Utilizing a Quantitative Risk Approach
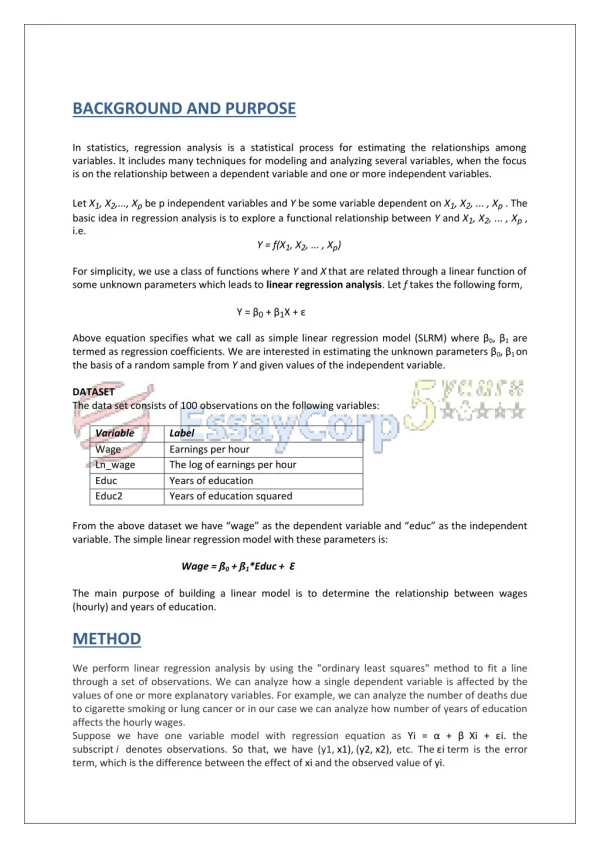
330 likes | 556 Views
Utilizing a Quantitative Risk Approach. To Drive Strategic IT COMPLIANCE. Glenn R. Wilson. VA SCAN October 3, 2013. Classifying IT R isk. Classifying IT Risk. Data risk Breach, loss, corruption, unavailability Operational risk Performance degradation, denial of service, outages

Utilizing a Quantitative Risk Approach
E N D
Presentation Transcript
Utilizing a Quantitative Risk Approach To Drive Strategic IT COMPLIANCE Glenn R. Wilson VA SCAN October 3, 2013
Classifying IT Risk Classifying IT Risk • Data risk • Breach, loss, corruption, unavailability • Operational risk • Performance degradation, denial of service, outages • Non-compliance risk
Common IT Risks • Unauthorized data access and changes • Data loss, corruption, unavailability • Denial of service attacks, malware • Physical device failure, theft or destruction • Inadequate system capacity, network architecture • Poor application coding, failed implementations • Inadequate change management controls • Regulatory compliance violations
Common IT Risk Impacts • Reduced customer satisfaction permanent customer loss • Business process interruption lost productivity / revenues • Penalties, fines, sanctions, reputational damage, personal liability • Fraud, identity theft, loss of financial assets • Failure to achieve core business objectives • What are the common themes? • Mission risk • Monetary loss • Legal liability
Why Comply? • Compliance reduces exposure to penalties and litigation • Compliance provides a baseline for risk management • Compliance is integral to proper corporate governance • Compliance requires a business to adopt best practices • Compliance promotes organizational effectiveness
In Compliance What does it mean to be “in compliance”? How do you know when you have achieved it? How do you sustain a state of compliance? What do we have to comply with? FERPA, HIPAA, HITECH, GLBA, SOX, PCI DSS, FISMA, ECPA, COPPA,EFTA, Bank Secrecy Act, USA Patriot Act, Basel II Accord … The short answer: “industry standards, federal, state and local laws” How many organizations put this statement into their policies and aren’t exactly sure what they are obligating themselves to?
Approaching Compliance • “Compliance should be the floor, not the ceiling, of your efforts” “It’s the fundamental layer for every security program.” (Rafael Diaz, CISO of the State of Illinois, quoted by Security Magazine from a Nov 2012 Chicago SC Congress event of SC Magazine) • Other speakers warned against using compliance as the be-all-end-all of an information security program. • “Compliance is a great hammer – if you have a nail”. “Don’t use a hammer if you have a screw”. “Using a FAIR report (Factor Analysis of Information Risk), which can translate the risk into real dollar amounts, making it easier to sell to the C-suite”. (Ward Spangenberg, CISO of Pearl.com, formerly of online gaming giant Zynga, quoted by Security Magazine from a Nov 2012 Chicago SC Congress event of SC Magazine) Source: http://www.securitymagazine.com/blogs/14-security-blog/post/83788-cisos-look-past-compliance-for-new-solutions-to-old-problems
Successfully Achieving Compliance • Know your organization’s specific compliance exposure • Know the processes by which its objectives are achieved • Gain executive level support • Obtain managerial and staff commitment • Where do you start? • The invariable starting point is… • Business Impact Assessment
Realities of Compliance • Compliance is not equal to Risk Management • (although achieving compliance does mitigate risk) • Can achieving compliance create risk? • Yes. What kinds? Operational, Financial, Legal • Failure to achieve compliance is itself a risk category
Drivers of Compliance • What is the primary driver of organizational compliance? • Non-compliance risk – Penalties, sanctions, liabilities • Other risk drivers: Financial, Reputational, Operational & Individual risk • Who primarily drives organizational compliance? • Board? • Executive Management? • Compliance Officers? • Internal Auditors? • Middle Management? Effective programs are driven by a culture of compliance and align with the organization’s strategic planning
Degrees of Compliance • To what extent should an organization ‘be in compliance’ • with a given regulatory requirement or industry standard? • 100%? 80%? 50%? 0%? • How fast should an organization achieve compliance? • How long should an organization be in compliance? • How far? How fast? How long?
Risk Versus Compliance How does risk vary with compliance? Risk Compliance • Greater compliance can decrease risk at many levels • Greater compliance may increase risk at many levels
Risk Mitigation Versus Cost Diminishing Return • What costs may be associated with risk mitigation? • Financial resources • Human resources • Competitive advantage loss Risk Cost
“Selling” Compliance • The need for compliance sells itself • The degree of compliance needs to be driven to levels appropriate for the organization. • Compliance costs can be expensive at many levels • Risks are well known but often not well understood • Do not overstate the merits or consequences • Do determine and promote impact awareness
Quantifying Risk To Drive Compliance • Are numbers persuasive? • Join now for only $19.95 per month • 4 out of 5 dentists recommend sugarless gum • More doctors smoke Camels than any other cigarette (133,597 surveyed) • Gartner Group says that 43 percent of companies were immediately put out of business by a “major loss” of computer records, and another 51 percent permanently closed their doors within two years — leaving a mere six percent “survival” rate; (homelandsecuritynewswire.com Feb 19, 2010)
Qualitative vs Quantitative Analysis • Qualitative • Faster, not data intensive • More cost-effective or is it? It does not provide numerical impact making cost benefit analysis difficult • Analysis based on likelihood and impact • Results stated in terms of low, med, high or similar numerical scale • Good for prioritizing risk and identifying high risks that need immediate mitigation • Quantitative • Data intensive simulation and decision analysis • Results stated in terms of probabilities and costs • Primary advantage is the cost benefit analysis for efficient use of resources • Results that are not clear will be qualitatively determined • Not every risk requires or is suited to quantitative analysis • Define a criteria for meaningful quantitative analysis of your organization’s risks • Identify technique(s) to be utilized and develop methods for consistent application • Define the expected outputs of the chosen quantitative analysis methods
Risk / Impact Models Which Likelihood - Impact pairs should be analyzed? Likelihood Med High Low Med High Low Impact
Risk / Impact Assessments • Inherent risk = high (9/10), Residual risk = medium (6/10) • Risk = (Probability) x (Impact) • More scientific ‘closed form’ methods exist using Convolution and Fourier Transforms which require large amounts of data to calculate frequency and severity distributions to obtain an aggregate losses (expected, unexpected, confidence levels) • ‘Open form’ solutions such as Monte Carlo simulation and Latin Hypercube sampling that evaluate scenarios for frequency and severity • of losses by generating random numbers using each type of distribution (identified using actual loss data).
Risk / Impact Distribution Calculations VaR = VaR12 + VaR22 + 2 * C2* VaR1 * VaR2 • Periodic • Aggregate Loss
Risk / Impact Calculation Models EF = (((TP×(C/E))×(VF×AP))/100) Risk Exposure = ALE = SLE * ARO EF: Exposure factor (% loss of asset) TP: Threat probability C: Criticality factor E: Effort requited to exploit the threat ALE: Annualized Loss Expectancy SLE: Single Loss Expectancy ARO: Annual Rate of Occurrence Return On Security Investment (ROSI) – A Practical Quantitative Model Wes Sonnenreich, Jason Albanese and Bruce Stout SageSecure, LLC 116 W. 23rd St., 5th Floor, NY, NY 10011 USA Journal of Research and Practice in Information Technology, Vol. 38, No. 1, February 2006 Adrian Munteanu, Alexandru Ioan Cuza University, Iasi, Romania Information Security Risk Assessment: The Qualitative Versus Quantitative Dilemma Managing Information in the Digital Economy: Issues & Solutions 228 Risk = Σan (Σram (Cm*(Vm*Om))) Risk Score = log(10Risk Score1+10Risk Score2) Likelihood Score = log(10Likelihood Score1 +10Likelihood Score2) Consequence Score = Risk Score – Likelihood Score Σan: Sum of the asset risk Σram: Risk sum for each combination of criterion, vulnerability and threat per asset Cm: Criterion value for the current combination Vm: Vulnerability risk level for current combination Om: Threat occurrence for current combination XunGuo Lin & Richard Jarrett Division of Mathematical and Information Sciences A Practical Approach to Quantitative Risk Assessment Canberra & Melbourne Risk Conference, Wellington, 2009 Abbas Asosheh, Bijan Dehmoubed, Amir Khani Tarbiat Modares University Tehran, Iran A New Quantitative Approach for Information Security Risk Assessment 2009 IEEE
Practical Considerations • What are the primary objectives of quantifying risk to drive compliance? • To quantify in whole or in part losses, expenses and liability • (Some quantification is better than none) • To use the methods and results to inform executive decision makers • What are the most useful numbers to consider? • Loss Expectancies (single and recurring) • Occurrence (actual or estimated) • Asset Value (tangible and intangible) • Recovery Costs • Long Term Costs
Establishing Impact Scales • Risk appetite is organization specific • with dependencies on: • Industry • Business Mission • Capitalization and Cash Flow • Board and Executive Management • Define risk / loss levels in terms of: • Monetary value • Liabilities / penalties • Mission specific factors
Case Specific Factors • Is this a valid quantitative analysis? • Annual threat probability 75% • Incident cost $1,000,000 • Weighted cost $750,000 • Annual counter cost $600,000 • Cost benefit $150,000 • What are the case specific factors? • Risk type and nature • Basis for numeric values • Cost types considered
Compliance Checklists • Strengths • Identifying gaps and deficiencies (a very necessary activity) • Weaknesses • Prioritizing remediation of deficiencies • Tracking corrective actions • Cost management • Resource deployment • May not result in value to the organization • Does not ensure adequate security or risk mitigation • May lead to an overburden of overlapping / unnecessary controls
Making The Case • How related or specific is the compliance type to your business? • Exactly what are the associated compliance risks? • What are the expected costs and impacts to comply? • How much return will be realized in reduction of risk or increased effectiveness? • Numbers are most persuasive when they are validly derived, understandable and relevant to a given situation. They can be mixed with qualitative factors.
Example – XYZ Act Compliance • The new XYZ federal ecommerce regulatory act will go into effect in 3 months. Even though your organization derives significant revenue from ecommerce activities, the new act is not on the radar of executive management even though you first brought the need to comply to their attention 18 months ago and again 3 months ago. You are not directly responsible for ecommerce revenues but are responsible for operating the organization’s ecommerce system within ‘industry standards, applicable federal, state and local laws. Major infrastructure reconfiguration and architectural changes are needed to comply. How can you re-approach the subject with executive management to gain the necessary support? • According to the last quarter financials, $6k per hour or 46% of revenues come from ecommerce activities. • There is a new threat vector that we have never faced before and there is a high probability that within months our system will be exploited if it is not hardened to the new standard. The IDS upgrade will cost $200k, and to comply within 3 months it will require 300 staff hours and $240k off peak ecommerce downtime. • If we do not act and an incident occurs, it will likely be viewed as “willful negligence” and we would incur the maximum fine of $10k a day plus average clean up costs of $80 per affected record of which we have 2 million. Our ecommerce operation could be disrupted or suspended by an external investigation for 7-10 days. • Every week that this project is delayed will cost an additional $20k in peak downtime and $10k in shift differential compensation.
Case 1 – PCI DSS • Essential Elements of Compliance: Secure collection, handling, storage and transmission of card-holder data, quarterly system scan by a PCI SSC Approved Scanning Vendor (ASV), annual SAQ • Non-Compliance Risk: The payment brands may, at their discretion, fine an acquiring bank • $5,000 to $100,000 per month for PCI compliance violationswhich will pass to the merchant. Bank • will also most likely either terminate your relationship or increase transaction fees. PCI is not a law. • Compliance Risk: Potential adverse effects on business processes and IT workload • Added Value: Mitigate risk of cardholder data breach, improved IT vendor contractual relations • Quantifying Risk Factors • Payment card revenue (gross and relative amounts) • Payment card transactions (gross and relative amounts) • Current transaction and processing fees • Cost to achieve compliance • Recurring costs
Case 2 – Sarbanes Oxley (SOX) • Essential Elements of Compliance: Publicly traded companies must maintain all controls needed • for accurate financial reporting. Financial reports require an internal controls report. • Non-Compliance Risk: Exchange de-listing, loss of investor confidence, loss of liability insurance. Incorrect submissions carry up to a $1 million fine and 10 years in imprisonment. • Willful incorrect violations allow for up to $5 million fine and 20 years imprisonment. • Compliance Risk: Drain on available resources, business process changes, IT requirements • are not well defined and attempts to comply may not pass an external audit. • Added Value: More reliable financial and asset controls, increased market capitalization • Quantifying Risk Factors • Stock ownership • Current market capitalization • Industry sector volatility
Case 3 – E911 • Essential Elements of Compliance(Virginia): All PBX/MLTS installed after July 1, 2009 must provide ANI and ALI to the local PSAP for 911 calls unless alternate methods of notification have been approved. (Article 8. Emergency Calls on Multiline Telephone Systems.§ 56-484.23) • Non-Compliance Risk: (Varies by state) Fines, OSHA sanctions, worker’s compensation claims caused by safety violation, common law liability, reputational damage • Compliance Risk: Significant cost to upgrade or replace existing phone system, business interruption, transient risk of media relation issues • Added Value: Employee trust, increased productivity, public goodwill, decreased liability • Quantifying Risk Factors • Age of the existing phone system • Cost to upgrade versus replace • Number of facilities, geographic distribution and occupancy habits • Case law
Case 4 – Gramm Leach Bliley (GLBA) • Essential Elements of Compliance: Protect consumers’ personal financial information held by financial institutions. There are three principal parts to the privacy requirements: the Financial Privacy Rule, the Safeguards Rule and pretexting provisions. The safeguard rule requires a plan that “contains administrative, technical, and physical safeguards” to “insure the security and confidentiality of customer information; protect against any anticipated threats or hazards to the security or integrity of such information; and protect against unauthorized access to or use of such information that could result in substantial harm or inconvenience to any customer. • Risk of Non-Compliance Risk: Fines up to $100,000 for each violation, Personal liability to officers and directors of up to $10,000 for each violation, Criminal penalties include imprisonment for up to 5 years. More serious willful violations call for the fine will be doubled and imprisonment for up to 10 years. (Monetary losses (immediate and future), reputational damage, personal liability) • Risk of Compliance: Business process and operational change management • Added Value: Customer relations, decreased legal liability • Quantifying Risk Factors • Implementation / recurrent costs versus volume / revenue associated with qualifying financial activities
Comments? Questions? Glenn R. Wilson, IT Audit Manager Old Dominion University, Norfolk, VA gwilson@odu.edu 757-683-3202 Thank you!