The Secure Hill Cipher
The Secure Hill Cipher. HILL. Jeff Overbey MA464-01 • Dr. Jerzy Wojdyło • April 29, 2003. Based on S. Saeednia. How to Make the Hill Cipher Secure. Cryptologia 24 (2000) 353–360. The Scenario. The Scenario. Alice. The Scenario. Bob. The Scenario. Oscar. The Scenario. Sender.

The Secure Hill Cipher
E N D
Presentation Transcript
The Secure Hill Cipher HILL Jeff Overbey MA464-01 • Dr. Jerzy Wojdyło • April 29, 2003 Based on S. Saeednia. How to Make the Hill Cipher Secure.Cryptologia 24 (2000) 353–360.
The Scenario Alice
The Scenario Bob
The Scenario Oscar
Sender Recipient Nosy Neighbor The Scenario Insecure Channel
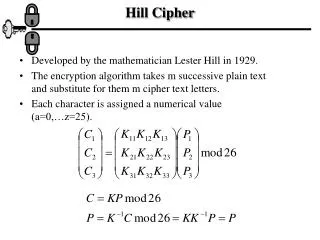
Beforehand… Alice and Bob privately share matrix K, invertible over Zm To encrypt a matrix X over Zm… Compute Y = KX Send Y To decrypt Y… Compute X = K–1Y Hill Cipher
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure “Hey Bob,wassup?” Insecure Channel
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel Y = KX
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel HEYBOBWAS Known Plaintext
Sender Recipient Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel HEYBOBWAS Known Plaintext
KNOWNPLAINTEXTATTACK KNOWNPLAINTEXTATTACK Sender Recipient hahahaHAHAHAHA… Nosy Neighbor Why the Hill Cipher Isn’t Secure Insecure Channel HEY BOB,WASSUP?
Beforehand… Alice and Bob privately share matrix K, invertible over Zm To encrypt a matrix X over Zm… Compute Y = KX Send Y To decrypt Y… Compute X = K–1Y Secure Hill Cipher Beforehand… • Alice and Bob privately share matrix K, invertible over Zm To encrypt a matrix X over Zm… • Choose a vector t over Zm • Form permutation matrix Pt • Compute Kt = Pt–1KPt • Compute Y = KtX and u = Kt • Send (Y,u) To decrypt (Y,u)… • Compute t = K–1u • Compute Pt • Compute Kt–1 = Pt–1K–1Pt • Compute X = Kt–1Y Note that (Kt)–1 = (K–1)t Hill Cipher
Permutation Matrices I = P23 =
Permutation Matrices I = P23 = A permutation matrix is a matrix with exactly one 1 in each row and column and zeros elsewhere. P12,23 =
Vector Representation P23 = P12,23 =
Beforehand… Alice and Bob privately share matrix K, invertible over Zm To encrypt a matrix X over Zm… Compute Y = KX Send Y To decrypt Y… Compute X = K–1Y Hill Cipher Secure Hill Cipher Beforehand… • Alice and Bob privately share matrix K, invertible over Zm To encrypt a matrix X over Zm… • Choose a vector t over Zm • Form permutation matrix Pt • Compute Kt = Pt–1KPt • Compute Y = KtX and u = Kt • Send (Y,u) To decrypt (Y,u)… • Compute t = K–1u • Compute Pt • Compute Kt–1 = Pt–1K–1Pt • Compute X = Kt–1Y
The Easy Way to Encrypt • Require t to be the vector representation of a permutation matrix • N.B.: This is for example only—it is not practical “in the field.”
An Example “Hey Bob, wassup?”
Form permutation matrix Pt: An Example Choose a permutation vector: 3 rows, since K is 3×3
Compute Kt = Pt–1KPt : An Example Find Pt–1:
An Example Find Pt–1: Compute Kt = Pt–1KPt : Permutation of K
An Example Compute Y = KtX: Compute u = Kt:
An Example Compute Y = KtX: Compute u = Kt:
An Example Send (Y,u) to Bob
Sender Recipient Nosy Neighbor The Scenario
Sender Recipient Nosy Neighbor The Scenario
Sender Recipient Nosy Neighbor The Scenario
Sender Recipient Nosy Neighbor The Scenario
An Example Receive (Y,u):
Compute t = K–1u and derive Pt: An Example Compute K–1:
Compute X = Kt–1Y: An Example Compute Kt–1 = Pt–1K–1Pt:
Compute X = Kt–1Y: An Example Compute Kt–1 = Pt–1K–1Pt: “Hey Bob, wassup?”
KNOWNPLAINTEXTATTACK KNOWNPLAINTEXTATTACK An Example But that was just a regular Hill cipher with a fancy key…
The Actual Really Secure Hill Cipher HILL Jeff Overbey MA464-01 • Dr. Jerzy Wojdyło • April 29, 2003 Based on S. Saeednia. How to Make the Hill Cipher Secure.Cryptologia 24 (2000) 353–360.
The Actual Really Secure Hill Cipher HILL or How to Secure the Secure Hill Cipher
Ensuring Security • X should have two columns • Why? Suppose K is n × n and X is n × s. • If s n… • If 2 < s< n… • If s = 2… • Pt should be different for each encryption • Theoretically, this can be ensured by choosing a different t for each encryption • We did this by requiring t to be a vector representation of a permutation matrix, but this is not the best solution.
The Function Let n denote the set of n × n permutation matrices. : Zmn n Ideally, • is onto • is 1-1
y = 26n y = n! The Function Let n denote the set of n × n permutation matrices. : Zmn n Is it possible? • Zmn = mn • n = n! • Zmn n An “ideal” function DNE.
The Function Ideas? Awkward silence…