CSC 311
CSC 311 CHAPTER ELEVEN INTERNET PROTOCOLS AND APPLICATIONS In this chapter we discuss THE INTERNET there can be many internets, but there is only one Internet We will be talking about TCP/IP Internet Protocol IP Transmission Control Protocol TCP

CSC 311
E N D
Presentation Transcript
CSC 311 CHAPTER ELEVEN INTERNET PROTOCOLS AND APPLICATIONS
In this chapter we discuss THE INTERNET • there can be many internets, but there is only one Internet • We will be talking about TCP/IP • Internet Protocol IP • Transmission Control Protocol TCP • Originally developed by the Department of Defense • DARPA, ARPANET • We currently run IPv4 but are in the process of switching to IPv6 CSC 311
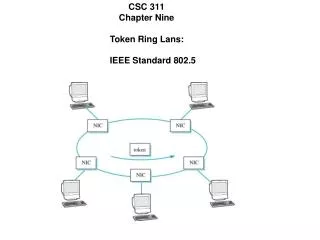
Overview of TCP/IP TCP Transmission Control Protocol IP Internet Protocol TCP provides connection oriented services for layer 5 of the protocol stack and relies on IP to route packets through the network Two ends that implement TCP execute a handshake that establishes a logical connection between them. Each side then executes flow control protcols, acknowledge segments, and responds to those that arrive damaged. UDP (User Datagram Protocol) is an alternative layer 4 protocol. Connectionless, no flow control, no guaranteed delivery. less overhead. CSC 311
CSC 311 Some of the protocols supported by TCP/IP
The Internet Protocol is a layer 3 protocol designed to provide a packet delivery service between two sites. It is commonly but not exclusively used with TCP CSC 311 Suppose two applications, A and B, need a connection-oriented service. TCP provides the reliable connection and IP handles routing through the different networks.
Internet Addressing to users, an internet address has the form: server.institution.domain This might appear in your email address as: user@server.institution.domain for browsers, the term www represents the default server at the specified location. periods are used to separate the terms. In this context, domain does not have the same meaning as that used in prior chapters. A DOMAIN is a collection of sites of a particular type. They have no geographic significance. Table 11.1 contains a list of domain names, some of which are new and may not be familiar to youl CSC 311
When the site is small and a default server is used, the server name can be omitted. We can have more components in this text address: example: www.legis.state.wi.us In this case, top domain is country us in this example it is divided into two subdomains: wi for Wisconsin the wi subdomain is further divided into “state” to indicate state offices the remaining components indicate the legislative branch and the default web server. These addresses are translated into actual internet addresses CSC 311
Current IPv4 Internet Addresses: Use dotted decimal notation. Actual address in a 32 value divided into 4 eight bit fields the address on the previous slide actually has an address of: 143.200.128.162 The maximum value in any of these fields is 255 which is the largest unsigned integer that can be represented with 8 bits. IP has several classes of internet addresses. CSC 311
Class A: 128 possible networks, with up to 16,777,216 nodes 0nnnnnnn xxxxxxxx xxxxxxxx xxxxxxxx Class B: 16,384 possible networks with up to 65,536 nodes 10nnnnnn nnnnnnnn xxxxxxxx xxxxxxxx Class C: 2,097,152 possible networks, with up to 256 nodes 110nnnnn nnnnnnnn nnnnnnnn xxxxxxxx Class D addresses used for multicasting 1110 followed by a 28 bit multicast address Class E reserved CSC 311
Classless Addresses: IPv4 is beginning to encounter problems. With 32 bits addresses, we could have over 4.3 billion unique addresses, but the class address system is inefficient, many addresses are wasted and we are starting to run out. Using the smaller class C addresses increases the number of network addresses that routers must deal with, thereby complicating the routing problem. One solution to the problem is a new addressing scheme: IPv6 uses 128 bit addresses. Another approach is to use classless addressing. Called the classless interdomain routing or CIDR, it is currently supported by BGP-4 (border gateway protocol version 4) CSC 311
How does CIDR work? It specifies a group of addresses that do not fall into any of the predefined classes, yet each address in the group can still be interpreted as a network number followed by a local identifier. The number of bits defining the network number varies to allow networks of varying size. It is commonly used to allocate multiple class C networks. Example: suppose and organization the need of up to 1000 stations. The CIDR approach would be to allocate four consecutive class C networks. Consider the following addresses: CSC 311
Class C Networks Bit Representation Address Range 211.195.8.0 11010011-11000011-00001000-xxxxxxxx 211.195.8.0 to 211.195.8.255 211.195.9.0 11010011-11000011-00001001-xxxxxxxx 211.195.9.0 to 211.195.9.255 211.195.10.0 11010011-11000011-00001010-xxxxxxxx 211,195.10.0 to 211.195.10.255 211.195.11.0 11010011-11000011-00001011-xxxxxxxx 211.195.11.0 to 211.195.11.255 In general, these Class C networks correspond to the contiguous set of addresses from 211.195.8.0 to 211.195.11.255 If you examine the addresses carefully, you will note that the first 22 bits of all four addresses are the same. So we can view any of these Class C networks as a 22 bit network address followed by a 10 bit local identifier. Furthermore, a router could extract the network number (in this case 211.195.8.0) via a logical AND between the 22 bit subnet mask and an IP address If we used 8 Class C addresses the first 21 bits would be the same an you could have 2K nodes For 16 Class C addresses the first 20 bits would be the same and you could have 4K nodes. CSC 311
How do routers extract the network address? The first three bits determine whether it is a Class A, B, or C address but what can be done when the number of bits in the network number varies, as it does with CIDR The router must know the number of bits in the network ID. Consequently, the usual representation of a network address, w.x.y.z is replaced by w.x.y.z./m, where m represents the number of bits in the network ID. For example, a router can represent the four networks above using the single entry: 211.195.8.0/22, the 22 indicates the network number is 22 bits long. CSC 311
There are international organizations that assign internet addresses and others that register domain names for a fee. These domains and IP addresses are kept in a distributed database, host computer calls on one of these databases to translate the text domain name into an internet address. CSC 311
CSC 311 Zones in a DNS hierarchy
CSC 311 An IP Packet Version: version of IP that created the packet Header Length: number of 32 bit words in the packet header Type of Service: packet handling requests. More recently QofS issues addressed by complex protocols. Packet Length: length of entire packet Identification, Flags, Fragment Offset: used in fragmentation Time to Live: max. time for packet to remain on the Internet. Protocol: Specifies higher layer protocol using IP Checksum: Used for error detection on the packet headers Source and Destination IP address. Options: Used to request special treatment.
Fragmentation: In transferring a packet across the Internet, many different network architectures may be encountered. These may require different packet sizes. In such instances, it may become necessary to break a packet into smaller packets. This process is called fragmentation. CSC 311
CSC 311 The packet’s identification value is placed into each packet’ Identification field. The flag field contains a more fragments bit mfb Each fragment will have an offset field to indicate where it goes in the reassembled packet. It measure offsets in units of 8 bytes.
IP Routing Relies heavily on RIP-2 and BGP protocols previously discussed. To get to the actual device on a LAN, we need a physical address rather than an IP address Answer: The router keeps tables correlating IP addresses of devices on its network to their physical addresses. The router, if it does not have this address, can obtain it by broadcasting the IP address on the network, the device which has that IP address will respond with its physical address. Obviously, we do not want to have to perform such broadcasts for every packet received, so the Router keeps a record of these responses. What happens if a network card in one of the machines needs to be replaced? The entries in the router database are purged periodically, so new network cards would be detected fairly quickly. Much like the process we discuss with bridge routing tables. CSC 311
Routers: • functions: • extract the destination address from the packet • find that address in the routing table • access the next hop value and determine the proper outgoing port • move the packet to a waiting queue for that port • transmit the packet CSC 311
CSC 311 put in other stuff next time
IPv6 CSC 311 As previously stated, IPv4 is showing signs of age. Many things in the field of telecommunications have changed since its inception. We are running out of addresses. mobile computing personal communication devices Streaming video requires attention to Quality of Service issues, etc.
IPv6 Packet Header format: CSC 311 There are fewer options in the header and the address fields have been expanded to 128 bits. The next header field allows insertion of an additional header between the standard header and the payload to provide information about options. At present, there are 6 types of extension headers.
IPv6 Addressing: Obviously, 128 bit addresses provide for substantially more addresses than IPv4. With IPv4 we had about 4.3 billion possible addresses. With IPv6 we have 2128 possible addresses, an almost unimaginably large number. In fact, if IPv6 possible addresses were spread out evenly over the surface of the earth, there would be 1024 addresses for each square meter of the earth’s surface, many more than the total number of IPv4 addresses currently available. It is inconceivable that this supply of addresses could ever be exhausted. Whereas IPv4 uses dotted decimal notation, IPv6 uses Hex/colon notation CSC 311
For example: • 7477:0000:0000:0000:0000:0AFF:1BDF:7FFFF • would be a valid IPv6 address • Obviously, writing so many values is cumbersome, so a shorthand • abbreviation has been provided. • runs of all zeros are not listed, a :: double colon implies that • the values between the colons are all zero. There could • be multiple zero fields. How many there are is calculated • by subtracting the number of digits that are present from 32, the • number of digits in a complete address. So the above address • would become: • 7477::0AFF:1BDF:7FFF • 2. leading zeros can also be omitted: • 7477::AFF:1BDF:7FFF CSC 311
This substitution can be made only once: Example 1DFG:0000:0000:0000:EDF2:0000:0000:E123 could only be shortened to: 1DFG::EDF2:0000:0000:E123 which could further be shorted to: 1DFG::EDF2:0:0:E123 CSC 311