Leader Election
Leader Election. Bernard Chen. Outlines . Introduction to leader election Complete Topology Logical Ring Topology Tree Topology Secure Extrema Finding Algorithm (SEFA) References. What is leader selection?.

Leader Election
E N D
Presentation Transcript
Leader Election Bernard Chen
Outlines • Introduction to leader election • Complete Topology • Logical Ring Topology • Tree Topology • Secure Extrema Finding Algorithm (SEFA) • References
What is leader selection? • The existence of a centralized controller greatly simplifies process synchronization • However, if the central controller breaks down, the service availability can be limited • The problem can be alleviated if a new controller (leader) can be chosen
When do we need leader election? • 1. The initiation of a system of processes • 2. When an existing leader fails (The detection of failures is normally based on a time-out mechanism)
Two Types of Election Criteria • 1. a leader election can be based on a global priority. This type of election is called extrema finding. (Every node has a fixed evaluation value) • 2. processes in the group can vote for a leader based on a node’s preference, it’s called a preference-based leader election algorithm.
Leader Election vs. Mutual Exclusion • In many aspects, leader election and mutual exclusion are the same; they both try to reach an agreement for identifying a unique process • However, there are some differences
Leader Election vs. Mutual Exclusion • The two major differences are: • A mutual exclusion must ensure that no process is starved, while a leader election is more concerned with the fast and successful termination of the election process • Another distinction is that the result for leader election need to be announced to all processes
Outlines • Introduction to leader election • Complete Topology • Logical Ring Topology • Tree Topology • Secure Extrema Finding Algorithm (SEFA) • References
Complete Topology • In a complete topology, each process in the group can reach any other process in the same group in onemessage hop. • Each process as a global priority, and the highest-priority is elected leader
The Bully Algorithm • It’s a extrema-finding algorithm • A process starts a leader election if it suspects that the coordinator has failed. • If a process Pheavy receives an election message from a lighter process Plight, it sends a take-over message to Plight. Plight is out of the race. • If a process doesn’t get a take-over message back, it wins, and sends a victory message to all other processes.
The Bully Algorithm • The bully election algorithm • Process 4 holds an election • Process 5 and 6 respond, telling 4 to stop • Now 5 and 6 each hold an election
The Bully Algorithm • Process 6 tells 5 to stop • Process 6 wins and tells everyone
Outlines • Introduction to leader election • Complete Topology • Logical Ring Topology • Tree Topology • Secure Extrema Finding Algorithm (SEFA) • References
Logical Ring Topology • A logical ring is easy to construct and offers the unique property that a message initiated by any node will return to the node, indicating completion of a round of broadcast
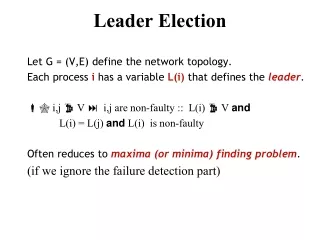
Leader Election • Initiation: • A process sends an ELECTION message to its successor (or next alive process) with its ID • Each process adds its own ID and forwards the ELECTION message • Leader Election: • Message comes back to initiator • Initiator announces the winner by sending another message around the ring
Outlines • Introduction to leader election • Complete Topology • Logical Ring Topology • Tree Topology • References
Tree Topology • To construct a logical ring structure is easy if the underlying network supports broadcast facilities • However, in Ad Hoc networks, user mobility may results in frequent leader election, making the process a critical component of system operation
Leader election in Ad Hoc networks • Most of the leader election algorithms for mobile ad hoc networks elect a “random” leader and hence are not extrema-finding • SEFA (Vasudevan S., 2003) is a round-based hierarchy-building approach which also considered secure problem • Good reviews can be found in [3](G. Tel. 2000) and [4](N.Lynch 1996)
Secure Extrema Finding Algorithm (SEFA) • SEFA is an extrema-finding algorithm in which all nodes use a Common Election Algorithm (CEA) to determine their rank • Decision factors might include node identity, battery lifes, or level of trust…etc • Larger the CEA value, the more “desirable” the node is a leader
Outlines • Introduction to leader election • Complete Topology • Logical Ring Topology • Tree Topology • Secure Extrema Finding Algorithm (SEFA) • References
References • Chow, Randy, et. al.,Distributed Operating Systems & Algorithms, Addison Wesley, March 18, 1997 • Vasudevan, S.; DeCleene, B.; Immerman, N.; Kurose, J.; Towsley, D.; “Leader election algorithms for wireless ad hoc networks”, DARPA Information Survivability Conference and Exposition, 2003. Proceedings • G. Tel. Introduction to Distributed Algorithms. Second Edition, 2000. Cambridge University Press • N.Lynch Distributed Algorithms. 1996, Morgan Kaufmann Publications • V. Park and M. Corson. A Highly adaptive Distributed Routing Algorithm for mobile Wireless Networks. In proceediing of IEEE INFOCOM, April 1997
Thank You • Questions??