On centralized C&C botnets • Botminer: Extension on Botsniffer, no limitations on the C&C types.
Thank you! Questions?