Chapter 8: System Software
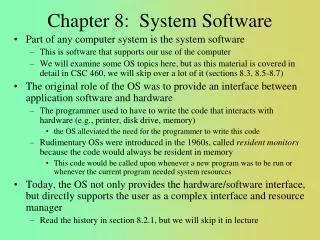
Chapter 8: System Software. Part of any computer system is the system software This is software that supports our use of the computer We will examine some OS topics here, but as this material is covered in detail in CSC 460, we will skip over a lot of it (sections 8.3, 8.5-8.7)

Chapter 8: System Software
E N D
Presentation Transcript
Chapter 8: System Software • Part of any computer system is the system software • This is software that supports our use of the computer • We will examine some OS topics here, but as this material is covered in detail in CSC 460, we will skip over a lot of it (sections 8.3, 8.5-8.7) • The original role of the OS was to provide an interface between application software and hardware • The programmer used to have to write the code that interacts with hardware (e.g., printer, disk drive, memory) • the OS alleviated the need for the programmer to write this code • Rudimentary OSs were introduced in the 1960s, called resident monitors because the code would always be resident in memory • This code would be called upon whenever a new program was to be run or whenever the current program needed system resources • Today, the OS not only provides the hardware/software interface, but directly supports the user as a complex interface and resource manager • Read the history in section 8.2.1, but we will skip it in lecture
OS Components • The kernel is the core of the OS • It supports the process manager, scheduler, resource manager and I/O manager • It is responsible for scheduling, synchronization, protection/security, memory management and interrupt handling • Other elements of the OS are • Shells – the user-specified environment • Utilities – programs usually run by the OS or user to keep the environment reasonably maintained (e.g., antiviral software, disk backup, disk defragmenter, screen saver, file manager) • We now examine services providing by the OS
User Interface • The interface actually takes on two roles: • Interface between user and hardware • How I/O requests are handled • This includes interrupt mechanisms, bus arbitration, protection mechanisms, and so forth • We covered some of this in chapter 7 and won’t go into any more detail here • Interface between user and software • How the user commands the system to perform operations whether the commands are to applications software or OS • Today, this is done through a GUI (menus, buttons, icons) • In the past, this was done through command line interpreters and still is common in OSs like Unix/Linux
Starting programs upon request Find executable code in the file system, load into memory Start the process give process a status and move to appropriate queue Handle scheduling of programs Process admitted to the system, placed in waiting queue Process moved to memory, placed in ready queue Program gets attention by the CPU context switching occurs between processes to move the CPU between processes Terminating the process and freeing its resources Process manager also Handles interprocess communication Communicates with other aspects of the OS kernel to track resource usage resource manager file manager memory manager Process Manager
Resources are finite They include disk/tape drives, memory, CPU, network connection, printer, etc Processes might need more resources than are available The OS allocates a resource to a process At that point, the resource is usually dedicated no other process can use the resource until the first process lets go of it this is known as mutually exclusive access – why is it necessary? This can lead to deadlock where processes hold resources and need other resources currently held by other processes P0 P1 R0 R1 Resource Management Process P0 currently has access to R0 and needs R1 while Process P1 currently has access to R1 and needs R0 result – deadlock, neither P0 nor P1 are able to continue but neither release their resources!
Synchronization & Atomic Instructions • Process manager must synchronize access to shared memory/resources • When a process wants access, it issues a request command • if the resource is unavailable, this process moves to a wait queue • once the resource becomes available, the next process in the queue is selected to hold onto the resource • We don’t want to interrupt the request command so we make it an atomic instruction (part of the instruction set) • Atomic instructions are non-interruptible even though they perform multiple steps such as “compare-and-swap” and “test-and-lock”
Memory Management, Modes • Memory is managed separately from resource management but is another type of resource • Manages virtual memory • Decides how many frames each processor (or user) is given • Allocates memory, should memory be allocated in contiguous blocks? • Memory management also searches for memory violations • CPUs typically operate in one of two modes: • User mode only has access to some operations and limited memory space access • Privileged mode (also known as system mode, administrator mode or kernel mode) has access to all operations and memory • When in user mode, program instructions may request access to resources/memory • To gain access, the OS must switch modes • Mode is a bit in the status flags
Security and Protection • In addition to deadlock, resource sharing leads to the situation where a process wants to use a resource that is owned by another process • Or the user who runs the first process wants to access a resource owned by a different user • Protection mechanisms must be enforced in the OS to make sure that this cannot happen • Otherwise, one use could access/erase/alter files owned by another user • Security mechanisms extend this idea of protection to networks so that a user is not able to access resources of the system (including the CPU and memory) unless they have been authorized to do so • Through some form of authentication mechanism such as logging in with a private password • Without security, systems would be susceptible to illegal access
Assemblers • The assembler is a program that translates an assembly program into machine language • Recall that there is a 1-to-1 mapping of assembly language instructions to machine instructions • unlike a high level language instruction which might require several to dozens of machine instructions • So the assembler’s task is not too difficult • Translate the mnemonic into the appropriate op code • Translate the operands into • Addressing mode and addressing specifications • Literals into binary equivalence • Variable names and Labels into memory locations and/or offsets • Compiler the list of variables and functions into a symbol table • What would happen if the assembler places variables and labels into specific memory locations? • the program/code would be non-relocatable
When you use library files of functions, those files are pre-assembled/compiled But your program needs to reference memory locations Where will your code and the library code be placed? It is the job of the linker to make the connections between variables and functions in your program and the library files It is the job of the loader to make the connections between variable names and labels, and memory locations Linkers and Loaders
Just as with assembly code, a program written in a high-level language must also be translated into machine language This is the job of the compiler But the compiler has a much harder job Consider the following code: This is translated into at least 15 Intel assembly instructions! Usually compilers make multiple passes through a program progressively breaking into smaller chunks resulting eventually in a (possibly optimized) machine language program Compilers for(j=0;j<n;j++) if(a[j] > b[j] – k) c[k++] = a[j]; The steps of a compiler
The Run-Time Stack • We examine one last system oriented feature • The run-time stack is used to implement function calls for most languages • When a function is called, an “activation record instance” is pushed onto the stack • This record contains storage space for • All local variables • All parameters • The return address (where to return to when the function terminates) • The return value (if the function returns a value) • When a function is called, the OS uses a special register called the Stack Pointer (SP) to determine where this new activation record instance is pushed • When the function terminates, the PC is reset to be the return address, the return value is returned to the function/operation that called the function, and the activation record instance is popped off the stack, with the SP adjusted to the new top • NOTE: without the run-time stack, recursion is not possible!