BIOMETRICS
BIOMETRICS. Presented By Rickie Jackson. Outline Introduction Biometrics techniques Strengths, and weaknesses FAR/FRR Major Players Summary. What Is Biometrics. Biometrics is the reading of a unique human physical attribute as data, which is then applied to actuating a system. .

BIOMETRICS
E N D
Presentation Transcript
BIOMETRICS Presented By Rickie Jackson
Outline • Introduction • Biometrics techniques • Strengths, and weaknesses • FAR/FRR • Major Players • Summary
What Is Biometrics Biometrics is the reading of a unique human physical attribute as data, which is then applied to actuating a system. • Access control of Secure areas • Replacing passwords on computers or PDAs
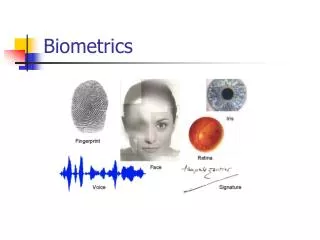
Biometrics Techniques • Retina scanning • Iris scanning • Fingerprint scanning • Hand scanning • Face recognition • Voice recognition & DSV • Signature recognition • Keystroke recognition
Retinal Scanning Iris Scanning User Looks Into a Viewer and Focuses on a Point; Infrared Light Scans Retina User looks at a camera (distance from camera increasing rapidly to 2-3 feet)
Finger Scanning User Places Finger on Scanning Device
Hand Scanning User Places Hand on Device
Facial Recognition User Looks at Camera
Other Techniques Voice Recognition & DSV User speaks into a microphone or other device, such as a telephone handset Signature Recognition User signs name on a device Keystroke Recognition User types standard sample on keyboard
Retina Iris Fingerprint Hand/Finger Geometry Face Recognition Voice Recognition Signature Recognition Keystroke Recognition Strengths, and Weakness
Technique Strengths Retina Highly accurate Iris Highly accurate; works with eyeglasses; more acceptable to users than retina scan Fingerprint Mature technology; highly accurate; low cost; small size, becoming widely acceptable Hand/Finger Geometry accurate and flexible; widely acceptable to users Face Recognition Widely acceptable to users; low cost; no direct contact; passive monitoring possible Voice Recognition Usable over existing telephone system; good for remote access and monitoring; Signature Recognition Widely acceptable to users Keystroke Recognition Widely acceptable to users; low cost; uses existing hardware
Technique Weaknesses Retina Inconvenient for persons with eyeglasses; dislike contact with device and light beam Iris New technology, cost, although this is rapidly changing Fingerprint Users can create high FRR; some persons dislike contact with device Hand/Finger Geometry User interface is bulky; dislike contact with device Face Recognition Face recognition is less accurate than other methods Voice Recognition Less accuracy; subject to background noise Signature Recognition Less accuracy; not widely used yet, but has potential with PDAs Keystroke Recognition Less accuracy;
FAR & FRR FAR(False Acceptance rate) – refers to how often the system accepts someone it should reject AND FRR(False Rejection Rate) is how often the system rejects someone it shouldn’t.
Relation of FAR and FRR FAR Accept wrong person FRR Reject the correct person Security Level Low High
Major Players • Computer access • Physical access • Handheld devices • Military/Govt. Agencies/DOD • Financial services • Hospitals • Telecommunication
Summary • As biometric technology advances, the cost of systems will decrease. • At the same time, biometrics systems will become increasingly sophisticated and accurate. • Scientist will physical and behavioral traits will increase the usefulness of biometrics. • The general public will gradually come to accept biometric system.
References Fuller, Scott and Pagan, Kevin 1997. Intranet Firewalls “Planning and Implementing Your Network Security System.” Ventana Communications Group, Inc. Conry-Murray, Andrew. Network Magazine. Oct. 1, 2002. p28 Securing End Users from Attack. McCollum, T. Security concerns prompt new initiatives. The Internal Auditor. Oct. 2002. Short, Bob. September 2002. Getting the 411 on Biometrics. Security Magazine. p48. Tocci, Salvatore. 2000. High-Tech IDs: From Finger Scans To Voice Patterns. Grolier Publishing Mitnick, Kevin & Simon, William L. The Art of Deception: Controlling the Human Element of Security. Library Journal.