Analysis of the RSA Encryption Algorithm
160 likes | 205 Views
In this paper, the RSA encryption algorithm and its factorization process are analyzed, focusing on improving efficiency. The background, block ciphers, keys, encryption, decryption, and algorithm development are explored in detail.

Analysis of the RSA Encryption Algorithm
E N D
Presentation Transcript
Analysis of the RSA Encryption Algorithm Betty Huang Computer Systems Lab 2009-2010
Abstract The RSA encryption algorithm is commonly used in public security due to the asymmetric nature of the cipher. The procedure is deceptively simple, though; given two random (large) prime numbers p and q, of which n = pq, and message m, the encrypted text is defined as c = me (mod n). E is some number that is coprime to the totient(n). The public key (n, e), however, makes it difficult for the user to find the private key (n, d), due to the fact that given only n, it is extremely difficult to find the prime factors p and q. The fastest methods currently have O(sqrt(n)) complexity, but require expensive resources and technology (Kaliski). The aim of this paper is to improve on the factorization process required by the RSA encryption algorithm.
Background • Purpose of Encryption Algorithms • One-way functions • Hash functions: MD5, SHA family • Block Cipher: DES, Blowfish
RSA • Rivest, Shamir, Adleman • Asymmetric Block Cipher • Different Keys for Encryption/Decryption
Block Ciphers A block cipher consists of two paired algorithms, one for encryption, E, and the other for decryption, E-1. Both algorithms accept two inputs: an input block of size n bits and a key of size k bits, yielding an n-bit output block. For any one fixed key, decryption is the inverse function of encryption, so that for any block M and key K. M is termed the plaintext and C the ciphertext.
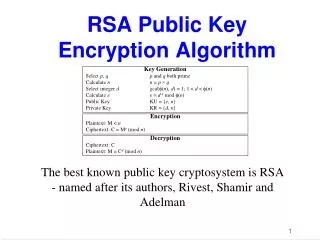
Process Initialization: • n = pq, with p and q primes • e relatively prime to φ(n) = (p − 1) (q − 1) • d inverse of e in Zφ(n) Keys: Public key: (n, e) Private key: (n, d) Encryption: Message M 1 < M < N C = M^e mod n Decryption: M = C^d mod n
An Example Keys: public key: (119, 5) private key: (119, 77) Encryption: M = 19 C = 195 mod 119 = 66 Decryption: C = 6677 mod 119 = 19 Setup: p = 7, q = 17 n = 7*17 = 119 φ(pq) = 6*16 = 96 choose e coprime to φ(pq) ex: e = 5 find d such that de = 1 (mod φ(pq)) d = 77
Algorithms Prime Generation Primality Tests (Miller-Rabin, etc) GCD Euler’s Totient Function Modular Multiplicative Inverse Chinese Remainder Theorem Integer Factorization
Development • GMP Library • RSA Algorithm Implementation • Integer Factorization
Development • Trial Division • Given a number n, test numbers less than n to find prime divisors
Development • Fermat’s Theorem • n = x2 – y2 • n = (x + y)(x – y) • Find s = (x - y), t = (x + y) • x = (s + t) /2, y = (t - s) / 2
Development • Pollard’s Rho Method sequence of pseudo-random integers constructed in the following way: x0 = random(0, N − 1) xi = f (xi−1 ) (mod N ), i = 1, 2, · · · where f is a polynomial with integer coefficients, eg. in most practical implementations of the algorithm f (x) = x2 + α, α = 0, -2
Results Factorization of Fermat 6: 264 + 1 = 18,446,744,073,709,551,617 Factors into: 274,177 × 67,280,421,310,721