HARDWARE IMPLEMENTATION OF TEA TINY ENCRYPTION ALGORITHM
HARDWARE IMPLEMENTATION OF TEA TINY ENCRYPTION ALGORITHM. ANOOP KUMAR PALVAI. The Tiny Encryption Algorithm (TEA) is one of the fastest and most efficient cryptographic algorithms in existence. Developed by Roger Needham and David Wheeler. OVERVIEW OF TEA. TEA is a symmetric key algorithm.

HARDWARE IMPLEMENTATION OF TEA TINY ENCRYPTION ALGORITHM
E N D
Presentation Transcript
HARDWARE IMPLEMENTATION OF TEA TINY ENCRYPTION ALGORITHM ANOOP KUMAR PALVAI
The Tiny Encryption Algorithm (TEA) is one of the fastest and most efficient cryptographic algorithms in existence. Developed by Roger Needham and David Wheeler.
OVERVIEW OF TEA TEA is a symmetric key algorithm. TEA is designed to minimize memory footprint and maximize speed. It is a Feistel type cipher that uses operations from mixed (orthogonal) algebraic groups. Achieves the Shannon's properties of complete diffusion and confusion with out the employment of S & P boxes, after only six rounds but thirty two rounds are recommended.
OVERVIEW Contd.. TEA seems to be highly resistant to differential cryptanalysis. TEA is a compromise for safety, ease of implementation, lack of specialized tables, and reasonable performance.
FUNCTIONALITY OF TEA Inputs to encryption algorithm are 64 bits of plain/cipher text , 128 bits of key and output is a cipher/plain text. It performs operations on 32 bit words. Each half of message is used to encrypt the other half over 64 rounds of processing and then combine to produce the cipher text block.
OPERATIONS PERFORMED IN A SINGLE ITERATION Each round i has inputs Left[i-1] and Right[i-1], derived from the previous round, as well as a sub key K[i] derived from the 128 bit overall K. The sub keys K[i] are different from K and from each other. The constant delta =(9E3779B9)h, is derived from the golden number ratio to ensure sub keys to be different.
DECRYPTION Decryption is essentially the same as the encryption process. The sub keys K[i] are used in the reverse order. It reduces the area required for implementation by half.
I IMPLENTATION IN HARDWARE
INPUT (H) INPUT (L) limit 000 S1 Sel Register 1 Register 0 SUM Delta S2 + A D Function E B C >>11 S2 se “AND” 3 K(0) K(1) K(2) K(3)
D A <<4 >>5 + B E + + C
St0 reset = ’1’ St1 s1=1, en1 =1, en2 =1,en4 =1 a = ‘0’ False Sel = 01 01 Sel =00 True St5 en2=1, en4=1, s1=1, s2=1 St2 en1=1, en4 =1, s1 = 1, s2=0 St6 en3 = 1, sel = 10 St3 en3 = 1, sel = 10 St7 en1=1, s1=1, s2=0 St4 en2=1, s1=1, s2=1 Sum = x00000000 Sum !=limit False True True False St8
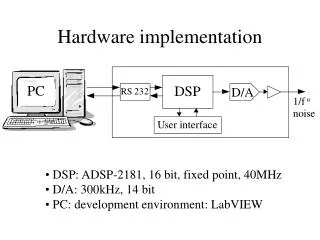
Tools Used • Aldec Active HDL 7.1 for simulation • Xilinx XST for synthesis • Xilinx ISE 8.2i for implementation • Device Utilization Summary • Device : xilinx Spartan3 xc3s1500-5fg456 • Number of Slice Flip Flops : 118 out of 26,624 1% • Total Number 4 input LUTs : 1,130 out of 26,62 4 % • Number of occupied Slices : 594 out of 13,312 4% • Number of bonded IOBs : 293 out of 333 87% • Number of MULT18X18s : 3 out of 32 9% • Total equivalent gate count for design: 20,489 • Minimum Time Period : 19.765 ns • Maximum Frequency : 50.6 MHz
Questions? Thank You