TIMELINE
350 likes | 691 Views
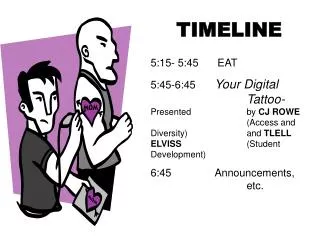
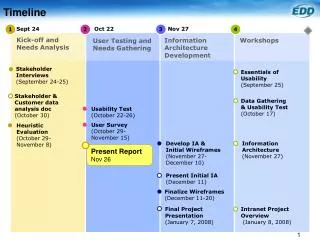
TIMELINE. 5:15- 5:45 EAT 5:45-6:45 Your Digital Tattoo- Presented by CJ ROWE (Access and Diversity) and TLELL ELVISS (Student Development) 6:45 Announcements, etc. your digital tattoo. Peer Program Presentation November 7 th , 2007. Before we begin…. Some caveats…

TIMELINE
E N D
Presentation Transcript
TIMELINE 5:15- 5:45 EAT 5:45-6:45 Your Digital Tattoo-Presented by CJ ROWE (Access and Diversity) and TLELL ELVISS (Student Development) 6:45 Announcements, etc.
your digital tattoo Peer Program Presentation November 7th, 2007
Before we begin… Some caveats… • Your style will be different – explore the content and find a way that is your own. • Your WHAT and HOW change based on your audience. • Like every activity, you must determine your objectives before you can choose the right content and method.
Tonight’s Objectives • To provide an opportunity to think about the concept, a digital tattoo, the WHAT. • To allow time for planning HOW you would deliver this type of content. • To explore your own biases, abilities, and understandings to strengthen your presentation skills. • To practice presenting some of the ideas.
Session Overview • Digging up your digital dirt • What is a digital tattoo? • Web 2.0 • Why we ♥ Web 2.0 • Why we don’t ♥ Web 2.0 • Being authentic and being safe • Case in point • Resources
A volunteer… Who is confident (or perhaps just curious) about their own digital dirt and would be willing to share? Let’s….google!
Why this first activity? • What was important about starting with an activity? • What other activities might you use? • What are some of the risks involved with this? How can you “control” those risks?
Web 2.0 What is Web 2.0? Any guesses? A short summary: http://leap.ubc.ca/get_teched_up/
Web 2.0 • Social Networking (ie. Friendster, myspace, Livejournal,facebook) • Second Life • Wikis(pedia) • RSS feeds • Blogs • Podcasts • Rate Your Professor
facebook by numbers… • In July 2006 facebook had 7.5 million users. By February 2007, the number of registered users exceeded 17 million. It now has over 40 million active users – with a minimum of 1-2 million users online at any time • 3% user growth each week – 200 000 plus new users per day • 6th most popular site in US, number 1 in Canada, 1% of all internet time spent there • Growth over last year: 18-24 y/o 38%, 12-17 y/o 149%, 25-34 y/o 181%, 35+ 98% • facebook is now in the dictionary – as both a noun and a verb • UBC: 30 000 members (students, faculty, staff, alumni) + more outside network
facebook in recent news… • Google has partnered with facebook to allow non-users to search for profiles not designated private without being signed up. http://chronicle.com/wiredcampus/index.php?id=2387 • facebook has increased the number of “applications” available but users often don’t realize they need to update their privacy settings every time they add a new app. • facebook has also announced that they are going to begin allowing professional networking through their site. http://money.cnn.com/2007/10/02/magazines/fortune/facelinkedin.fortune/index.htm?postversion=2007100210 • Microsoft recently agreed to a $240 million dollar equity investment into development of facebook and secured exclusive rights to third-party advertising via facebook. http://money.cnn.com/2007/10/24/magazines/fortune/fastforward_microsoft_facebook.fortune/index.htm
Why we ♥ Web 2.0… • Gives students a venue to meet each other and connect with people they might not normally have met. • Pulse – can tell you what is cool, popular, mainstream, or not mainstream. • Advertising events for students – VERY good response rates • Creating a forum for campus groups to interact and build a sense of team
Why we don’t ♥ Web 2.0… • Safety • TMI: Too Much Information • Cyber-stalking or identity theft • Dangerous behaviours endorsed • Used by folks outside the institution to screen or monitor student behaviour • The “digital tattoo” effect: What information do you want to have floating around about yourself 5 years from now…10 years from now…20 years from now? • Impact on job prospects. What does your site say about you?
Information dump • When is it good to provide information? • When do you need another strategy? • How else could you explore Web 2.0 and some of the facts associated with it?
Making the case… Often, one of the most influential and impactful ways of conveying information is through stories. Following are a few examples we have used to explore the digital tattoo idea through real stories. Consider: • what stories might you use? • why might you use them? • what important considerations would you make when sharing them? • what will you need to be careful of?
Cases… To keep in mind just how personal and yet very public the internet can be we came across these examples of cases where information shared on social networking sites or personal blogs that had big consequences.
Case in point… At a 2005 Pennsylvania State University vs. Ohio State football game, Penn U. students stormed the field after their victory, causing a riot. Police officers scanned Facebook and accessed a student group titled “I rushed the field after the OSU game (and I lived!)” to analyze photos and identify approximately 50 students involved (Read, 2006). http://youtube.com/watch?v=PtWMl0Bkbuc
Case in point… In China an intimate blog written by a 25-year-old who also wrote a magazine sex column attracted 10 million daily visitors to the Sina.com server. Her blog initiated a “raging debate” on the internet, and the Chinese censors banned her forthcoming book. Although she defended her right to write about her sex life, the blogger said that she never realized her blog would be read so widely or that it would create such controversy. She quit her job at the magazine and has shut down her blog. (Yardley, 2003) http://query.nytimes.com/gst/fullpage.html?res=9B0CE7DA133AF933A05752C1A9659C8B63
Case in point… A blogger from Utah harshly criticized her Mormon upbringing, her job and co-workers online, assuming that her technophobic parents and her boss would never find out. But they did, and “All hell broke loose,” as she put it. She alienated her parents and lost her job. “It was shocking for everyone,” she said; “I was extremely naïve.” (St. John, 2003).
Case in point… Students at many universities can now use facebook as a tool to select their roommate. Students are encouraged to login, explore profiles and find someone they would like to live with in residence. http://www.insidehighered.com/news/2007/08/24/roommate
Other cases? Consider: • What other cases have you encountered that would be useful to add here? • Why is presenting some real stories important? • What will you need to be careful of?
Activity… Sort yourself into small groups of 4-5 and share: • What do you think are the biggest safety concerns for social networking sites. • What digital dirt “might” exist about you? • How can you balance being authentic and being safe?
Tip #1: Personal Information • Do not include anything personal: where you live, your phone number, address, or any other identifying information. • Just because there is a field for certain information, does not mean you have to fill it in. • If you need to post any personal information on a website, make sure you read through (or at least know somewhat) about the Privacy Statement on the website. • If you find that a website lacks a Privacy contract/statement/etc., the website is probably not trustworthy enough to post any personal information on.
Tip #2: Identifying Others • Remember that posting information about your friends could put them at risk. Seek permission from your friends before posting any of their personal information. If a friend asks you to take information down do it. • Do not include or discuss your professor or TA's name, your employer's name, the name of the community you work, your company's clients, etc.
Tip #3: Photos • Do not post any photos of you participating in illegal activity, and/or acting irresponsibly, or that others might find offensive. (i.e underage drinking could put you at risk for legal consequences) • Employers may look up potential candidates on-line before making hiring decisions.
Tip #4: Selling your soul • Social Networks and other sites may sell personal information about people who use their service. Therefore your profile can be viewed by others without your knowledge. • Websites may have privacy policies but that does not prevent people with access (other members of Facebook for example) from redistributing your information elsewhere on the internet.
Tip #5: Stalking • Your personal information can be used for the purposes of stalking and/or identity theft. • Limit access to your profile, only add people as friends to your site if you know them in real life. • Avoid posting any plans or activities on your site. Making this information available could make you susceptible to would be stalkers.
Tip #6: Internet Archives • Information you post can follow you around for years to come. Even if you remove certain information, someone may already have copies or may have distributed that information on the internet. • The wayback machine: http://www.archive.org/web/web.php
Tip #7: Meeting online • If you plan to meet someone that you have met online, meet this person in a busy area (ex: coffee shop). Tell someone where you are going and when you expect to return. Have a friend call you on your cell phone to check in with you.
Tip #8: Reporting harrassment • Electronic communication that is unwanted, and that is persistent, repeated, obscene or otherwise unwelcome may be harassment, and action may be taken under University policy. If you are concerned about your personal safety and/or would like more information contact the University of British Columbia’s Campus Security Office. • If the comments are threatening in nature, you can contact Campus police and/or the RCMP for assistance.
Questions to ask… Before you post information online ask yourself… • Would I still post it if it was on a public bulletin board on campus? • If it were published in the paper? • If someone passed the info or photo on to my parents? • If I knew a potential employer might see it?, my professors?, Campus Police? • Would I engage an unknown person in conversation if we were two strangers sitting on the bus together?
Resources LEAP • http://leap.ubc.ca/get_together/online_communities/digital_tattoo/ Using facebook while maintaing privacy • http://engtech.wordpress.com/2007/03/08/how-to-use-facebook-without-losing-your-job-over-it/ Dealing with your Digital Dirt • http://www.abilitiesenhanced.com/digital-dirt.pdf BC Rural Women’s Online Safety Toolkit • http://www.onlinesafetytoolkit.com/
Resources cont. Stalking meets the Internet • http://womynsvoices.ca/en/node/124 Digital Voyeurism: A New Age for Peeping Toms • http://womynsvoices.ca/en/node/479 “Cultivating Violence Through Technology? Exploring the Connections between Internet Communication Technologies (ICT) and Violence Against Women (VAW) • http://www.genderit.org/upload/ad6d215b74e2a8613f0cf5416c9f3865/VAW_ICT_V1_MARCH2005.pdf University of Wisconsin: Living in Online Communities: A User’s Guide • http://www.uwec.edu/sdd/onlinesafety.htm
Questions??? • What else is important to consider in facilitating this type of workshop? • Does this all make sense? • Did we miss anything?
Thanks! We are not experts…but feel free to contact us if you have any questions CJ Rowe Access and Diversity 604-822-2415 cj.rowe@ubc.ca Tlell Elviss Student Development 604-822-9196 tlell.elviss@ubc.ca