COMP 416b Internet Protocols and Software
COMP 416b Internet Protocols and Software. Instructor: Zhijun Wang Quiz#2 including lectures 5-7 will be given next lecture (Nov.12) Today’s contents Host Configuration: BOOTP and DHCP (Chap.16) DNS (Chap.17) Email (Chap. 20) SNMP (Chap. 21). Chapter 16. Host Configuration:

COMP 416b Internet Protocols and Software
E N D
Presentation Transcript
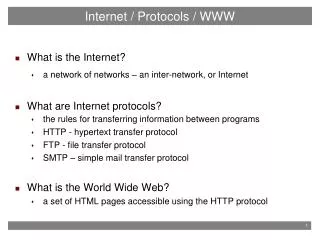
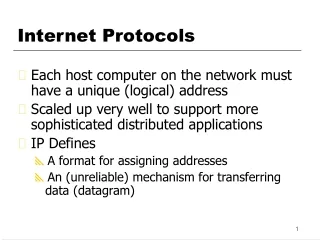
COMP 416b Internet Protocols and Software Instructor: Zhijun Wang Quiz#2 including lectures 5-7 will be given next lecture (Nov.12) Today’s contents • Host Configuration: BOOTP and DHCP (Chap.16) • DNS (Chap.17) • Email (Chap. 20) • SNMP (Chap. 21) TCP/IP Protocol Suite
Chapter 16 Host Configuration: BOOTP and DHCP Objectives • Know the types of information required by a system on boot-up • Know how BOOTP operates • Know how DHCP operates • Understand the differences between BOOTP and DHCP • Understand the DHCP transition state diagram TCP/IP Protocol Suite
What does a computer need to communication with other computers? • The IP address of the computer • The subnet mask of the computer • The IP address of the router • The IP address of the name server This information usually stored in a configuration file by a disk and accessed by the computer during the bootstrap. TCP/IP Protocol Suite
But what about a diskless computer or a computer with a disk that is booted for the first time? • Bootstrap protocol (BOOTP) BOOTP is a client/server protocol designed to provide the four pieces of information for a diskless computer or a computer that is booted for the first time. TCP/IP Protocol Suite
BOOTP and RARP Client and server RARPcan solve the IP address. Why do we need BOOTP? The RARP client and server must be in the same network. The BOOTP client and server can be in the different networks. Client and Server in the same network Port number Destination IP address Source IP address TCP/IP Protocol Suite
Client and server in the same network • Operations of BOOTP for client and server in the same network: • The BOOTP server issues a passive open command on UDP port number • 67 and waits for a client. • A booted client issues an active open command on port number 68. The • message is encapsulated in a UDP user datagram, using the destination • and source port number 67 and 68. The UDP user datagram is encapsulated • in an IP datagram. The client uses all 0s as the source IP address and all 1s • as the destination IP address. • The server responds with either a broadcast or a unicast message • using a UDP source and destination port numbers 67 and 68. TCP/IP Protocol Suite
Client and server on two different networks An IP address with all 1s is broadcast within a network.A host or a router needs to be configured as a relay agent to relay the message to other networks. The relay agent knows the unicast address of the BOOTP server. When the relay agent receives a broadcast request message, it sends the message to the BOOTP server and send the reply back when it gets the replay message from the server. TCP/IP Protocol Suite
BOOTP packet format • Operation codedefines • the BOOTP packet type: • request • reply TCP/IP Protocol Suite
16.2 DHCP The Dynamic Host Configuration Protocol (DHCP) provides static and dynamic address allocation that can be manual or automatic. Dynamic address means the pair of IP address and physical address can be dynamically changed. Physical address is fixed for a device. Why do we need DHCP? Not enough IP address in a network. User’s mobility. TCP/IP Protocol Suite
Address allocation There are two methods to allocate IP address for DHCP: static and dynamic. Static address allocation in DHCP just likes BOOTP. A DHCP server has a database that statically binds physical addresses to IP addresses. In dynamic address allocation, DHCP has two databases. The static database stores the pair of IP address and physical address. The other stores a pool of available IP addresses. When a client sends a request to a DHCP server, the server first checks its static database, if there is an entry for the client in the database, the permanent IP address is sent back. Otherwise, the server selects an available IP address and assign to the client. TCP/IP Protocol Suite
DHCP packet TCP/IP Protocol Suite
Example of Exchanging messages TCP/IP Protocol Suite
Chapter 17 Domain NameSystem: DNS Objectives • Understand how the DNS is organized • Know the domains in the DNS • Know how a name or address is resolved TCP/IP Protocol Suite
When you access a website e.g. www.google.com, how does your computer work? • Your computer needs to communicate with a google server • Your computer needs the IP address of google server. • The IP address is solved by domain name system (DNS) TCP/IP Protocol Suite
17.1 NAME SPACE The names assigned to machines must be unique because the addresses are unique. A name space that maps each address to a unique name can be organized in two ways: flat or hierarchical. In a flat name space, a name is assigned to an address. A name in this space is a sequence of characters without structure. In a hierarchical name space, each name is made of several parts. The first part can define the nature of the organization, the second part can define the name of an organization, the third part can define department in the organization and so on. For example, www.comp.polyu.edu.hk TCP/IP Protocol Suite
17.2 DOMAIN NAME SPACE The domain name space is hierarchical in design. The names are defined in an inverted-tree structure with the root at the top. The tree can have 128 levels: level 0 (root) to level 127. Domain name space TCP/IP Protocol Suite
Domain names and labels Each node in the tree has a label, which is a string with a maximum of 63 characters. The root label is a null string (empty string). DNS requires that children of a node have different labels, which guarantees the unique of the domain names. A full domain name is sequence of labels separated by dot (.). The domain name are always read from node up to root. TCP/IP Protocol Suite
FQDN and PQDN The root node is a null label. If a label is terminated by a null string, it is called a fully qualified domain name (FQDN). A FQDN contains the full name of a host and ends with a dot. If a label is not terminated by a null string, it is called a partially qualified domain name (PQDN). A PQDN starts from a node, but it does not reach the root. FQDN PQDN www.comp.polyu.edu.hk. www.yahoo.com. www.mit.edu. www.comp.polyu.hk www www.polyu.edu.hk TCP/IP Protocol Suite
Domains A domain is a subtree of the domain name space. The name of the domain is the domain name of the node at the top of the subtree. TCP/IP Protocol Suite
17.3 DISTRIBUTION OF Distributed NAME SPACE The information contained in the domain name space is distributed among many computers called DNS servers. Hierarchy of name servers TCP/IP Protocol Suite
Zones and domains What a server is responsible for or has authority over is called a Zone. A zone can be defined as a contiguous part of the entire tree. If a domain has only one zone, they are the same. A root server is a server whose zone consists of the whole tree, the root server usually does not store any information about domains but delegates its authority to other servers. A primary server is a server that stores a file about the zone for which it is an authority. A secondary server is a server that transfers the complete information about a zone from another server and store the file on its local disk. A primary server loads all information from the disk file; the secondary server loads all information from the primary server. When the secondary downloads information from the primary server, it is called zone transfer. TCP/IP Protocol Suite
17.4 DNS IN THE INTERNET The domain name space (tree) is divided into three different sections: generic domains, country domains, and the inverse domain. DNS used in the Internet TCP/IP Protocol Suite
Generic domains Generic domains define registered hosts according to their generic behavior. Each node in the tree defines a domain, which is an index to the domain name space database. TCP/IP Protocol Suite
Table Generic domain labels -14 labels TCP/IP Protocol Suite
Country domains Country domain section users use two-character country abbreviations (e.g., hk for Hong Kong). Second-labels can be organizational, or they can be more specific, national designations. TCP/IP Protocol Suite
Inverse domain The inverse domain is used to map an address to a name. The inverse domain is added to the domain name space with the first level node called arpa. The second level is also one single node named in-addr (for inverse address). The rest of the domain defines IP Addresses. TCP/IP Protocol Suite
17.5 RESOLUTION Mapping a name to an address or an address to a name is called name-address resolution. DNS is designed as a client-server application. A host that needs to map an address to a name or a name to an address calls a DNS client called a resolver. Three methods: recursive resolution, iterative resolution and cache. Cache: when a server asks a mapping from another server and receives the responds, it stores this information in its cache memory before sending to the client. If the same or another client asks for the same mapping, it can check its cache memory and resolve the problem. TCP/IP Protocol Suite
Recursive resolution The client (resolver) can ask for a recursive answer from a name server. This means that the resolver expects the server to supply the final answer. If the server is the authority for the domain name, it checks its database and responds. If the server is not the authority, it sends the request to another server and waits for the response. mcgraw.com TCP/IP Protocol Suite
Iterative resolution If the client does not ask for a recursive answer, the mapping can be done iteratively. If the server is an authority for the name, it sends the answer. If it is not, it returns the IP address of the server it thinks can resolve the query mcgraw.com TCP/IP Protocol Suite
17.6 DNS MESSAGES The DNS query message consists of a header and question records; the DNS response message consists of a header, question records, answer records, authoritative records, and additional records. DNS messages include query and response messages. DNS messages TCP/IP Protocol Suite
Query and response messages and header format TCP/IP Protocol Suite
17.10 ENCAPSULATION DNS uses UDP as the transport protocol when the size of the response message is less than 512 bytes. If the size of the response message is more than 512 bytes, a TCP connection (port 53) is used. TCP/IP Protocol Suite
Chapter 20 Electronic Mail: SMTP, POP, and IMAP Objectives • Understand four configurations of email architecture • Understand the functions and formats of a user agent • Understand MIME and its capabilities and data types • Understand the functions and commands of an MTA • Understand the function of POP3 and IMAP4 TCP/IP Protocol Suite
Email Architecture - Scenario I The sender and the receiver of the email are users (or application programs) are in the same system. The administrator creates one mail box for each user where the received message are stored. A mail box is a part of hard drive, a special file with permission restrictions. Only the own can access to it. The program running for receiving or sending email is called user agent (UA). When the sender and the receiver of an email are on the same system, we need only two UAs. TCP/IP Protocol Suite
Scenario-II The sender and the receiver of an email are users (or application programs) on the two different systems. We need two UAs and one message transfer agent (MTA). MTA is responsible for email delivery from one system to the other. TCP/IP Protocol Suite
Scenario-III Thesender and receiver of an email are users on different systems, and the sender is connected to the mail server via LAN or a WAN. In this case, we need two UAs and two pairs of MTAs (client and server). TCP/IP Protocol Suite
Scenario-IV The sender and receiver of an email are users who are connected to their servers by a LAN or WAN. In this case, we need a message access agent To store received emails. Hence, we need two pairs of MTAs and a pair of MAAs. This is the most common situation today. push pull TCP/IP Protocol Suite
20.3 MESSAGE TRANSFER AGENT: SMTP The actual mail transfer requires message transfer agents (MTAs). The protocol that defines the MTA client and server in the Internet is called Simple Mail Transfer Protocol (SMTP). Position of SMTP TCP/IP Protocol Suite
Commands and responses SMTP uses commands and responses to transfer messages between an MTA client and an MTA server. Each command or reply is terminated by A two-character (carriage return and line feed) end-of-line token. Command format TCP/IP Protocol Suite
Connection establishment After a client made a TCP connection to the well-known port 25, the SMTP Servers starts the connection phase which involves three steps as below. TCP/IP Protocol Suite
Connection termination After the message is transferred successfully, the client terminates the Connection. This involves two steps as below TCP/IP Protocol Suite
Example 1 Let us see how we can directly use SMTP to send an email and simulate the commands and responses we described in this section. We use TELNET to log into port 25 (the well-known port for SMTP). We then use the commands directly to send an email. In this example, forouzanb@adelphia.net is sending an email to himself. The first few lines show TELNET trying to connect to the adelphia mail server. $ telnet mail.adelphia.net 25Trying 68.168.78.100...Connected to mail.adelphia.net (68.168.78.100). After connection, we can type the SMTP commands and then receive the responses as shown below. We have shown the commands in black and the responses in color. Note that we have added for clarification some comment lines, designated by the “=” sign. These lines are not part of the email procedure. TCP/IP Protocol Suite
Example 1 (Continued) ================== Connection Establishment ================220 mta13.adelphia.net SMTP server ready Fri, 6 Aug 2004 . . .HELO mail.adelphia.net250 mta13.adelphia.net===================== Envelope ===================MAIL FROM: forouzanb@adelphia.net250 Sender <forouzanb@adelphia.net> OkRCPT TO: forouzanb@adelphia.net250 Recipient <forouzanb@adelphia.net> Ok=================== Header and Body ==================DATA354 Ok Send data ending with <CRLF>.<CRLF>From: ForouzanTO: ForouzanThis is a test messageto show SMTP in action.. TCP/IP Protocol Suite
Example 1 (Continued) ============= Connection Termination=============== 250 Message received: adelphia.net@mail.adelphia.net QUIT 221 mta13.adelphia.net SMTP server closing connection Connection closed by foreign host. TCP/IP Protocol Suite
20.4 MESSAGE ACCESS AGENT: POP AND IMAP The third stage of mail delivery uses a message access agent; the client must pull messages from the server. Currently two message access protocols are available: Post Office Protocol, version 3 (POP3) and Internet Mail Access Protocol, version 4 (IMAP4). Position of POP3 and IMAP4 TCP/IP Protocol Suite
Figure 20.20POP3 TCP/IP Protocol Suite
Chapter 21 Network Management: SNMP Objectives • Understand the SNMP manager and the SNMP agent • Understand the roles of SMI and MIB in network management • Be familiar with SMI object attributes and encoding methods • Know how an MIB variable is accessed • Be familiar with the SNMP PDU and format TCP/IP Protocol Suite
21.1 CONCEPT Simple network management protocol (SNMP) is a framework for managing devices in an Internet using TCP/IP protocol suite. It defines a manager, usually a host, that controls and monitors a set of agents, usually routers. SNMP is an application layer protocol in which a few manager stations control a set of agents. A management station, called a manager, is a host that runs the SNMP client program. A managed station, called agent, is a router (or host) that runs the SNMP server program. Management is achieved through simple information between a manager and an agent. TCP/IP Protocol Suite
21.2 MANAGEMENT COMPONENTS SNMP requires the use of two other protocols: Structure of Management Information (SMI) and Management Information Base (MIB). Network management on the Internet is done through the cooperation of SNMP, SMI, and MIB. TCP/IP Protocol Suite
Roles of three protocols SNMP defines the format of packets exchanged between a manager and an agent. It reads and changes the status (values) of objects (variables) in SNMP packets. SMI defines the general rules for naming objects, defining object types (including range and length), and showing how to encode objects and values. SMI defines neither the number of objects an entity should manage, nor names the objects to be managed nor defines the association between the objects and their values. MIB creates a collection of named objects, their types, and their relationships to each other in an entity to be managed. We can compare the task of network management to the task of writing a program. ❏Both tasks need rules. In network management this is handled by SMI.❏ Both tasks need variable declarations. In network management this is handled by MIB.❏ Both tasks have actions performed by statements. In network management this is handled by SNMP. TCP/IP Protocol Suite