Introduction to the .NET Framework
Introduction to the .NET Framework. Richard Grimes richard@richardgrimes.com www.grimes.demon.co.uk. Richard Grimes. .NET contributer Dr Dobb’s Journal Visual C++ .NET columnist for Windows Developer Magazine C# Q&A column for C#Pro www.c-sharppro.com Contributor to MSDN Magazine

Introduction to the .NET Framework
E N D
Presentation Transcript
Introduction to the .NET Framework Richard Grimesrichard@richardgrimes.com www.grimes.demon.co.uk © 2004 Richard Grimes
Richard Grimes • .NET contributer Dr Dobb’s Journal • Visual C++ .NET columnist for Windows Developer Magazine • C# Q&A column for C#Pro • www.c-sharppro.com • Contributor to MSDN Magazine • Twice monthly .NET email newsletter • www.wd-mag.com/newsletters © 2004 Richard Grimes
Richard Grimes • Developing Application with Visual Studio.NET, Addison Wesley, 2002 • Programming with Managed Extensions for Microsoft Visual C++ .NET, Microsoft Press, 2003 © 2004 Richard Grimes
Aims For The Day • Gain an understanding of the .NET architecture • Understand the basic features and facilities of .NET • Gain an overview of the .NET framework library © 2004 Richard Grimes
.NET Types and Objects • Everything in .NET is an object • reference types • value types (including enums) • ‘boxed’ value types • Reference types are created on the managed heap • Value types are created on the managed stack © 2004 Richard Grimes
.NET Types Object Reference Types Value Types Interfaces Delegates Exceptions Attributes Enums © 2004 Richard Grimes
.NET Types and Objects • Reference types have System.Object as the highest base class • must be created on heap with new • Value types have System.ValueType as base class, Enums have System.Enum as bass class • must be created on stack or embedded as a member of a reference type © 2004 Richard Grimes
Memory Layout • You should not care because data is accessed through members, not pointers • For interop with native code you can use a value type as a .NET representation of native structures • can specify the memory layout in this case © 2004 Richard Grimes
Exceptions • Standard mechanism to handle ‘exceptional’ situations • Code can be ‘guarded’ • clause to catch exception from guarded code • clause that is run when guarded block is left for any reason • Uncaught exceptions are passed up the call stack © 2004 Richard Grimes
Exception Handlers • Can catch all exceptions or specific exceptions • Can provide exception handlers for many different exception types • handler handles exception and the exception types derived from it © 2004 Richard Grimes
Type Members • Reference and Value types have • methods, fields, properties • Interfaces • have only methods and properties • All types can have events • metadata for delegate fields and a standard protocol to initialise them © 2004 Richard Grimes
Methods • Can be overloaded on parameter • methods with the same name differ by the parameters that they • cannot have default values for parameters • By default parameters are ‘by value’ • value passed on the stack, if you pass a reference type the reference is passed ‘by value’ not the object • can user modifier to pass by reference © 2004 Richard Grimes
Fields • Data members • read and write access • Can define const fields • C# can define readonly fields © 2004 Richard Grimes
Properties • Metadata that identifies methods to be used for read/write access • can implement either or both • Can add extra logic in property method • and can calculate values • Can implement Indexers • ‘indexed’ collection © 2004 Richard Grimes
Constructors • Constructor is called when an object is created • can overload constructors • ‘Destructor’ is called when object is finalized • you do not determine when this happens © 2004 Richard Grimes
Virtual Members • When a member is marked as virtual the runtime uses the object type to determine what method to call • Used in polymorphism • allows you to pass a derived object through a base class parameter and the ‘right’ method will be called © 2004 Richard Grimes
Static and Instance • Static members are not members of any particular instance • static fields are available to all instances • values of instance fields are specific to the instance • Static methods are executed in the context where they are called • instance methods are executed in the context where the object was created © 2004 Richard Grimes
Inheritance • .NET only supports single type inheritance • only reference types, value types are ‘sealed’ • .NET supports multiple interface implementation • and interfaces can have multiple ‘inheritance’ • Can derive from classes written in any language © 2004 Richard Grimes
Access Modifiers • Define whether the type is visible outside of the assembly • Define access to a member from • types within the same assembly • types in another assembly Assembly Assembly public class public class internal class internal class
Access Modifiers - Members Access From .NET Modifier C# Modifier External Internal public public Any class Any class famorassem protected internal Only derived Any class assem internal None Any class family protected Only derived Only derived famandassem None Only derived private private None This class © 2004 Richard Grimes
Managed Heap • Heap is managed by the garbage collector • cheap to allocate, expensive to compact • The GC will periodically remove old objects and compact the heap • objects that are not ‘reachable’ will be removed © 2004 Richard Grimes
Finalization • Objects are removed when the GC works, no sooner • ‘Finalizers’ perform clean up work • called when object is removed from heap • can be a long time after the object was last used • Use Dispose pattern instead • clean up code called explicitly by your code © 2004 Richard Grimes
Interfaces • Are ‘reference’ types • but always refers to an object • Object can force caller to call interface through interface reference, or allow call through object reference • Interfaces do not contain • storage, constructors, static members, method implementations © 2004 Richard Grimes
CLS • Common Language Specification defines rules that allow code written by one language to be used by code written by another language • not all code is CLS Compliant © 2004 Richard Grimes
Assemblies • Types are contained in assemblies • libraries, DLLs, can be shared between processes • EXEs are processes • Typically libraries do not run ‘on their own’ • but ASP.NET applications are libraries because .NET provides a host process © 2004 Richard Grimes
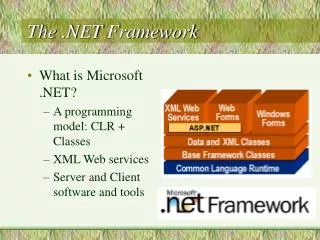
Executing Code • All code is compiled to Intermediate Language • .NET runtime will just-in-time compile this to native machine code at runtime • on a per method basis, the compiled code is cached in memory • Can pre-JIT the code © 2004 Richard Grimes
Assembly Loader Validation Verification Permissions Architecture - Loading Assembly Resolver .NET Runtime JIT Compiler Compiled Code Libraries .NET Framework Libraries © 2004 Richard Grimes
Accessing Non .NET Code .NET Process Native Library Platform Invoke COM Interop Native Library WebServices Native Process .NET Library COM Interop .NET Hosting .NET Library © 2004 Richard Grimes
Thread Thread .NET Remoting .NET Remoting Thread Architecture - Execution Process Application Domain Application Domain Process Application Domain © 2004 Richard Grimes
Basic Objects • Primitive Types • Collections • Arrays • Strings © 2004 Richard Grimes
Primitive Types • Part of the framework library • Used by all languages • the CLS primitive types, that is • Encapsulates operations on those types • conversions to other types • comparisons with other instances © 2004 Richard Grimes
Primitive Types CLS Types Non-Compliant Types Framework Type C# Type Framework Type C# Type Boolean bool Byte byte Char char UInt16 ushort SByte sbyte UInt32 uint Int16 short UInt64 ulong Int32 int Int64 long Single float Double double Decimal decimal String string © 2004 Richard Grimes
Collections • Defines standard collection classes and interfaces • ICollection, has count and synchronised access • IComparer, compare items in a sorted collection • IDictionary, access to a key-value collection • IList, items are accessed by index • IEnumerable, exposes an enumerator that iterates over the collection © 2004 Richard Grimes
Arrays • Single and multiple dimensions • Typed, index is zero-based • Size specified at declaration • Access given by index and via an enumerator • implements IEnumerable, IList, ICollection • All access is bounds checked © 2004 Richard Grimes
Strings • Contains an array of Char (Unicode) • Encapsulates all string operations • copy, replace, insert, remove, trim, sub string, uppercase, lowercase, compare, format, split, index of, last index of, pad left and right • Immutable • Interned • two string objects may be the same string, the string is interned © 2004 Richard Grimes
Metadata • Metadata describes types • all types have metadata • can extend metadata with ‘custom’ metadata • Runtime can read custom metadata as ‘out of band’ information © 2004 Richard Grimes
Metadata • The combination of metadata and IL means that anyone can ‘read’ your algorithm • can alleviate this with obfuscation • only solution is DRM with Longhorn © 2004 Richard Grimes
Attributes • Changes the metadata on a type • some add runtime metadata (eg [Serializable] • some add new metadata that is known by the runtime (eg [STAThread]) • some add metadata that is not known by the runtime, but known by other classes and code (eg [Conditional]) © 2004 Richard Grimes
Metadata APIs • The Reflection namespace allows you to read metadata at runtime • allows you to dynamically invoke methods and properties, and access fields • and can read attributes • The Reflection Emit API allows you to write metadata at runtime • create metadata and IL © 2004 Richard Grimes
Assemblies • Unit of deployment and security • defines the boundary of security and of type definition • Can contain multiple modules • each module is written in a single language • assembly can consist of modules written in many different languages • can also have other resource files © 2004 Richard Grimes
.NET Containers Assembly Module External Resources myfile.exe myPic.jpg Internal Resources myStrings.txt Configuration File myfile.exe.config © 2004 Richard Grimes
Assembly Names • Assembly name contains four parts • PE file name • version • culture • public key/public key token • EXEs don’t use culture other than neutral © 2004 Richard Grimes
Assembly Names • Assembly name uniquely identifies a library • Usually processes are ‘statically’ linked to libraries • library name is stored in the manifest of the files that use it • process will not load if the specific assembly cannot be found © 2004 Richard Grimes
EXEs and Libraries process.exe Manifest libOne, version=1.0.0.1, culture=neutral, publicKeyToken=null libTwo, version=1.2.0.1, culture=neutral, publicKeyToken=null libTwo.dll version=1.2.0.1, culture=neutral, publicKeyToken=null libOne.dll version=1.0.0.1, culture=neutral, publicKeyToken=null © 2004 Richard Grimes
Assembly Location • In most cases the libraries will be in the same folder as the process • can be in a folder with the name of the PE file • if the file has culture specific resources, then it’ll be in a folder with the culture name • Can be shared by putting it in the Global Assembly Cache © 2004 Richard Grimes
GAC • Appears to contain multiple files with the same name but different version • actually implemented with multiple folders • Contains assemblies • shared by other assemblies • ‘publisher policy files’, used to alter the versioning policy © 2004 Richard Grimes
Satellite Assemblies • Resource-only • Culture specific • Runtime ResourceManager class will load the assembly for the current thread culture • or fallback, ultimately to ‘neutral’ resources © 2004 Richard Grimes
Security • The most important part of .NET! • All arrays and string access is bounds checked • Stack is managed by .NET, so cannot overwrite return address • Code access security checks whether the code has the permissions to run © 2004 Richard Grimes
Signing Assemblies • Use the publisher public/private key • hash is created from assembly, encrypted with private key and appended to the assembly • public key is added to assembly • Assembly user can decrypt the signed hash, create its own hash from the assembly and compare the two © 2004 Richard Grimes
Assembly Validation • Check that the PE file is valid • ‘everything is where it should be’, eg entry point, resources, dependencies • Check that the metadata is valid • that the tables are valid • Check that the IL is valid • check that it is ‘correct’ IL • check that jumps are within a method © 2004 Richard Grimes