Cryptographic Protocol Amendment Proposal for Enhanced Security
The proposal outlines updates for the AMP system, including editorial changes, fixing flaws in PAK-Z, promoting unrestricted language, and enabling support for different signature schemes. It emphasizes consistency in variable naming conventions and offers guidelines for implementing improved security measures. The document also discusses the concept of provable security and its significance in cryptographic protocols to prevent potential breaches. Furthermore, it introduces the PAK-Z+ security theorem to enhance the overall system resilience.

Cryptographic Protocol Amendment Proposal for Enhanced Security
E N D
Presentation Transcript
P1363.2 update David Jablon, Phil MacKenzie
Outline • AMP • Kwon proposed editorial change to PVDGP-AMP • Fix of APKAS-AMP • Use AMP+ • PAK-Z • Editorial • Unrestricted language to allow all signature schemes • Variable name changes (for consistency) • Technical • Fixing flaw in PAK-Z • Client checks secret signature key against a hash • Client signs both DH messages, instead of just one
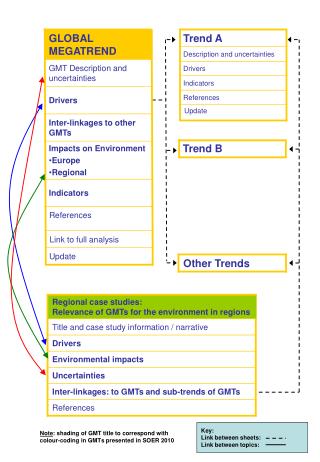
wc ws AMP+ (simplified) [K2005] vpw = gh(pw) Client Server pw wc = gsc Check wc in parent group ws = ((wc)h(wc) vpw)ss Check ws is not in small subgroup e = (sc+h(wc,ws) )/(sch(wc) +h(pw)) z = (ws)e z = (wcgh(wc,ws))ss
Other AMP considerations • Editor’s Notes • D.5.5.1.8-10
PAK-Z Editorial • Fix inconsistencies • Variable names (uniform naming convention – upper case/lower case, etc.) • Sign(group element) changed to Sign(octet string representation of group element) • Etc. • Generalize Sign and Verify to allow other signature schemes • Requires representations of signatures and private keys, either of which could be a tuple of integers • Use 1363a-2004 E.3 for signature representations, and new P1363.2 E.4 for private key representations • Q: Informational v. Normative?
PAK (using g) m=gx· H1(pw) m=gy, k s a PAK-Z (simplified) [M2002] [g, pk, V’] g = H1(pw) V’ = H2(pw)sk Client Server pw g = H1(pw) Output keys (a’,sk) Output keys (a’,sk) a = a’ V’ sk = a a’ H2(pw) s = Signsk(m) Abort if Verifypk(m,s)=0
PAK (using g) m=gx· H1(pw) m=gy, k s a, V’’ PAK-Z+ (simplified) [g, pk, V’, V’’] g = H1(pw) V’ = H2(pw)sk V’’ = H3(sk) Client Server pw g = H1(pw) Output keys (a’,sk) Output keys (a’,sk) a = a’ V’ sk = a a’ H2(pw) Abort if H3(sk)V’’ s = Signsk(m,m) Abort if Verifypk ((m,m), s)=0
PAK (using g) m=gx· H1(pw) m=gy, k s a Attack on server resilience of PAK-Z [g, pk, V’] g = H1(pw) V’ = H2(pw)sk Client Adversary pw Assume pk=gsk g = H1(pw) Output keys (a’,sk) Output keys (a’,sk) a = a’ V’ 1 sk = a a’ H2(pw) s = Signsk(m) Compute pk’ from (m,s) If pk’=pk/g, bit 0 of sk is 1 Otherwise bit 0 of sk is 0 (Compute other bits of pk similarly)
Provable Security • “Provable Security”: • Show that breaking protocol implies breaking a well-known cryptographic assumption, like Diffie-Hellman • “Breaking Protocol” • Succeed with better probability than trivial online guessing of passwords • Intuitively, breaking a protocol means being able to perform an “offline dictionary attack” on the password
Model and definition (from [BPR2000]) • Adversary controls network and may ask for some session keys to be “revealed” • Attacker succeeds if it can distinguish an “unrevealed” session key from a random key • Advantage: AdvP(A) = 2Pr(SuccP(A))-1
PAK-Z+ Security Theorem (informal) • S = # of possible passwords • n = number of Send queries • t = running time of A • q = number of hash queries (random oracle model) • AdvPAK-Z+(A) = n/S + n·AdvDH(O(t)) + n·ForgeSig(O(t)) + e