Network Protocol Tunneling
Network Protocol Tunneling. Network Security’s Friend or Foe Spyridon Dossis / DSV, Stockholm University. Outline. Description & Concerns Tunneling Protocols & Protocol Tunneling Network Tunneling Tools & Setup Demo Conclusions. Network Protocol Tunneling.

Network Protocol Tunneling
E N D
Presentation Transcript
Network Protocol Tunneling Network Security’s Friend or Foe SpyridonDossis / DSV, Stockholm University
Outline • Description & Concerns • Tunneling Protocols & Protocol Tunneling • Network Tunneling Tools & Setup • Demo • Conclusions
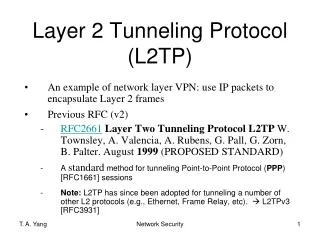
Network Protocol Tunneling • A delivery network protocol encapsulates a payload network protocol • The delivery protocol usually operates at the same or higher level (e.g. in the TCP/IP stack) than the payload protocol
Protocol Tunneling & Covert Channels • Protocol Tunneling • Order in Protocol Encapsulation • Obfuscation rather than hiding • Practical use cases & misuse • Covert Channels • Channels not intended for information transfer • Hiding in unused protocol fields, utilizing fields such as IP ID, TCP Sequence number etc. • Network Steganography
Common Uses • Carry data over incompatible delivery-networks • Provide a (encrypted) path through a public network • Monitoring vs Anti-Censorship • Allowing “some kind” of traffic may lead to “any kind”
Misuse of Network Tunneling • Pre-existing network-based security tools (firewalls, IDS) may not be able to apply the controls to the tunneled traffic • Evading traffic regulation • Lack of host-based security controls • Defense in depth • Inability for ingress and egress filtering • ‘Open-ended’ tunnel may forward traffic to other internal hosts
Network Tunneling – Rising Concerns • Advanced Persistent Threats (APTs) - Remote Control & Data exfiltration • Backdoors with OS commands, file transfer capabilities are installed in target systems. • Upload collected files using common ports such as HTTP (80), HTTPS (443) and DNS (53) bypassing detection. • Covert channels for malware • e.g. C&C communications over DNS (i.e. Feederbot, W32.Morto )
Outline • Description & Concerns • Tunneling Protocols & Protocol Tunneling • Network Tunneling Tools & Setup • Demo • Conclusions
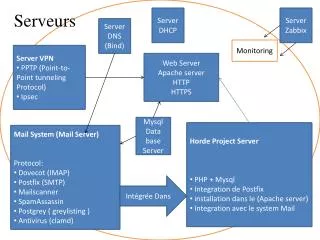
IPSec Tunnel Mode • The original IP packet is encrypted • The ESP header indicates that the entire packet is the payload (IP-in-IP) • Inserts a new IP header (next header is ESP) Image taken from http://www.free-it.de/archiv/talks_2005/paper-11156/paper-11156.html
IPSec Tunnel Mode • Security services from gateway to gateway or from host to gateway over an insecure network • The entire original packet is encrypted • Internal traffic behind the gateways is not protected • Often used to implement Virtual Private Networks (IPsec VPNs) • Site-to-site • Client-to-site
GRE – Generic Routing Encapsulation • “GRE (Generic Routing Encapsulation) specifies a protocol for encapsulation of an arbitrary protocol over another arbitrary network layer protocol” – RFC 2784 and 2890 • Point-to-point links Image taken from http://netwild.ru/pptp/
GRE and IP • Ethernet over IPv4/IPv6 (e.g. Openstack Neutron) • Support for tunneling broadcasting/multicasting • e.g. Delivering routing updates to multiple sites • IPv4/IPv6 over IPv4/IPv6 • No default encryption/security services • IPSec Tunnel/Transport over GRE
IPv6 over IPv4 Transition Mechanisms • Tunnel Brokers provide a network tunneling service • 6in4 – IPv6 over IPv4 • 4in6 – IPv4 over IPv6 • ISATAP • Teredo – IPv6 over UDP over IPv4 • …and others
SSH (Secure Shell) Protocol • Secure channel over an insecure network between an SSH client and an SSH server (e.g. OpenSSH) typically listening at TCP port 22 • Public-key cryptography for server (and client) authentication • Remote command execution, file transfer (SCP, SFTP), TCP port and X forwarding, tunneling
SSH Local-port forwarding • Local-port forwarding when traffic coming to a local port is forwarded to a specified remote host/port • Destination is relative to the SSH server’s location and mostly unrestricted • SSH client can be configured to act either as a local-only service or public to other hosts
SSH Remote-port forwarding • Remote-port forwarding when traffic coming to a remote port is forwarded to a specified local host/port • Destination is relative to the SSH client’s location and mostly unrestricted • SSH server can be configured to act either as a local-only service or public to other hosts
SSH Static Forwards Limitations • Performs successfully for single-host/port communications • Simple Web (HTTP) • Mail (SMTP, POP3, IMAP) • SSH • Fails for more complex network services • Web with External References / Surfing • Solution: Chain to a Web Proxy • FTP • Peer-to-Peer
SSH Dynamic-port Forwarding • The SOCKS protocol proxies TCP connections/forwards UDP packets from client to server through a proxy • A local SOCKS proxy is created on the SSH client’s side and can forward traffic to arbitrary remote hosts and ports • Firewall Traversal / Content-filtering circumvention
SSH X forwarding • Run remote X Window System based applications but displayed locally • Need for X server for Windows • Secure the X protocol by tunneling it over SSH • ssh –X user@host <application> • Run a remote browser visiting a blocked website
ICMP Tunneling • “An ICMP ECHO_REQUEST packet contains an additional 8 bytes worth of ICMP header followed by an arbitrary-amount of data” – ping(8) man page • LOKI (Phrack Issue 49) utilized it to establish a covert channel between client/server • IP over ICMP • TCP over ICMP
HTTP Tunneling • Various network protocols are encapsulated using the HTTP protocol • HTTP is rarely blocked • Bypass restrictions • Firewalls • Proxy server / Content-filtering
DNS Tunneling - Overview • Transport arbitrary data by encoding them into DNS messages • Wide support and availability of the global DNS infrastructure • Few organizations block DNS traffic from individual clients to the Internet (e.g. captive portals in public Wi-Fi) • Effective for bypassing security measures such as firewalls or ACLs • Used for two-way communication or data exfiltration
DNS Tunneling - History • Around since 1998 • NSTX (Nameserver Transfer Protocol) • OzymanDNS (Dan Kaminsky) – “Tunneling Audio, Video and SSH over DNS” • Used mostly for bypassing paywalls
DNS Primer • Mapping domain names and IP addresses • Record types • A, AAAA, CNAME, MX, NS, PTR, TXT, NULL • EDNS for UDP payloads larger than 512 bytes • Increased bandwidth • Internal users can contact arbitrary external domains through the organization’s DNS servers/resolvers
DNS Recursive Resolution Image taken from http://nirlog.com/2006/03/28/dns-amplification-attack/
DNS Tunneling - Limitations • Maximum 253 characters in domain • Maximum 63 characters per subdomain • Case-insensitive (Base32 encoding) • TXT requests allow for maximum characters in response + Base64 encoding • Bandwidth up to 110KB/s, 150ms latency (Van Leijenhorst, 2008)
Outline • Description & Concerns • Tunneling Protocols & Protocol Tunneling • Network Tunneling Tools & Setup • Demo • Conclusions
UDP over SSH Static Forwards • Combined with NetCat • Establish a local/remote port forward over SSH with an SSH server • Create a FIFO special file (a named pipe) on both sides • Listen for UDP requests / Relay through the SSH tunnel • Forward UDP requests / Relay through the SSH tunnel • tcp_to_udp & udp_to_tcp • socat Relay & UDPTunnel (UDP over TCP)
SSH Dynamic-port Forwarding • In the case of HTTP browsing, DNS requests are still submitted by the client • Monitoring can reveal DNS requests for common websites along SSH traffic. • Solution: forward DNS requests also to the SSH server. • (e.g. Firefox network.proxy.socks_remote_dns) • Multi-hop setups • Client (SSH lpf) -> Host 1 (SSH dpf) -> Host 2 -> Web
SSH Tunneling Detection / Mitigation • SSH Traffic Volume & SSH Tunnel Endpoints • Tunnel Hunter (Dusi et al., 2008) • Naïve Bayes Classifier • Packet size & Packet inter-arrival time • Detect Tunneling & Classify the actual protocol (BitTorrent, POP, SMTP, HTTP) with high accuracy • Limitations with respect to multiple SSH authentication types, data compression, login failures, network protocols • SSH server in non-standard ports (e.g. 443) • EmergingThreats Snort Rules, Cisco IDS • Degrade SSH performance (TCP over TCP )
ICMP Tunneling Technique Image taken from http://www.sectechno.com/2010/10/31/bypassing-firewalls-using-icmp-tunnel/
ICMP Tunneling Tools • ICMPTX (IP over ICMP) • ICMP Tunnel (IP over ICMP) • Hans (IP over ICMP) • itun (IP over ICMP) • Ptunnel (TCP over ICMP) • Droid-VPN , Troid-VPN (Android Apps, need root) • PD-Proxy, Wi-Free, Tunnel Guru • +++++++++++++++++++++++++++++++++++++++++++++++
ICMP Tunneling Detection / Mitigation • Detection Signatures • ICMP_PingTunnel_Detected • LOKI ICMP tunneling back door • ICMP Raw Sockets • Non-standard average packet size • High ICMP traffic volume between tunnel endpoints • Disallow ICMP traffic
HTTP Tunneling Technique • The Tunnel Client initiates an HTTP connection to the Tunnel Server • The application encapsulates the application requests in HTTP requests destined to the Tunnel Server • The Tunnel Server unwraps and forwards
HTTP Tunneling Tools • GNU httptunnel • htc – Tunnel Client component • hts – Tunnel Server component • Syntax • Server: hts –F remote:<remote_port> 80 • Client: htc –F <local_port> server:80ssh –p <local_port>user@localhost
DNS Tunneling - Tools • OzymanDNS • Dns2tcp • Iodine • Heyoka (+ source IP spoofing) • DNSCat • NSTX • DNScapy • MagicTunnel, Element53, VPN-over-DNS (Android) • iodine for iOS • “VPN over DNS”
DNS Tunneling – Detection / Mitigation • Increased DNS traffic (network traffic profiling) • Maximum DNS request packet size • Large number of DNS TXT requests • Number of DNS requests, unique hostnames to a single domain • Composition of hostnames • Length, unique characters, character frequency analysis • Split DNS • Web proxies (but not clients) can resolve external domains
DNS Tunneling - Challenges • Determining which tunneling messages are malicious • Real-time Blackhole Lists (DNSBL lookups) • 23.42.168.192.dnsbl.example.net • example.net.dnslist.example.com • NIST National Software Reference Library • 84C0C5914FF0B825141BA2C6A9E3D6F4.md5.dshield.org • Mail server performs DNS TXT requests (SPF)
Outline • Description & Concerns • Tunneling Protocols & Protocol Tunneling • Network Tunneling Tools & Setup • Demo • Conclusions
Outline • Description & Concerns • Tunneling Protocols & Protocol Tunneling • Network Tunneling Tools & Setup • Demo • Conclusions