453 Network Security
453 Network Security. Section 1: Introduction to Network Security Dr. E.C. Kulasekere Sri Lanka Institute of Information Technology - 2006. Text Books. Network Security: Private Communication in a Public World, Charlie Kaufman, Pearson Education Inc., 2002

453 Network Security
E N D
Presentation Transcript
453 Network Security Section 1: Introduction to Network Security Dr. E.C. Kulasekere Sri Lanka Institute of Information Technology - 2006
Text Books • Network Security: Private Communication in a Public World, Charlie Kaufman, Pearson Education Inc., 2002 • Network Security: A Complete Reference – Roberta Bragg, Mark Rhodes-Ousley, Keith Strassberg – Tata McGraw-Hill 2004. • Cryptography and Network Security/3e – William Stallings, Pearson Ed. 2003.
Syllabus • Foundations of computer and network security. • Access Control and Site Security. • Threats and vulnerabilities. • Attack Methods. • Technical defenses: authentication, operating system security, firewalls, etc. • Elements of Cryptography. • Cryptographic Systems: SSL/TLS, VPNs, Kerberos. • Application Security: Electronic Commerce and E-mail.
Syllabus … • Network vulnerability assessment and intrusion detection. • Remediation methods, including backup and repair strategies. • Business continuity planning and disaster recovery planning • Legal issues, privacy, cyber war and cyber terror.
Other Information • Web site: • http://www.ent.mrt.ac.lk/~ekulasek/ns • Email: • ekulasek@ent.mrt.ac.lk • Telephone: • Found at website. • All information will be updated on the website since I am a visiting instructor.
Expectation from Students • Friendly atmosphere in class. • Student involvement in discussions. • Complete laboratory work in time. • Do individual assignments by yourself and not copy. • Have an attitude that the course is for learning and not for passing exams.
Outline For this Section • Computer Security, Laws and Crime • Attacks, services and mechanisms • Security attacks and security services • Methods of defense • Model for internetwork security, Internet standards and Request for comments. • Cryptographic algorithms • Secure protocols • Authentication, access control.
Security is it a New Concept? • Lock the Doors and Windows. Control access • Role Based Access - Only Mom is allowed to enter • Don’t talk to strangers - even if you see some one you know Look beyond. • Don’t share your secrets – keep sniffers at bay • Don’t accept gifts from strangers • Play nice with others • Leave your valuables at home. Don’t steal • Keep your shots up to date • If you see something wrong, call the police.
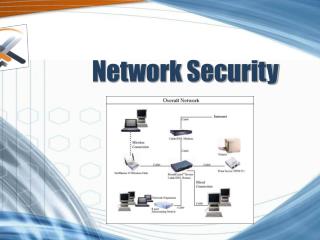
Levels of Security • Information security • Early days, security was provided by physical access restrictions. • With networking this changed. • Computer security • Restriction to shared resource • Physical security • Network security • Protection of data during transmission. • Infrastructure setup for security. Eg. Bastion host Are these definitions enough?
More Classifications • Three D’s of security • Detection: tool based by monitoring • Defense: patching and updating • Deterrence: laws and policy making • Classification based on business • Business agility • Return on investment • Risk management and business continuity planning • Customer confidence
Attack, Services and Mechanisms • Security attack: any action that will compromise the security of information. • Security mechanism: A mechanism that is designed to detect , prevent, or recover from a security attack. • Security services: A service that enhances the security of data processing systems and information transfers. A security service makes use of one or more security mechanisms.
Security Attacks Normal flow of Information source destination
Security Attacks … • Unauthorized party gets access to information • This is an attack on confidentiality • The attacker could be a person or program. • Eg. of this could be unauthorized copying of files. Interception
Security Attacks … • The system is destroyed or becomes unavailable • This is an attack on availability. • This could be a destruction of a piece of hardware or cutting a communication line. Interruption
Security Attacks … Modification • An unauthorized party gains access to information and also modifies it. • This is an attack on integrity of information. • Modification of program or date files to operate or contain different information.
Security Attacks … Fabrication • An unauthorized party injects fabricated information into the system. • This is an attack on authenticity. • Examples of this is insertion of spurious messages, addition of records to a file etc.
Attack Types • Passive Attack: • This type of attack does not involve the parties concerned. • Does not alter the information flowing between the parties. • Active Attack • This type of attack involves the other parties concerned. • The information flow is altered.
Passive Attack • This type of attacks are hard to detect since it does not involve the other party or alter the data. • This kind of attack can be prevented rather than detected. • Examples are Eavesdropping or monitoring of traffic. • The objective of the opponent is to obtain the information that is being transmitted. • Release of message content – Opponent getting to know the contents. • Traffic analysis – the link traffic profile and information gathering is done by the opponent.
Active Attack • This is easier to detect since the information stream is altered and involves the other party. • Harder to prevent since no absolute protection is available with the current buggy systems. • Involves some modification of the data stream or creation of a false stream. • Masquerading – The entity pretends to be a different entity. Eg. Use a sniffer on a telnet stream • Replay – passive capture of data, alter and then retransmit.
Security Services • Confidentiality (privacy) – is the protection of transmitted data from passive attacks. • Authentication (who created or sent the data) – is assuring that the communication is authentic. • Integrity (has not been altered) – will ensure that the messages are received with no duplication, insertion, modification. Reordering or replays. • Connection oriented service – addresses DoS and modifications (duplication, insertion, modification and reordering problems handled). • Connectionless service - deals with only individual messages and only assures against modification. This is because it only deals with individual packets.
Security Mechanisms • Separation • Physical separation • Temporal separation • Logical separation • cryptographic separation • combinations of all above • Share all or nothing • share via access limitations • share by capabilities (tokens) • limit use of an object
Design Issues in the Model • Design an algorithm for performing the security-related transformation. The algorithm should be such that an opponent cannot defeat its purpose. • Generate the secret information to be used with the algorithm. • Develop methods for the distribution and sharing of the secret information. • Specify a protocol to be used by the two principles that makes use of the security algorithm and the secret information to achieve a particular security service.
Other Considerations • Network Design Considerations • Designing for acceptable risk. • Use of network models with security (LAN/WAN more secure?, Dedicated/non-dedicated?, segregation and isolation) • Host hardening • Firewalls, Packet filtering • Choice of network devices • Choice of routers and other hardware • Routing protocols • Intrusion detection systems (IDS) • Host based IDS • Network based IDS
Security HighlightedKevin Mitnick • FBI arrested Kevin in February 1995 • stealing 20,000 credit-card numbers through the Internet. Valued at over one million dollars. • broke into the computer of Tsutomu Shimomura, a computer-security expert. • managed to get access to a set of utility programs, that would basically give him the tools necessary to break-in almost anywhere. • may have distributed these tools to other hackers.
The Downside!! • Kevin served five years in a Federal correctional institution before being released in January 2000. • Now charges $15,000 for a one hour talk !!
Security Highlighted - Kevin Mitnick • FBI arrested Kevin in February 1995 • stealing 20,000 credit-card numbers through the Internet • valued at over one million dollars.