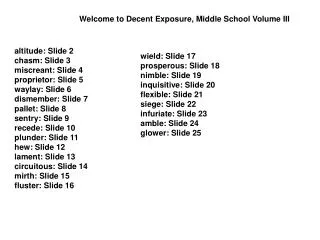
‘Sentry’
‘Sentry’. Information Leakage and Loss . Data Loss, Theft and Leakage happen in a number of environments and for a number of reasons. To combat many of these, ‘Sentry’ performs quickly and effectively in: Panic Situations

‘Sentry’
E N D
Presentation Transcript
Information Leakage and Loss Data Loss, Theft and Leakage happen in a number of environments and for a number of reasons. To combat many of these, ‘Sentry’ performs quickly and effectively in: • Panic Situations Loss or theft of a mobile computer where its whereabouts are unknown. • Critical Situations Internal staff theft - widely perceived to be a major source of sensitive data leakage. • Controlled Situations Employment Termination All too often when an employee leaves a position, for whatever reason, they take the employer’s data with them. Computer Replacement Programmes When an organisation / person replaces its computers they are often dispatched with inadequate or no measures taken to cleanse them of data.
What is ‘Sentry’ ‘Sentry’ is a simple but effective tool that securely eradicates computer data that may be at risk of moving out of its owner’s control.
Mobile Data – Panic Application • Your device is missing, lost or stolen. • It contains gigabytes of information some of which is inevitably sensitive. • Whatever security tools are installed none provide any information to help manage the situation. • ‘Sentry’ works quickly, instructing the device to self-destruct & proving it has done so, allowing effective crisis management.
Mobile Data – Critical Application • When an organisation suspects that an employee is acting against its interests it needs to respond quickly. • Most organisations accept that employees remove information and pass it to unwanted sources. • Equally employees store an organisation’s information at a third party site for use post employment. • ‘Sentry’ can be used in-house to quickly shut down a rogue employee.
Mobile Data – Controlled Application • Employment Termination • When an employee leaves or is removed from position the organisation must ensure that any information on his/her computer is erased before it is compromised. • Computer Replacement Programme • As organisations replace and renew their computers they need to take adequate measures to make sure the information on the computer is erased before it is dispatched. • ‘Sentry’ can be used in-house to perform an unrecoverable delete on all desktops and laptops in just a couple of minutes.
What makes ‘Sentry’ so effective? • ‘Sentry’ is an invisible application that waits for an instruction to destroy the data contents on the computer it is protecting. • It eliminates human error by having no user interaction, there are no passwords to enter or programmes to start, ‘Sentry’ is always working when the computer is. • ‘Sentry’ needs no hardware other than its host computer. • No restrictions, ‘Sentry’ protects all data regardless of its location on the device. • ‘Sentry’ is a hosted service meaning there is no expensive infrastructure to install or maintain.
Why ‘Sentry’ over traditional security tools? Password, 2a4n5d7y ***************** • ‘Sentry’ is not meant to replace existing data protection strategies or tools and acts as a powerful layer in a complete data protection strategy. • Currently accepted tools such as encryption, require user intervention, either to enter complicated passwords or insert external plug in hardware. • End users often render these tools useless by recording the password and storing it or the plug in device, with the laptop, stripping the tool of its functionality. • Protected data is good, NO data is best. • ‘Sentry’ deletes ALL data, protected or not.
The ‘Sentry’ Process Data Vault Security ‘Sentry’ Issues Self Destruct Command To Required Computer. Authorised Internal ‘Sentry’ Operator or Data Vault Security is asked to destroy a particular device. Device receives ‘Sentry’ delete Instruction and shuts down. Whatever the circumstance, Panic, Critical or Controlled ‘Sentry’ works in the same way. The authorised operator identifies the relevant device through the ‘Sentry’ service and quickly issues a request to erase all sensitive data. When the command reaches the device the data is eradicated and the proof is delivered to the relevant parties almost immediately.
How does ‘Sentry’ work? COMMUNICATION CHANNELS • Mobile Broadband • All Other Broadband • WI-FI / WI-MAX • Intranet • Extranet ‘Sentry’ Client’s Device Hosted ‘Sentry’ service • ‘Sentry’ uses whichever communications channels an organisation uses to deliver the decommission instruction to the device. • Whichever channel reaches the device first will trigger ‘Sentry’ and the data will be deleted. • For mobile workers ‘Sentry’ uses the worldwide mobile broadband infrastructure as standard as well as the internet, meaning that a lost device can be contacted almost anywhere on earth.
Unrecoverable Data Deletion • All selected data is deleted to the US Department of Defence 5220(M) standard which means it is effectively unrecoverable to all but the most sophisticated security organisations. • ‘Sentry’ finishes the job by rendering the operating system inactive, leaving the device completely useless.
Data Vault Security ‘Sentry’ Audit Trail • Traditional tools require a leap of faith that the data is safe because there is no information about the device – it is simply missing. • The ‘Sentry’ comprehensive decommission report proves that the data cannot be compromised and that the measures taken to achieve this have succeeded. • The report shows a list of ALL files deleted, when, and very importantly, whether any were accessed in the time that the device was missing and unreached by ‘Sentry’. • Culprit Identification and Device Location are also available.
Summary of Benefits at a Glance • ‘Sentry’ uses and will always use the fastest communications methods available to communicate with a computer, whatever the reason for the decommission. • ‘Sentry’ gives control to its users. No need to notify police or other authorities. • After purchase ‘Sentry’ is free to use – there are NO additional costs. • ‘Sentry’ is always active when its host computer is. When it receives a decommission instruction ‘Sentry’ works quickly to leave the computer risk free. • On a typical computer ‘Sentry’ can destroy 500 MB of data made up of more than 4500 documents (2380 Word docs, 2127 Spreadsheets and several hundred emails) in 103 seconds, too fast for the data to be seriously compromised. • ‘Sentry’ can be integrated with Data Vault Security ‘Backup’ for ultimate protection.
‘Sentry’ Wi-Fi / RFID integration • ‘Sentry’ can be triggered by a location based RFID/Wi-FI system to destroy the data on a computer that leaves an authorised zone in a building or compound, for example a hospital. • Where appropriate ‘Sentry’ can be set to simply inform the user of a potential breach and compromise situation by text message or e-mail and await instruction to delete the data if necessary.
‘Sentry’ ticks all the boxes • ‘Sentry’s integrated volume encryption or Full Disk Encryption integration make efforts to get round ‘Sentry’ extremely difficult. • ‘Sentry’ integrates with leading data back up tools to provide an excellent route back to productivity in the shortest time possible. • ‘Sentry’ can be used as a proactive tool, for example with its device vacation functionality that searches for the device in designated downtimes such as user holidays. • ‘Sentry’ is a low cost insurance layer to help an individual or organisation keep its data for its own use only.