Sensor Network Security
Sensor Network Security. Presenter Ahmed Galib Reza. Introduction. Why wireless sensor networks (WSN)? Wireless sensor networks consist of a large number of such sensor nodes and are able to collect and disseminate data in areas.

Sensor Network Security
E N D
Presentation Transcript
Sensor Network Security Presenter Ahmed Galib Reza
Introduction • Why wireless sensor networks (WSN)? • Wireless sensor networks consist of a large number of such sensor nodes and are able to collect and disseminate data in areas. • Sensor’s low cost has made wireless sensor network cost effective. • Ordinary networks are unsuitable for environmental and/or strategic reasons [1]. • Three different types of nodes used in WSN: Crossbow’s MICA2 [2], CSIRO’s FLECK [3] and Crossbow’s Imote [2].
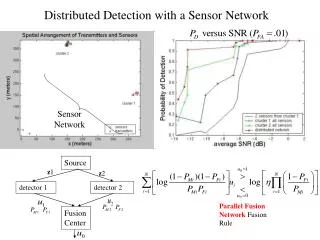
Introduction (Contd.) Fig. 1: A typical wireless sensor network (WSN)
Applications of WSN • Smart houses • Smart farms • Smart parking • Smart hospitals • Habitat monitoring • Building and structure monitoring • Distributed robotics • Etc.
Obstacles to WSN • WSN shares the common problems of the conventional network along with its own problems [4]. • Very limited resources • Limited memory and Storage space : A typical sensor has a 16 bit 8 Mhz CPU with 10K RAM, 48K Program Memory and 1M flash storage. • Power limitation • Unreliable communication media • Unreliable Transfer : Packet-based routing of the sensor network is connectionless hence unreliable.
Obstacles to WSN (Contd.) • Conflicts: Even if the channel is reliable, the communication may still be unreliable due to broadcast nature of WSN. • Latency: Multi-hop routing, network congestion and node processing can lead to greater latency in the network. • Unattended Operation: • Exposure to Physical Attacks.
Obstacles to WSN (Contd.) • Managed Remotely: Hard to detect physical tampering. • No Central Management Point: Ideally a WSN should have no central management point. However, if the network is designed incorrectly it may lead to greater congestion.
Problems Identification • WSN are more vulnerable to security breaches than traditional network due to: • More physical access. • Memory and energy limitation. • Limitation of processing abilities. • low coverage. • Unreliable communication media. • Broadcasting nature.
Security Goals of WSN • Confidentiality [5] • Integrity • Authentication • Availability
Goals of Security Solutions of WSN • High computation • Low memory • Low storage • Limited energy
Findings in Present Research • Although considerable amount of researches have been done so far, yet solutions remain inadequate. Because: • If low energy and memory consumption is achieved it compromises on the level of security and vice versa.
Physical Layer • The physical layer deals with the transmission of media between sending and receiving nodes, and includes the rate at which data is sent, the signal strength, and the frequency types. • Jamming attacks are one of the common attacks on the physical layer. • Ideally a frequency hopping spread spectrum (FHSS) is used in sensor networks. • Wood et al. [6] propose a mapping protocol which builds a map of the jammed region to prioritize message delivery in the network in such a way as to overcome the jamming attacks.
Data Link Layer • The data link layer does the error detection and correction, and the encoding of data. • This link layer is vulnerable to jamming and DoS attacks. • TinySec [7] introduces link layer encryption which depends on a key management scheme. However, an attacker with better energy efficiency can still launch a successful attack. • Protocols like LMAC [8] have better anti-jamming properties which are viable countermeasure at this layer. • Wood and Stankovic [9] suggest a number of solutions for detecting link layer attacks, such as collision detection techniques, modifying the MAC code to limit the rate of requests and using smaller frames for each packet.
Network Layer • The network layer is responsible for routing of messages from node to node, node to cluster leader, cluster leader to cluster leader, cluster leaders to base station and vice versa. • Possible attacks at this layer are: Spoofing, altering information, selective forwarding, sinkhole attacks, Sybil attacks, worm-holes • Authors in Poovendram and Lazos [10] propose a solution of the problem addressed above based on graph theory. • Yih-Chun and Johnson [11] packet leashes which add additional information to the packet to restrict the maximum distance a packet can travel in a given amount of time are proposed.
Related Work • Jeffery et al. [12] proposes a light-weight security protocol that operates in the base station of sensor communication whereby the base station can detect and remove an aberrant node if it is compromised. This protocol does not specify any security measures in case of a passive attack on a node where an adversary is intercepting the communication. • Zhu et al. [13] present LEAP, a security mechanism using a key management scheme based on a set of four keys for each sensor node which for security purposes restricts the impact of nodes in the immediate neighborhood of the compromised node.
Related Work (Contd.) • Marti et al. [14] propose watchdog and path-rater tools to detect and mitigate routing behavior, whereby the watchdog detects a misbehaving node. However, weaknesses such as ambiguous collisions, limited transmission power, false misbehavior and collusions make this technique less effective. • A security-enhanced version of AODV called Security-aware AODV (SAODV) is introduced by Yi et al. [15]. It is claimed that SAODV achieves a satisfactory performance-overhead trade-off. However, the fact that it is a metric-centric approach that relies on an user-defined, application-dependent parameter for evaluating trust levels, does not solve the fundamental security problem and leaves a lot of questions unanswered.
Reference [1] Akyildiz, I.F., Su, W., Sankarasubramaniam Y. and Cayirci, E. (2002) Wireless sensor networks: A survey. Computer Networks, 38 (4) March, pp. 393-422. [2] Crossbow Technologies Inc. (2004)Wireless sensor networks: getting started guide. [online] Available at http://www.xbow.com/Support/Support_pdf_files/MoteWorks_Getting_Started_Guide.pdf[Accessed 05 October 2009] [3] Corke, P., Sen, S., Sikka, P., Valencia, P. andWark, T. (2006) Wireless sensor and actuator networks. CSIRO, 2-year Progress Report: July 2004 – June 2006. [online] Available at http://www.csiro.gov.au/csiro/content/file/pfik.html [Accessed 05 October 2009] [4] Perrig, A., Szewczyk, R., Wen, V., Culler, D. and Tygar, J.D. (2002) SPINS: security protocols for sensor networks. In Wireless Networks Journal (WINE), September 2002. [5] Carman, D.W., Krus, P.S. and Matt, B.J. Constraints and approaches for distributed sensor network security. Technical Report 00-010. Glenwood, Maryland, USA, NAI Labs, Network Associates, 2000.
Reference [6] Wood, A., Stankovic, J. and Son, S.H. (2003) A jammed-area mapping service for sensor networks. In Proceedings of the Real-Time Systems Symposium, December 3-5, Cancun, Mexico. [7]Karlof, C., Shastry, N. and Wagner, D. (2004) Tinysec: a link layer security architecture for wireless sensor networks. In Proceedings of SenSys’04, November 3-5, 2004, Baltimore, Maryland, USA. [8] Hoesel, L.V. and Havinga, P. (2005) A lightweight medium access protocol (LMAC) for wireless sensor networks: reducing preamble transmissions and transceiver state switches. In Proceedings of INSS, June 27-28, 2005, San Diego, California, USA. [9]Wood A. and Stankovic, J. (2002) Denial of service in sensor networks. IEEE Computer, October, pp. 54-62. [10] Poovendran, R. and Lazos, L. (2005) A graph theoretic framework for preventing the wormhole attack in wireless ad hoc networks. ACM Journal on Wireless Networks.
Reference [11] Yih-Chun, H. and Johnson, D. (2006) Wormhole attacks in wireless networks. IEEE Journal on Selected Areas in Communications (JSAC) 24 (2), February. [13] Zhu, S., Setia, S. and Jajodia, S. (2003) LEAP: efficient security mechanisms for large-scale distributed sensor networks. In Proceedings of the ACM Conference on Computer and Communications Security (CCS '03), October 27-30 2003, Washington, DC. [14] Marti, S., Giuli, T. J., Lai, K. and Baker, M. (2000) Mitigating routing misbehavior in mobile ad hoc networks. In Proceedings of the 6th Annual International Conference on Mobile Computing and Networking (MobiCom 2000) August 6-11, 2000, Boston, USA. Boston, MA, ACM Press, pages 255-265. [15] Yi, S., Naldurg P. and Kravets R. (2001) Security aware ad hoc routing for wireless sensor networks. In Proceedings of the 2001 ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc ’01), October 4-5, Long Beach, California, USA ACM Press, pp. 299-302.