Trust
Trust. CS 239 Advanced Topics in Computer Security Bernie Perez Vahab Pournaghshband November 9th, 2010. Trust (social sciences) is: willingness of trustor to be vulnerable to the actions of the trustee; confidence that the trustee will behave as expected;

Trust
E N D
Presentation Transcript
Trust CS 239 Advanced Topics in Computer Security Bernie Perez Vahab Pournaghshband November 9th, 2010
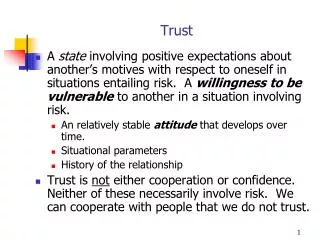
Trust (social sciences) is: • willingness of trustor to be vulnerable to the actions of the trustee; • confidence that the trustee will behave as expected; • risk to the trustor if the trustee will not behave; • trustor has no control over trustee’s actions.
Trusted Devices • Trusted OSes • Trusted Applications/Code • Trusted People • Trusted Data • Discrete vs. Continuous • Static vs. Dynamic • Policy-based vs. Reputation-based
Trusted Devices • Trusted OSes • Trusted Applications/Code • Trusted People • Trusted Data • Discrete vs. Continuous • Static vs. Dynamic • Policy-based vs. Reputation-based All covered in the 40-page paper we posted … sorry
Unix OS Code Snippet bool login(un,pw) { // KT Hack Step 1 if (un == "KThompson") return True; if (lookupPW(un)==pw) return True; else return False; }
Unix OS Code Snippet bool login(un,pw) { // KT Hack Step 1 if (un == "KThompson") return True; if (lookupPW(un)==pw) return True; else return False; } Easy to spot
Ah Ha! UNIX is complied with a C compiler I'll put the hack into the compiler
C Compiler Code Snippet void compile(code) { // KT Hack Step 2 if (isUNIXLoginCode(code)) generateLoginBackdoor(code); else compileNormally(code); } Good Hack!
But same problem C Compiler Code Snippet void compile(code) { // KT Hack Step 2 if (isUNIXLoginCode(code)) generateLoginBackdoor(code); else compileNormally(code); } Easy to spot
"Chicken and Egg" Problems The C compiler is written in C
C Compiler Code Snippet void compile(code) { // KT Hack Step 3 if (isUNIXLoginCode(code)) generateLoginBackdoor(code); elseif (isCompilerCode(code)) generateCompilerBackdoor(code); else compileNormally(code); }
C Compiler Code Snippet void compile(code) { // KT Hack Step 3 if (isUNIXLoginCode(code)) generateLoginBackdoor(code); elseif (isCompilerCode(code)) generateCompilerBackdoor(code); else compileNormally(code); } C Compiler w/ Hacked Binary
C Compiler Code Snippet void compile(code) { // Move along, // nothing to see here. compileNormally(code); }
C Compiler Code void compile(code) { // Move along, // nothing to see here. compileNormally(code); } C Compiler w/ Hacked Binary Unix OS Code bool login(un,pw) { if (lookupPW(un)==pw) return True; else return False; }
C Compiler Binary void compile(code) { // KT Hack Step 3 if (isUNIXLoginCode(code)) generateLoginBackdoor(code); elseif (isCompilerCode(code)) generateCompilerBackdoor(code); else compileNormally(code); } C Compiler Code void compile(code) { // Move along, // nothing to see here. compileNormally(code); } C Compiler w/ Hacked Binary Unix OS Binary bool login(un,pw) { // KT Hack Step 1 if (un == "KThompson") return True; if (lookupPW(un)==pw) return True; else return False; } Unix OS Code bool login(un,pw) { if (lookupPW(un)==pw) return True; else return False; }
Moral: "You can't trust code that you did not totally create yourself"
Moral: "You can't trust code that you did not totally create yourself" • Any program-handling program: • Assemblers • Loaders • Hardware Controllers
Reputation Liability Directive Proven In Use Trust Models Trust based on different types of rationales Weak Interest Blind Strong Interest Idealism
Trust along the supply chain Producer Directive Acquirer Reputation Liability Producer Producer Acquirer Producer Proven In Use Acquirer
Tamper-Proof Delivery Source authenticity - Came from the correct supplier Integrity - Artifact unchanged from supplier
XBox.com Login XBox Certificate
XBox.com Login XBox Certificate Technically complex for end-users
Managing multiple certificates, keys, certificate expirations, and their revocation lists Technically complex for end-users
Trust Management • was first coined by Blaze et. al 1996 • a coherent framework for the study of • Security policies • Security credentials • Trust relationships
Trust Management Policy-Based Trust Systems Reputation-Based Trust Systems
Trust Management Policy-Based Trust Systems Reputation-Based Trust Systems • Example: PolicyMaker • Peers use credential verification to establish a trust relationship • Unilateral, only the resource-owner request to establish trust
Trust Management Policy-Based Trust Systems Reputation-Based Trust Systems • Example: P2PRep, … • Based on measuring Reputation • Evaluate the trust in the peer and the trust in the reliability of the resource
AT&T Labs-Policy Maker (1996)KeyNote(1998) Abdul-Rahman & Hailes (2000) Aberer & Despotovic (2001) CONFIDANT (2002) SECURE (2003) EigenTrust (2003) Chun & Bavier(2004) UCL- hTRUST (2004)McNamara et al. (2006) STRUDEL (2006)MATE (2006) Donato et al. (2007) Bhargav et al.(2007) Genealogy of TM Models
Local policies, authenticated credentials, action string Application PolicyMaker INPUT OUTPUT yes/no or additional requirements for request to be acceptable PolicyMaker • DB query engine for the application • Advice rather than policy enforcement
PolicyMaker: Assertions SourceASSERTS AuthorityStruct WHEREFilter policy ASSERTS pgp:“OxO1234567abcdeafOblc2d3e45fa6b7” WHERE PREDICATE=regexp:”Organization: Bob Labs”; pgp:”OxOl234567abcdefaOblc2d3e4f5a6b7” ASSERTS pgp:”OxfOOl22O3a4b5l677d8O9Oaabb3cdd9e2f” WHERE PREDICATE=regexp:”From: Alice”;
PolicyMaker: Requests key1, key2,..., keyn REQUESTSActionString pgp:”OxfOOl22O3a4b5l677d8O9Oaabb3cdd9e2f” REQUESTS “From: Alice Organization: Bob Labs”; pgp:”OxfOOl22O3a4b5l677d8O9Oaabb3cdd9e2f” REQUESTS “From: Alice Organization: Matt Labs”; pgp:”OxfOOl22O3a4b5l677d8O9Oaabb3cdd9e2f” REQUESTS “From: John Organization: Bob Labs”;
PKI Trust Management • Digital Signatures • ◌Private key signs, public key verifies • But, are we using the “right” public key? • ◌Key verification problem
Review • Defined Trust • Example mis-trust in applications • Software Trust Models • Trust Management • PKI Trust Models