Fundamentals of Radio Frequency Communications and Wireless Security
This session provides an overview of basic concepts in wireless security, focusing on the vulnerabilities, threats, and attacks against wireless networks. Attendees will learn about the critical principles of confidentiality, integrity, availability, and privacy in the context of wireless communication. The session also explores different wireless technologies, including RFID, Bluetooth, ZigBee, and more, and addresses specific vulnerabilities related to mobility and device theft. Key security measures will be discussed, equipping participants with foundational knowledge to enhance wireless network security.

Fundamentals of Radio Frequency Communications and Wireless Security
E N D
Presentation Transcript
Basic radio frequency communications - 2 Session 1
Contents • Basic security concepts • Attacks against wireless networks • Wireless technologies • Classification according to the range
Basic security concepts • Vulnerability • An inherent weakness in the design, configuration, implementation of a network or system • This can take any form and can be intentional, accidental, or simply an act of nature • Threat • Any possible event that can disrupt the operation, functioning, integrity, or availability of a network or system
Basic security concepts • Attack • A specific technique used to exploit a vulnerability • Example • A threat could be a denial of service • A vulnerability is in the design of a communication system • An attack could be jamming
Basic security concepts • Confidentiality • Providing confidentiality means hiding the information from an unauthorized third party • Integrity • Ensuring data integrity means protecting data from being modified without authorization • Availability • The wireless network should be always available to be used
Basic security concepts • Privacy • Ensuring privacy means hiding the user identity, location or service usage • Authentication • Process that ensures that only legitimate users (possessing certain credentials) can access the wireless network
Basic security concepts • Access Control • Process that grants a legitimate user access to certain information that he/she is allowed to access • Non-repudiation • Activities that prevent users from denying the use of wireless networks
Attacks against wireless networks • Passive attacks (1) • Channel eavesdropping • An attacker can place an antenna to hear the information between the victim transmitter and receiver • Channel overuse • The radio spectrum is a shared resource • A wireless operator or a user may make an excessive use of the radio spectrum and prevent others from accessing it
Attacks against wireless networks • Passive attacks (2) • Traffic analysis • An analysis that shows characteristics of the traffic, e.g. how frequently the communication takes place • Active attacks (1) • Channel jamming • Part of denial of service attacks • Performed by transmitting at the same time in the same communication channel as the victim
Attacks against wireless networks • Active attacks (2) • Identity cheat • An attacker impersonates a legitimate user in the wireless networks • Spoofing • An attacker retrieves data and sends other data to the victim user • Data alteration • An attacker modifies the content of the information
Attacks against wireless networks • Specific vulnerabilities of wireless networks regarding mobility, i.e. the fact that a device can roam across different wireless networks and network operators (1) • Privacy of a user is threatened • Mobile device is small • Limited storage, computing power and energy • Strong protection measures (e.g. strong cryptography) are difficult to implement
Attacks against wireless networks • Specific vulnerabilities of wireless networks regarding mobility, i.e. the fact that a device can roam across different wireless networks and network operators (2) • Mobile device can be easily stolen • This may lead to misuse and reverse engineering
Wireless technologies • RFID • Personal networks • Bluetooth (IEEE 802.15.1) • ZigBee (IEEE 802.15.4) • Wireless LAN (IEEE 802.11) • Cellular networks • GSM • UMTS (3G)
Wireless technologies • Wireless mesh networks • Mobile ad hoc networks • Hybrid ad hoc networks • Vehicular networks • Sensor networks • Integrated networks
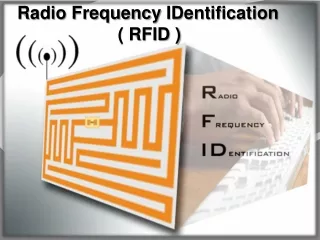
RFID • RFID (Radio Frequency Identification) • Serves for automatic and secure reading of an ID-number • There are also RFID devices capable of storing data – wireless memory (e.g. electronic passports) • Applications (http://www1.nrk.no/nett-tv/klipp/164552) • Logistics • Ticketing • Transport (e.g. Autopass), etc.
RFID • Operation • An RFID tag is mounted on the object to be identified • The tag consists of a chip and an antenna • Energy needed for operation of the tag is (usually) received from the reader – a radio transmitter • When the tag finds itself in the field of the reader’s radio signal, it transmits an echo • The echo is checked in the reader’s database and thus the object is identified.
Personal networks • Bluetooth • A short-range communications system intended to replace the cables connecting portable and/or fixed electronic devices. • The system offers services that enable the connection of devices and the exchange of data between these devices.
Personal networks • Bluetooth
Personal networks • ZigBee • A short-range communication system intended to facilitate communication between various technical devices, tipically home appliances. • Simpler messages than Bluetooth • More scalable than Bluetooth
Wireless LAN • Wireless LAN enables connectivity of computing devices (PCs, laptop, printers, etc.) by means of a radio link • Such a connection is transparent for the users • There is no logical difference between a wired and a wireless connection.
Cellular networks • Cellular network • A radio network made up of a number of radio cells, each served by a fixed transmitter, known as a base station. • These cells are used to cover different areas in order to provide radio coverage over a wider area than the area of one cell • Example • Mobile telephony networks (GPS, UMTS)
Cellular networks • Abbreviations (1) • SIM – Subscriber Identity Module • MS – Mobile Station • USIM – Universal Subscriber Identity Module • ME – Mobile Equipment • TE – Terminal Equipment • UE – User Equipment • BTS – Base Transceiver Station • BSC – Base Station Controller
Cellular networks • Abbreviations (2) • Node B – Analogue to BTS in UMTS • RNC – Radio Network Controller • BSS – Base Station Subsystem • RNS – Radio Network Subsystem • MSC – Mobile Switching Center • GMSC – Gateway MSC • SGSN – Serving GPRS Support Node • GGSN – Gateway GPRS Support Node
Cellular networks • Abbreviations (3) • VLR – Visitor Location Register • HLR – Home Location Register • EIR – Equipment Identity Register • AuC – Authentication Center • PSTN – Public Switched Telephone Network • PLMN – Public Land Mobile Network
Wireless mesh networks • Mesh network • Data communication through fixed nodes • The connectivity allows continued communication even if some of the nodes in the network stop functioning • Wireless mesh network • Communication between the nodes is wireless • Similar to mobile ad hoc networks, but the nodes are in general not mobile.
Mobile ad hoc networks (MANETs) • A self-configuring network of mobile routers (and associated hosts) connected by wireless links • Together, they form an arbitrary topology • The routers are free to move randomly and organize themselves arbitrarily
Mobile ad hoc networks (MANETs) • The network's wireless topology may change rapidly and unpredictably • Such a network may operate in a standalone fashion, or may be connected to a larger Internet
Hybrid ad hoc networks • A structure-based network that is extended using multi-hop communications • The existence of a communication link between the mobile station and the base station is not required • A mobile station that has no direct connection with a base station can use other mobile stations as relays.
Vehicular networks (VANETs) • A form of MANET • Intended to provide communication among nearby vehicles and between vehicles and nearby fixed equipment (roadside equipment) • The main goal • providing safety and comfort for passengers
Vehicular networks (VANETs) • A special electronic device is placed inside each vehicle • Provides ad hoc network connectivity for the passengers • This network tends to operate without any infrastructure
Wireless sensor networks • Spatially distributed autonomous devices • Use sensors to cooperatively monitor physical or environmental conditions (temperature, sound, vibration, pressure, motion, pollutants, etc.) at different locations. • In addition to one or more sensors, each node in a sensor network is equipped with a radio transceiver, a small microcontroller, and an energy source, usually a battery.
Integrated networks • Modern networks often integrate many types of networks, including various types of wireless networks • Example • Sensor networks and ad hoc networks are often integrated to make a single network
Classification according to range • According to the range, wireless networks are classified in the following way • Short-range • Bluetooth, ZigBee • Medium-range • WLAN • Medium long-range • Cellular • Long-range • Satellite global area networks