Exploring Customer Needs with APT Attack Stages
This slide deck provides an in-depth exploration of Advanced Persistent Threat (APT) attack stages, guiding customers through the common tactics employed by attackers. It discusses the challenges organizations face at each stage—from intelligence gathering to data exfiltration—and identifies areas where customers may be most vulnerable. The presentation encourages dialogue on potential solutions, not limited to products, and emphasizes the importance of understanding these threats to bolster defenses effectively. For usage inquiries, contact Richard Sheng at richard_sheng@trendmicro.com.

Exploring Customer Needs with APT Attack Stages
E N D
Presentation Transcript
Exploring Customer Needs with APT Attack Stages Last update - Feb. 26, 2012
How to use these slides • Share with customer on the common attack stages of APT. • Walk them thru the tactics in each stage and the new challenges faced. • Explore where customer feels the most pain or is weakest. • Discuss the solutions (non-products) , technologies, process change needed to deal with those challenges. If you have questions about how to use this deck, please contact Richard Sheng: richard_sheng@trendmicro.com or +886 928 756 411
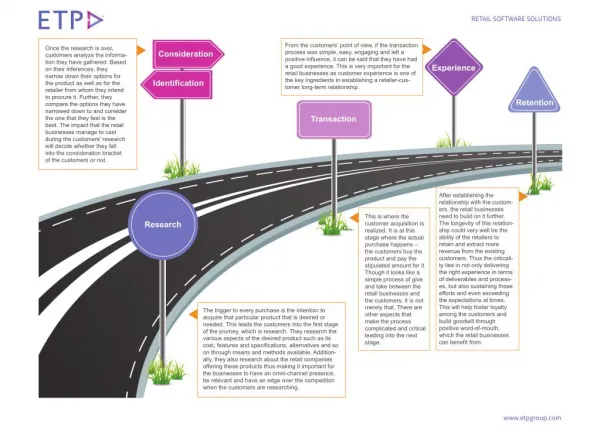
A Typical Targeted Attack and APT Profile 1. Intelligence Gathering Identify & research target individuals using public sources (LinkedIn, Facebook, etc) and prepare a customized attack. 2. Point of Entry The initial compromise is typically from zero-day malware delivered via social engineering (email/IM or drive by download). A backdoor is created and the network can now be infiltrated. (Alternatively, a web site exploitation or direct network hack may be employed.) 3. Command & Control (C&C) Communication Allows the attacker to instruct and control the compromised machines and malware used for all subsequent phases. 4. Lateral Movement Once inside the network, attacker compromises additional machines to harvest credentials, escalate privilege levels and maintain persistent control. 5. Asset/Data Discovery Several techniques (ex. Port scanning) are used to identify the noteworthy servers and the services that house the data of interest. 6. Data Exfiltration Once sensitive information is gathered, the data is funneled to an internal staging server where it is chunked, compressed and often encrypted for transmission to external locations.
APT Attack Stages/Tactics 1 Point of Entry Reconnaissance/Targeting using Social Engineering. Usually penetrate via email/IM and exploit vulnerabilities to achieve an initial compromise 2 Command & Control (C&C) Allows the threat actors to instruct the compromised machines for lateral movement. It opens a continuous communication channel for threat actors which is essential in a targeted attack 3 Lateral Movement Once inside the network, threat actors seek additional compromised machines to maintain persistent control and harvest credentials for escalating their privilege levels 4 Asset/Data Discovery Several techniques (ex. Port scanning) are used to identify the noteworthy servers and the services they are running for locating the data of interest 5 Data Exfiltration Once sensitive information is gathered, the data is chunked, compressed and often encrypted for transmission to external locations under attacker’s control APT Problems by Stages Antivirus & FW ineffective - Malware customized - Open ports & protocols Human weakest link - Social engineering - Spear-phishing Are we under attack? - Limited visibility of infiltration attempts Edge Vulnerabilities - Web app vulnerabilities • Back-door Established • - Don’t know which hosts are compromised • Lack of C&C visibility • Command & control servers are dynamic • Encrypted Communications over HTTP/HTTPS • Can’t afford to block theses ports • Difficult to inspect high volume traffic Unpatched Hosts Most breaches involves known vulnerabilities that aren’t patched Privilege Escalation Harvest credentials for escalating their privilege levels Visibility of Log-in Failure Visibility Hackers will attempt to use harvested credential to traverse servers on the network. Overwhelmed with system events Once inside the network, threat actors seek additional machines Unpatched Hosts Known vulnerabilities aren’t patched Server Setting & Configuration changes Hackers will attempt to change server configurations. Data Exfiltration Once sensitive information is gathered, the data is chunked, compressed and often encrypted for transmission to external locations under attacker’s control APT Needs by Stages Check for signs of infiltration - Look for attachments that have been exploited, on the mail servers Analyze Exploits in Sandbox Environment - Determine C&C comm. & system impact. Vulnerability Assessment - Identify vulnerabilities on external facing services. • Identify C&C IP/Domain • By executing exploited documents in sandbox. • Monitor network traffic for C&C communications • Identify compromised hosts • Gain visibility of malware chatter • Update Gateway Security Policy • Disrupt future C&C communication attempts Vulnerability Shielding - Protect unpatched hosts, including legacy systems, and zero-day vulnerabilities System Integrity Monitoring - Define suspicious and anomalous system and log changes , and failed login. Restrict & Monitor User Access & Privilege Uses - Separate access privilege between help desk and datacenter. Log Management & Analysis - Develop process and tools to monitory logs & events. Vulnerability Assessment Several techniques (ex. Port scanning) are used to identify internal vulnerabilities. Integrity Monitoring - Define suspicious and anomalous system and log changes , and failed login. Data Leak Prevention Once sensitive information is gathered, the data is chunked, compressed and often Encryption encrypted for transmission to external locations under attacker’s control Incident Management - Create an incident response plan.
What’s Available Today APTs Mail Scanner or integrate with IMSS/SMEX Integrated DLP Dynamic Threat Analysis System (DTAS) - sandbox Endpoint Encryption NVW – Threat Blocking Threat Awareness Audit APT Needs by Stages TDA 2.58/2.6 – listen for C&C communication, identify infected hosts, detect worm activities. Check for signs of infiltration - Look for attachments that have been exploited, on the mail servers Analyze Exploits in Sandbox Environment - Determine C&C comm. & system impact. Vulnerability Assessment - Identify vulnerabilities on external facing services. • Identify C&C IP/Domain • By executing exploited documents in sandbox. • Monitor network traffic for C&C communications • Identify compromised hosts • Gain visibility of malware chatter • Update Gateway Security Policy • Disrupt future C&C communication attempts Vulnerability Shielding - Protect unpatched hosts, including legacy systems, and zero-day vulnerabilities System Integrity Monitoring - Define suspicious and anomalous system and log changes , and failed login. Restrict & Monitor User Access & Privilege Uses - Separate access privilege between help desk and datacenter. Log Management & Analysis - Develop process and tools to monitory logs & events. Vulnerability Assessment Several techniques (ex. Port scanning) are used to identify internal vulnerabilities. Integrity Monitoring - Define suspicious and anomalous system and log changes , and failed login. Data Leak Prevention Once sensitive information is gathered, the data is chunked, compressed and often Encryption encrypted for transmission to external locations under attacker’s control Incident Management - Create an incident response plan. Deep Security – Vulnerability Shielding | Log & System Integrity Monitoring OfficeScan IDF Plug-in - Vulnerability Shielding Coming Soon 2Q 2012 - APTs Assessment Services 2Q 2012 - Deep Discovery Family - Deep Discovery 3, Deep Discovery Playback, Deep Discovery Manager – ETA April. 2H 2012 - Deep Discovery 3.x - Infected Host Blocking (session termination/TCP reset) | Integrated DLP