Firewalls and VPNS
340 likes | 521 Views
Team 9 Keith Elliot David Snyder Matthew While. Firewalls and VPNS. Firewall. Provides a barrier and/or filter between networks Can be configured to block packets Sometimes called a level 4 switch. Hardware Firewalls. Stateless Packet Filters

Firewalls and VPNS
E N D
Presentation Transcript
Team 9 Keith Elliot David Snyder Matthew While Firewalls and VPNS
Firewall • Provides a barrier and/or filter between networks • Can be configured to block packets • Sometimes called a level 4 switch
Hardware Firewalls • Stateless Packet Filters • Evaluates each packet against a set of rules • Stateful Packet Filters • Evaluates connection attempts and monitors flow
Software Firewalls • Application • Operates at the application level by examining data before being passed down • Proxy-Based • Is a service that generally runs on a server that handles all requests • See next slide
Proxy Server • The specific firewall in the OpNet lab is a gateway (i.e. a router) running a Proxy Server. A client requests a service from the proxy server, which evaluates the request. If it is determined to be valid, the proxy server makes the service request on behalf of the client. • The proxy server can be disabled for specific applications (HTTP, Database, Email, etc.)
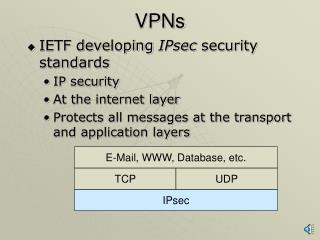
VPN • VPN (Virtual Private Network) • Acts as a private network connection (inside a company for example) while running over a more public internet. • Uses IP Tunneling.
Advantages: Firewall and VPN • Firewalls • Provides protection to network resources by restricting access based upon information contained in packets • Common Use: Allows the separation of Intra-nets from the Internet • VPN • Allows access through firewalls by creating virtual circuits using tunneling. • Common Use: Provides secure remote access to an institution's protected resources
Tunneling • Wraps an IP frame inside another frame of the same layer. • An IP frame inside another IP frame. • The inner packet can be encrypted, which allows for privacy of the connection. • You may remember IP6 was tested by tunneling inside IP4 packets.
Disadvantages: VPNs • Tunneling increases the length of IP packets • May result in inefficient use of bandwidth, especially for short packets • Potential performance impact at end routers as they need to do more work • Remove headers, decrypt packet body • Administrative overhead and cost associated with managing the VPN server
Scenario 1 - Described • Simulates two sales people working offsite • Characterized by light Web Browsing and light Database access • Connect to a server via the Internet. s
Scenario 2- Described • Replaces the simple router previously used to connect to the server with a firewall • Configured to block Database access. • The Sales people can still engage in Web Browsing
Scenario 3- Described • Scenario 3 configures a VPN for Sales A • Sales A now tunnels through the firewall and can access the database • Still allowing web browsing • Sales B is restricted to web browsing with no database access.
Results • Average Client DB and Client HTTP Traffic for the three scenarios. Show live.
Exercises 1 & 2 • Explain the effect of the firewall, as well as the configured VPN, on the database and HTTP traffic requested by Sales A and Sales B.
Exercises 1 & 2 - Observations • From the captured graphs, it can be observed that without the firewall both Sales A and Sales B clients were able to access the database, while adding the firewall prevented both Sales clients from accessing it. Configuring the VPN access for Sales A allowed it to access the database through the firewall. • Comparing the graphs of received HTTP and database traffic for both Sales A and B clients confirms that both clients receive HTTP traffic in all scenarios (i.e., the firewall permits HTTP traffic from both Sales clients). Once the firewall is in place however, database traffic is only permitted through the firewall using a VPN.
Exercise 3 • Generate and analyze the graph(s) that show the response time for DB Queries and HTTP requests.
Exercise 3- DB Queries • Obviously there is no DB Query response times for the Firewall without VPN • Firewall with VPN response time is slower due to overhead from the VPN and additional router.
Exercise 3 - HTTP • It was observed that the inclusion of the firewall did not add to the response time of the HTTP traffic. The additional inclusion of the VPN increased the response time of the traffic.
Exercise 4 • Create a diagram that allows database access and no HTTP access to Sales A and HTTP access and no Database access to Sales B.
Exercise 4 • Two additional firewall nodes were added, Router E and Router F. • The previous VPN runnel was changed from between Router A and Router D to between Router A and Router E. • A second VPN tunnel was then configured between Router B and Router F with the remote client set as Sales B. • Router E was then configured to allow database access but block HTTP access and Router F was configured to allow HTTP but block database access.
Exercise 5 • Configure Encryption over the VPN. Study Sales A DB response times.
Exercise 5 • You can see DB Query response time is increased with encryption. • As Sales A is the only one with DB Access, his response time should be identical to global response time and in fact they are.
Other Things We Tried:Restricting VPN Connections • VPN is an application with IP traffic itself, and it therefore should be able to blocked by the Firewall. And it can. If you duplicate the Firewall with VPN and configure the Firewall to block “Other Applications”, Sales A can no longer make DB Query or HTTP requests. • This is because Sales A's VPN in Compulsory. Set it to Voluntary and Sales A can make HTTP requests like Sales B by not using the VPN.
Other Things We Tried:VPN Impact on Network Traffic • Implementing a VPN should increase the volume of network traffic as all tunneled IP packets will be encapsulated inside the data portion of new packets. These packets will have the end router’s address as their destination. • To confirm this in the lab, we measured the throughput of the network link from Router A to the Internet to see how implementing a VPN impacted the total network traffic
Other Things We Tried:VPN Impact on Network Traffic • The rate of data sent to from Router A to the Internet is higher when the data is tunneled using the VPN • The is caused by the additional IP headers that are added by the VPN
Other Things We Tried:VPN Impact on Network Traffic • The rate at which data is received from the Internet into Router A is also higher when the data is tunneled using the VPN • The percentage increase that the VPN adds for the responses is lower than when sending data. This is a result of the responses are typically larger in size (e.g., database queries are typically shorter than the results etc.)